Protecting Privacy in E-Commerce: A Guide for Online Shoppers
Summary: Tips and strategies for maintaining your privacy and protecting your personal information while shopping online, from vetting vendors to secu...
581 articles on data privacy, breach protection, and cybersecurity insights.

Summary: Tips and strategies for maintaining your privacy and protecting your personal information while shopping online, from vetting vendors to secu...

Summary: Learn how to maximize your privacy on the most popular social media platforms. This guide explains how to adjust settings to protect your per...

Summary: Learn how to maximize your privacy on the most popular social media platforms. This guide explains how to adjust settings to protect your per...

Introduction The world of online dating can be an exciting way to meet new people and potentially find a romantic partner. However, it also comes with...

Summary: Online harassment and cyberstalking can have serious consequences for victims, making it essential to know how to protect yourself and your p...

Summary: With the rise of remote work, it's essential to understand the privacy risks associated with working from home. This article will discuss pot...
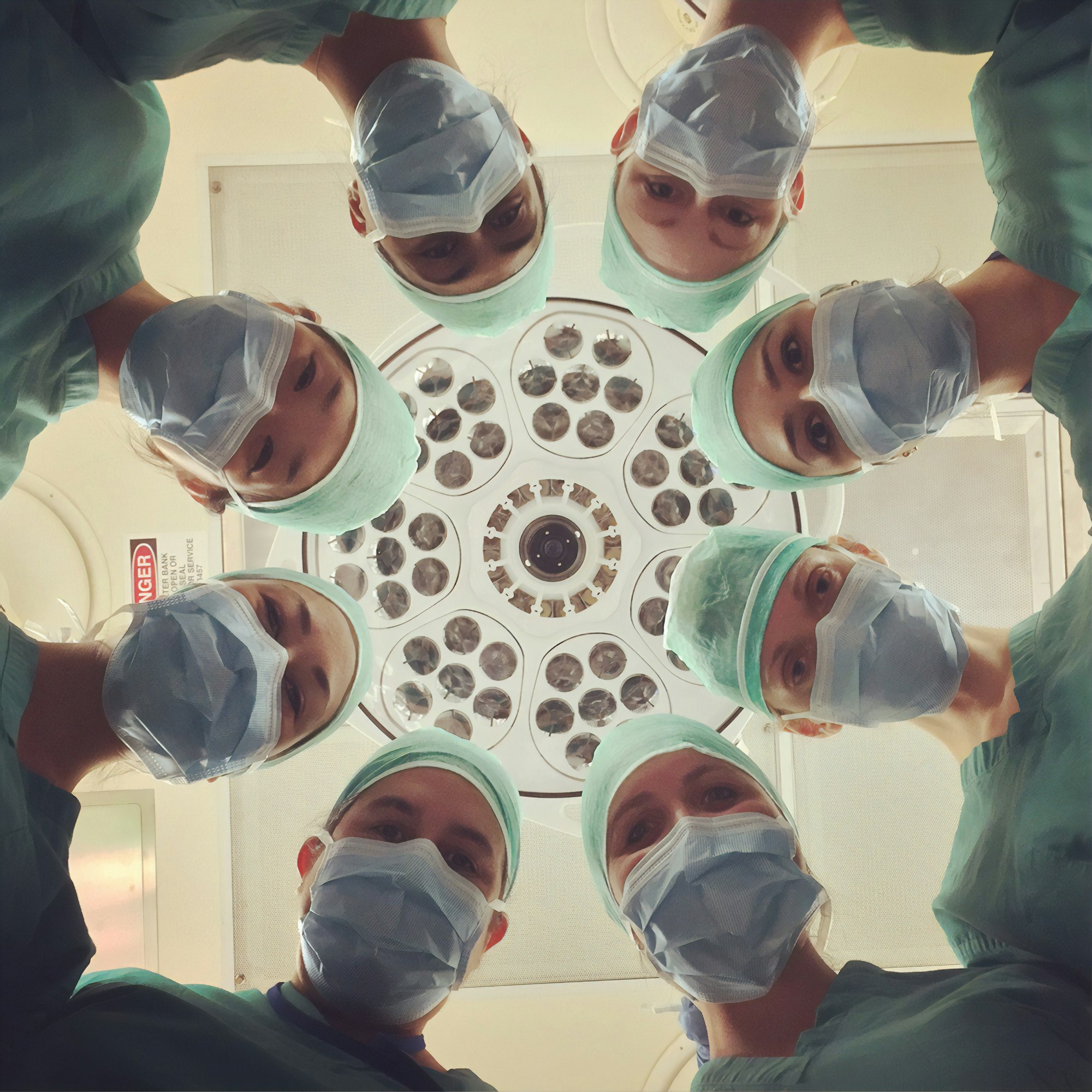
Summary: The healthcare industry is increasingly reliant on digital technology, making the protection of patient data a critical concern. This article...

Introduction COVID-19 has transformed the world in countless ways, including the rapid introduction and deployment of digital surveillance and trackin...

Summary: This article will focus on the importance of mobile app privacy and offer practical tips for choosing and using apps safely. Topics covered w...

Introduction In the digital age, intelligence agencies and international alliances play a crucial role in monitoring and analyzing internet communicat...

Summary: This article will provide a comparative overview of privacy laws and regulations in various countries and regions, including the European Uni...

Summary: This article will offer guidance on what to do in the event of a data breach or identity theft, including steps to take immediately after dis...