As artificial intelligence becomes increasingly sophisticated, so do the threats that exploit these technologies. Today, we’re excited to announce the launch of our AI Security Defense Hub at ai.myprivacy.blog a comprehensive, free educational platform designed to help individuals and organizations understand and protect against the most critical AI-powered cybersecurity threats of our time.
The Reality of AI-Powered Threats in 2026
We’re living in an era where artificial intelligence can create convincing deepfakes in minutes, clone voices from a few seconds of audio, and generate sophisticated phishing campaigns tailored to individual victims. These aren’t distant future scenarios – they’re happening right now, and they’re targeting people just like you.
Recent statistics paint a sobering picture:
- Deepfake incidents have increased by over 900% in the past year- Voice cloning scams are costing Americans billions annually, particularly targeting elderly populations- AI-powered crypto scams have resulted in over $1 billion in losses in 2024 alone- Biometric spoofing attacks are becoming increasingly sophisticated and accessible
The traditional approach to cybersecurity education focusing on “don’t click suspicious links” is no longer sufficient. We need a new framework for understanding and defending against threats that leverage the same cutting-edge AI technologies we use in our daily lives.
Introducing the AI Security Defense Hub
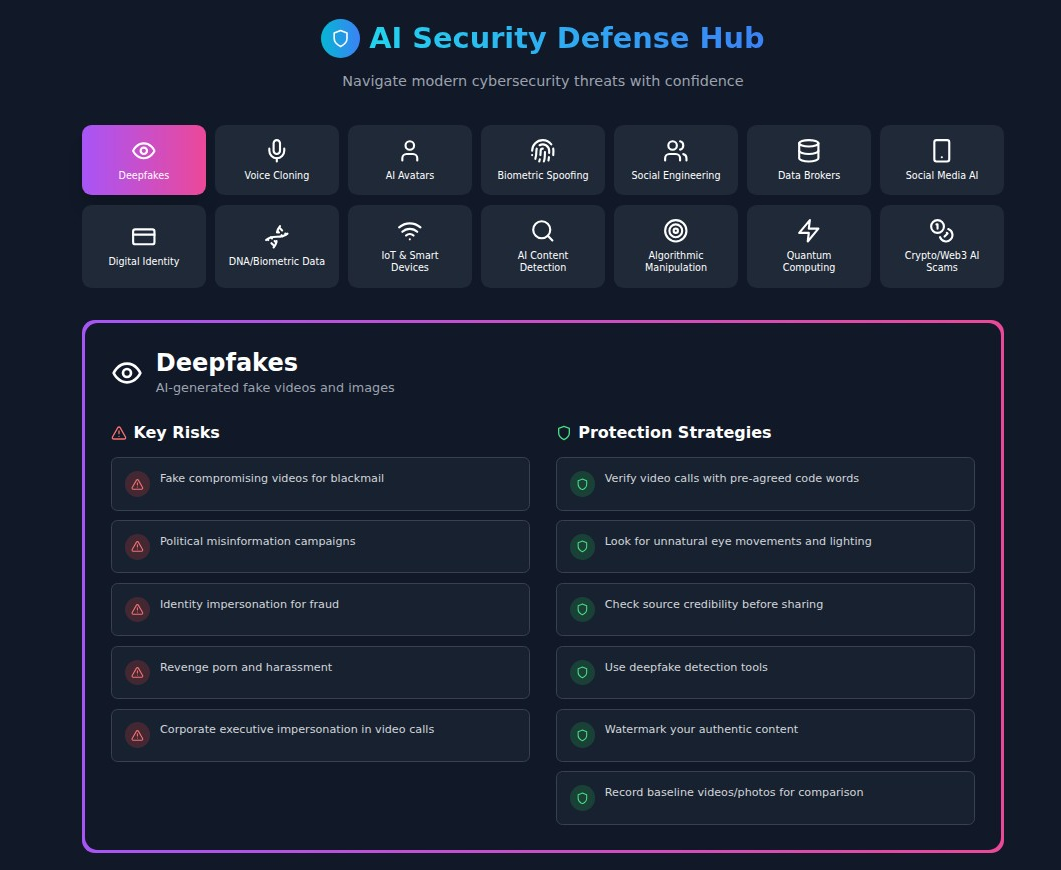
Our AI Security Defense Hub represents a paradigm shift in cybersecurity education. Rather than generic warnings, we provide specific, actionable guidance across 14 critical categories of AI-powered threats that every person should understand:
Core AI Threats
- Deepfakes: Understanding AI-generated fake videos and images- Voice Cloning: Protecting against AI voice replication attacks- AI Avatars: Recognizing digital doubles and unauthorized AI personas- Biometric Spoofing: Defending against fingerprint, face, and voice security bypasses
