The Right to Be Forgotten: Understanding and Exercising Your Online Privacy Rights
Summary: The article will discuss the concept of the "right to be forgotten," focusing on the legal basis and implications of this privacy right. It w...
581 articles on data privacy, breach protection, and cybersecurity insights.

Summary: The article will discuss the concept of the "right to be forgotten," focusing on the legal basis and implications of this privacy right. It w...

Summary: This article will cover various tools and techniques for maintaining anonymity online, such as using Tor Browser, VPNs, proxy servers, and te...

Summary: The article will explore privacy-focused alternatives to popular apps and services, including search engines, email providers, messaging apps...
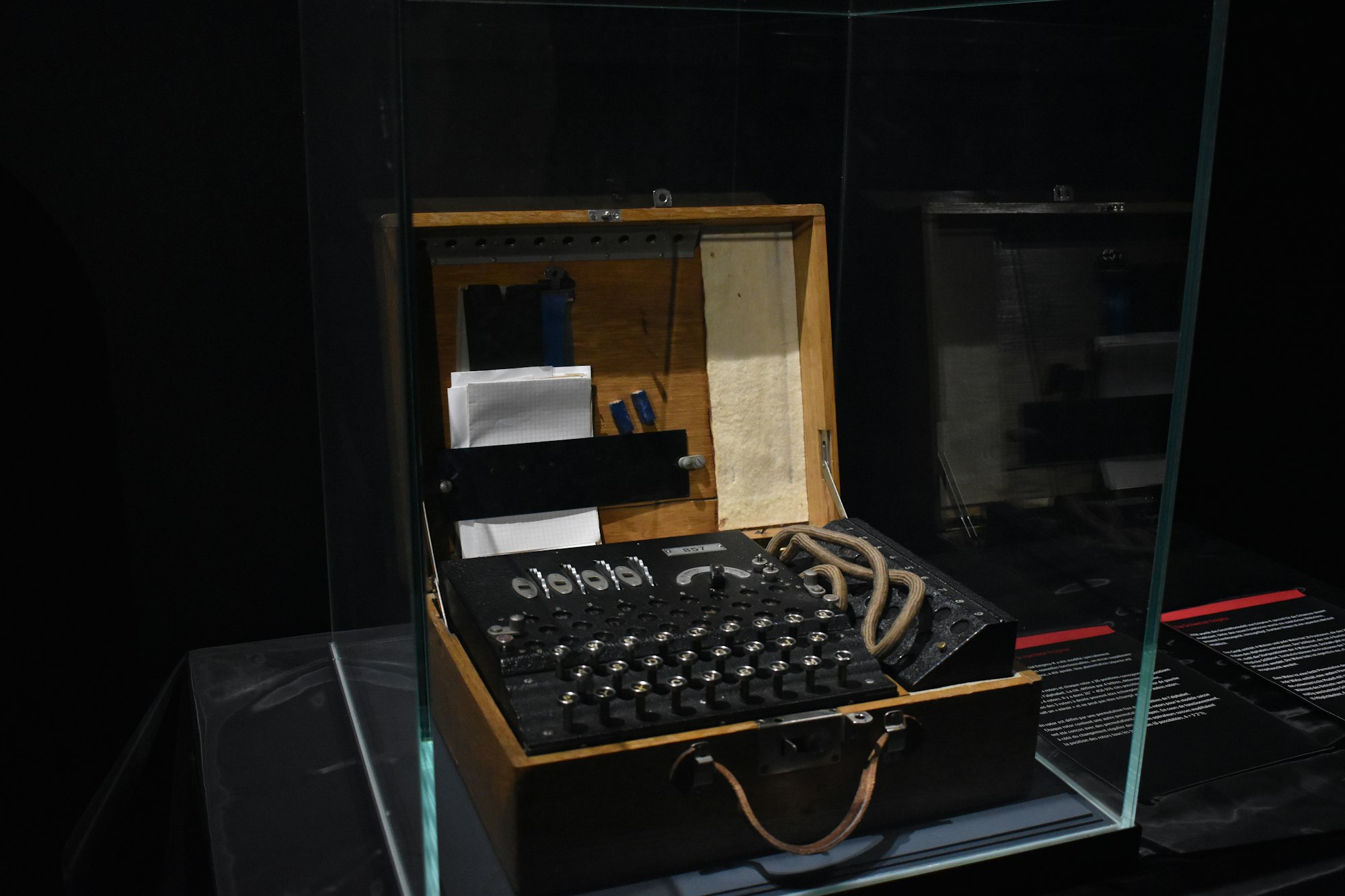
Summary: This article will provide an overview of encryption tools and techniques to help protect your digital life, including email encryption, end-t...

