Proton Mail's Legal Battle for Privacy: Challenging Australia's eSafety Regulator
Introduction Proton, the Switzerland-based encrypted email service, has taken a firm stand against the Australian online safety regulator's proposed s...
619 articles on data privacy, breach protection, and cybersecurity insights.

Introduction Proton, the Switzerland-based encrypted email service, has taken a firm stand against the Australian online safety regulator's proposed s...
Your Privacy Matters: Protect and Secure Your Digital Identity Join us in a journey to regain control of your digital privacy. Our expertly crafted gu...

Introduction: The rapid advancement of Artificial Intelligence (AI) has brought about significant benefits in various fields. However, it also present...
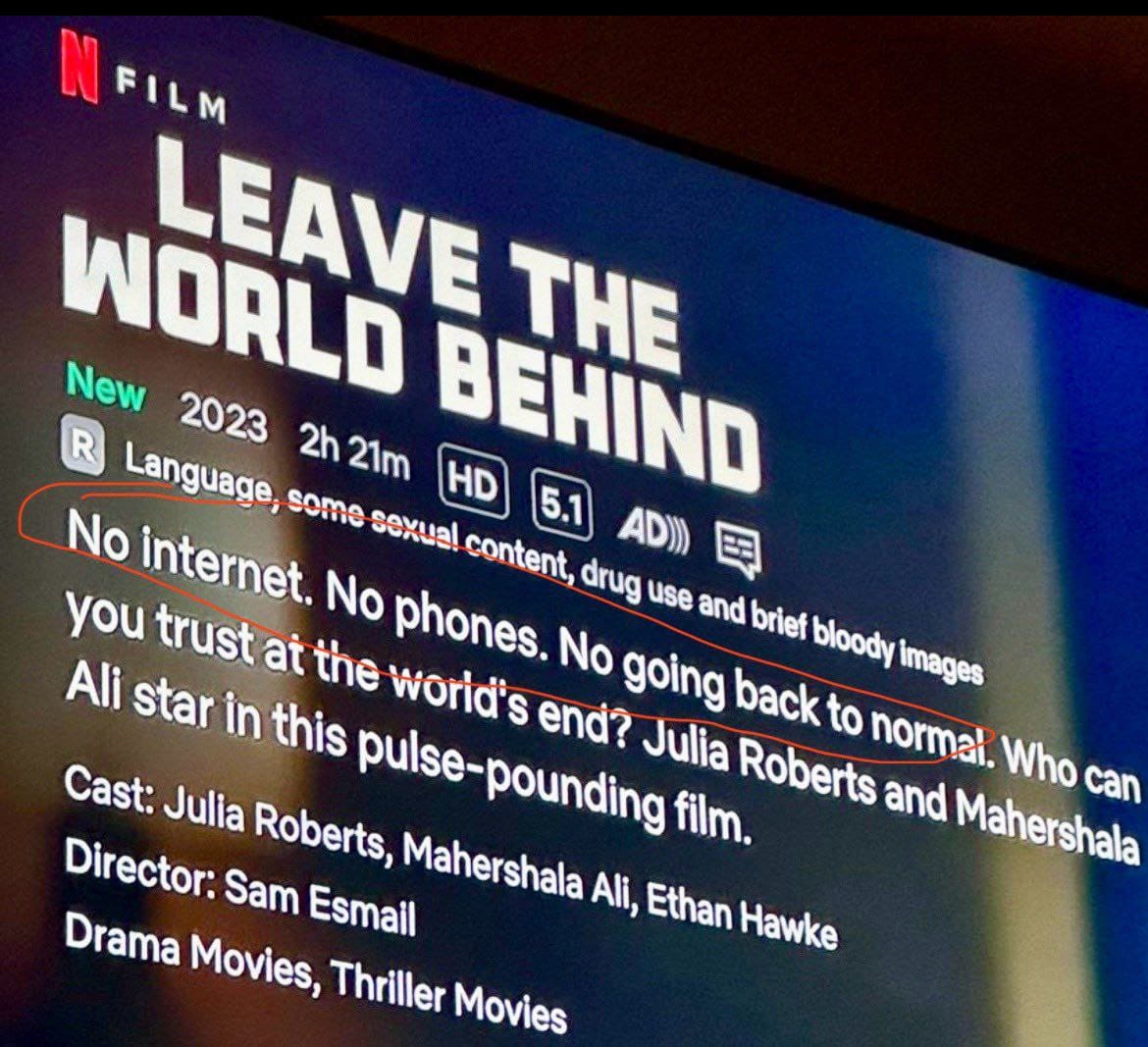
The new “Leave the World Behind” movie on Netflix, PRODUCED BY THE OBAMAS, is one of the most blatant examples of predictive programming combined with...

Section 702 of the Foreign Intelligence Surveillance Act (FISA) differs from other surveillance authorities in several key ways: Intersection of Secti...

Introduction In the complex arena of digital surveillance, companies like NSO Group and Cellebrite have gained notoriety for their powerful spyware to...

Introduction The confrontation between Apple Inc. and the Federal Bureau of Investigation (FBI) over unlocking an encrypted iPhone belonging to a San....

Introduction In an era where digital privacy is increasingly under threat, the use of sophisticated phone spyware by various nation-states has become ...

Introduction In a significant stride towards enhancing user privacy, Meta Platforms, Inc. has recently initiated the rollout of end-to-end encryption ...

Introduction In a significant legal action, the state of New Mexico has initiated a lawsuit against Meta Platforms, Inc., the parent company of Facebo...

Here's a synopsis of each game along with their hacking elements: The Evolution and Adoption of Hacking in Video Games Introduction Video games have l...

The intersection of Section 702, Net Neutrality, the Internet Bill of Rights, and the Patriot Act presents a complex landscape for digital privacy, se...