Social & Data Threats
- Social Engineering: Modern psychological manipulation enhanced by AI- Data Brokers: How your personal information is collected and weaponized- Social Media AI: Understanding how platforms use your data for AI training- Digital Identity: Protecting against synthetic identity fraud
Technical & Financial Threats
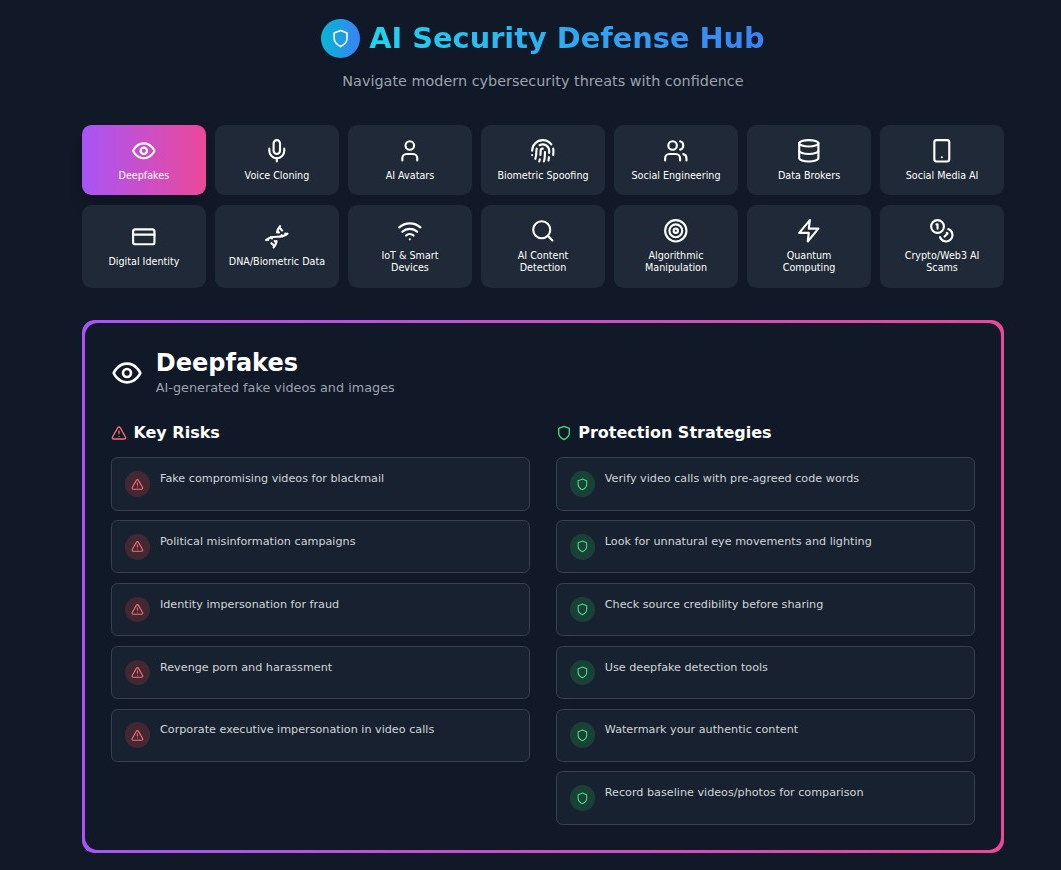
- DNA/Biometric Data Protection: Safeguarding genetic and biometric information- IoT & Smart Device Security: Securing your connected home and devices- AI Content Detection: Learning to identify AI-generated content- Algorithmic Manipulation: Understanding how AI influences your decisions- Quantum Computing Threats: Preparing for future cryptographic challenges- Crypto/Web3 AI Scams: Protecting your digital assets from AI-enhanced fraud
What Makes Our Platform Different
1. Detailed, Actionable Information
Unlike generic cybersecurity resources, each threat category includes:
- Real-world examples of how attacks occur- Specific protection strategies you can implement immediately- Detailed explanations of how the technology works- Links to actual tools and services for protection
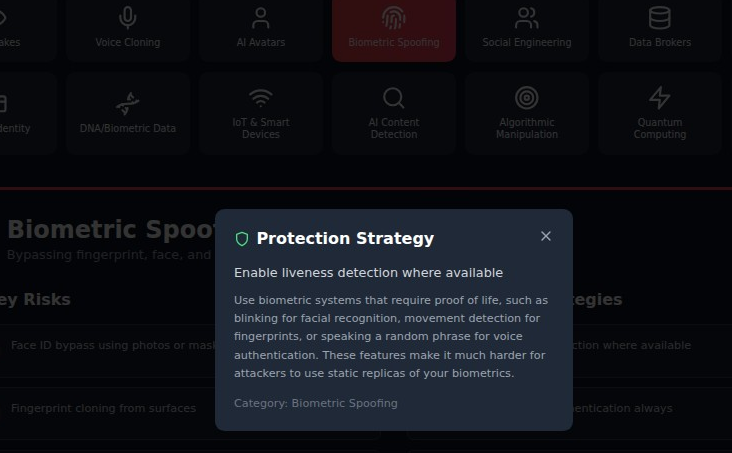
2. Enhanced Modal System
Every risk and protection strategy is supported by comprehensive explanations. Click on any item to get detailed context, implementation guidance, and real-world examples – transforming brief tips into actionable intelligence.
3. Comprehensive Resource Directory
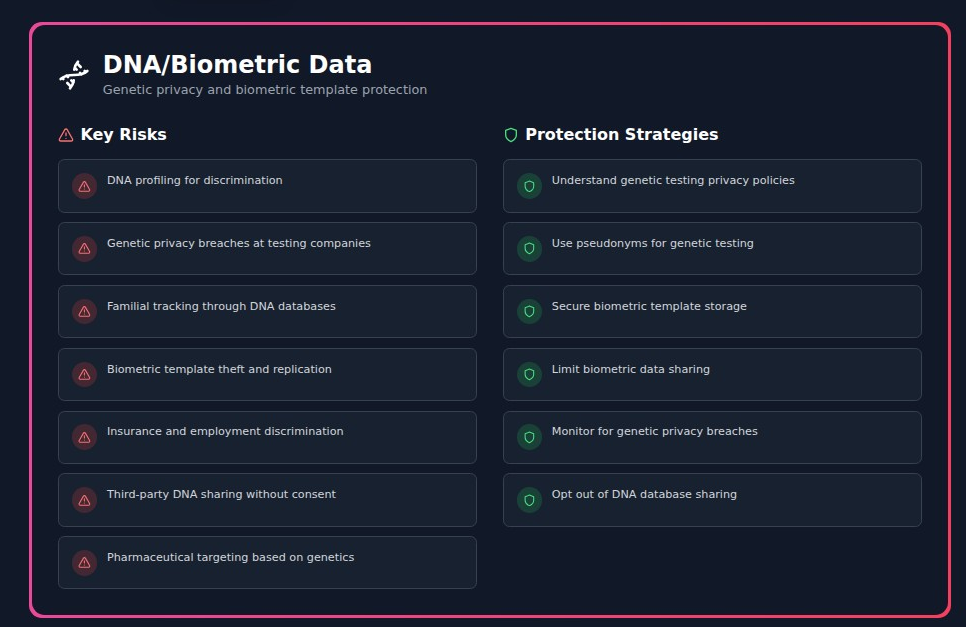
Our “Report & Get Help” section provides direct links to:
- Federal reporting agencies (FBI IC3, FTC, CISA)- AI detection tools (Reality Defender, Deepware Scanner, Microsoft Video Authenticator)- Identity protection services (Credit bureau freeze links, DeleteMe for data removal)- Emergency assistance contacts and procedures
4. Universal Protection Framework
Beyond category-specific advice, we provide six universal protection principles that form the foundation of AI-era security:
- Strong authentication practices- Maintaining healthy skepticism- Regular system updates- Continuous data monitoring- Digital hygiene practices- Emergency response planning
Real-World Impact: Why This Matters
The Grandmother Scam 2.0
Consider Sarah, a 78-year-old grandmother who received a panicked call from someone who sounded exactly like her grandson. The caller, using AI voice cloning technology, claimed to be in jail and needed $3,000 for bail money immediately. The voice was perfect every inflection, every speech pattern matched her grandson’s voice exactly.
Fortunately, Sarah had learned about voice cloning scams and family safe words through our platform. She asked the caller for their agreed-upon family safe word. The scammer, of course, didn’t know it. What could have been a devastating financial loss became a teaching moment for her entire family.
The Executive Deepfake
David, a mid-level manager at a Fortune 500 company, received a video call from someone who appeared to be his CEO, requesting an urgent wire transfer of $50,000 for a confidential acquisition. The video quality was perfect, the mannerisms were accurate, and the request seemed plausible.
However, David had learned about corporate deepfake attacks and implemented verification protocols. He politely ended the call and contacted the CEO through official company channels. The real CEO was in a meeting across town and had never made the request. The company’s quick action prevented a significant financial loss and led to improved security protocols company-wide.
The Rubio Deepfake Incident: A Wake-Up Call for Government Communications Security
The Crypto Influencer Trap
Maria, a 32-year-old marketing professional, was targeted by an AI-generated crypto influencer on social media. The fake influencer had thousands of followers, professional-looking trading results, and even appeared in live streams promoting a new “revolutionary” cryptocurrency.