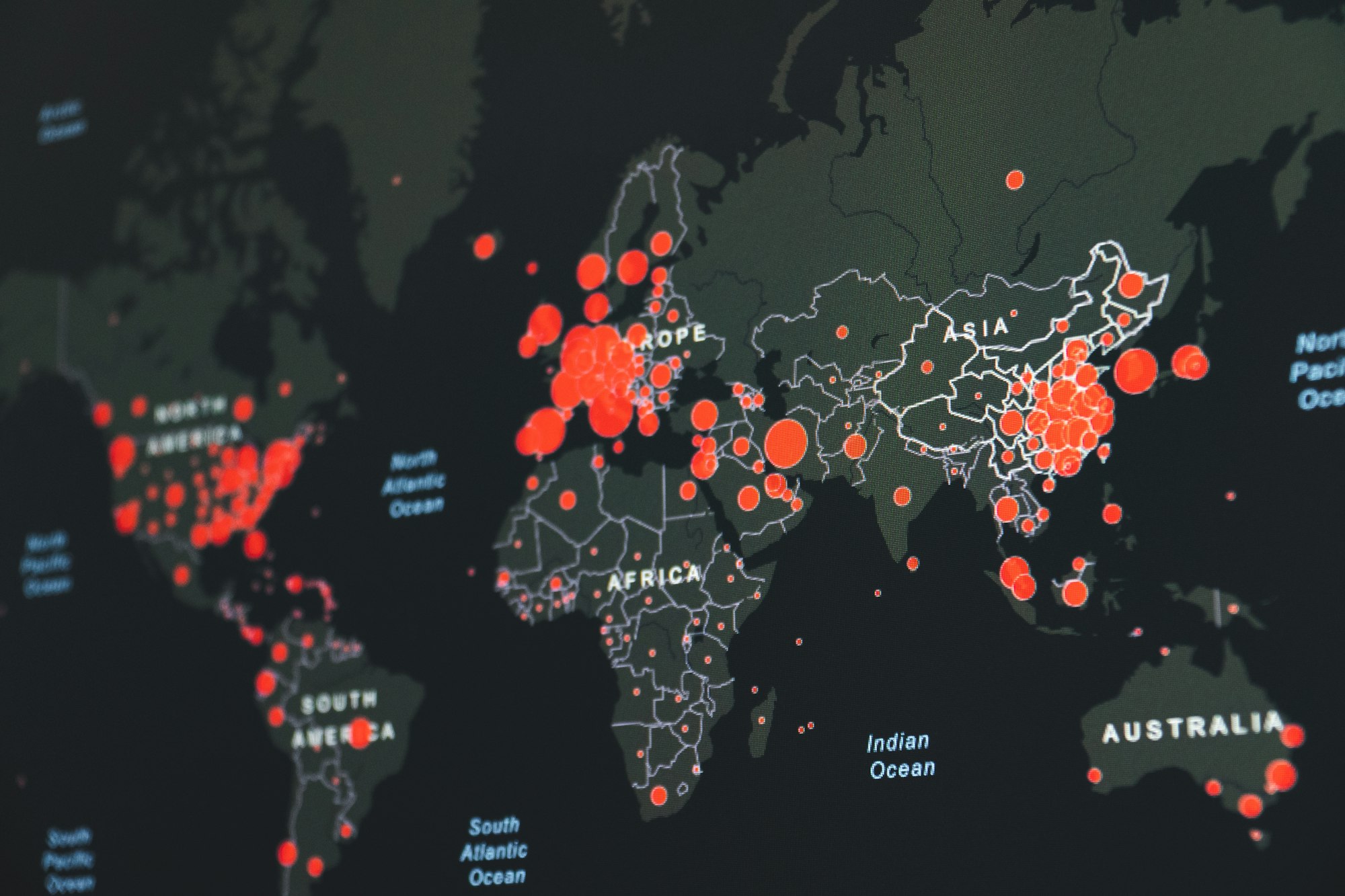
Summary: Our online activities leave behind a digital footprint that can reveal a lot about our personal lives and preferences. This article will disc...

Summary: This article will focus on the importance of protecting your financial information when conducting online banking and shopping. It will discu...

Summary: As children increasingly use digital devices and the internet, it's essential to equip them with the necessary digital literacy skills. This ...

Summary: With the increasing popularity of smart home devices, such as voice assistants, smart thermostats, and security cameras, this article will di...

Summary: This article will provide an overview of phishing attacks, which are attempts by cybercriminals to trick individuals into revealing sensitive...
There are several government resources available that can assist individuals in need of help regarding digital privacy, cybersecurity, and online safe...

Summary: The online world can be a dangerous place for children, with risks ranging from cyberbullying to online predators. This article will provide ...

Summary: Strong, unique passwords are essential for protecting online accounts, but managing them can be a challenge. This article will discuss the im...