Because Maria had learned about AI-generated fake influencers through our platform, she recognized the warning signs: too-perfect trading results, generic responses to specific questions, and high-pressure tactics. She researched the cryptocurrency independently and discovered it was a complete scam that ultimately defrauded over 10,000 people of more than $50 million.
Navigating the Crypto Landscape: An In-Depth Look at Privacy in the Future of Payments
Looking Forward: The Future of AI Security Education
The AI Security Defense Hub represents just the beginning of our commitment to democratizing AI security knowledge. We’re continuously updating our platform with:
- Emerging threat analysis as new AI attack vectors develop- Interactive simulations to help users practice identifying threats- Community reporting features for sharing new scam patterns- Integration with security tools for real-time threat detection
Industry Recognition and Trust
Our platform has been developed in partnership with cybersecurity experts, draws from official government resources, and maintains strict accuracy standards. We’re proud to be part of the broader MyPrivacy.blog ecosystem, which has been recognized for:
- Evidence-based privacy education- Practical, actionable advice- Commitment to user empowerment- Independence from commercial interests
Getting Started: Your First Steps
Protecting yourself from AI-powered threats doesn’t require a computer science degree – it requires awareness, preparation, and the right resources. Here’s how to get started:
- **Visit **ai.myprivacy.blog and explore each of the 14 threat categories2. Click on risks and protections that are most relevant to your situation to get detailed explanations3. Implement universal protection tips starting with the basics like strong authentication4. Share the resource with family members and colleagues who might be vulnerable5. Bookmark the “Report & Get Help” section for emergency situations
The Stakes Have Never Been Higher
We’re at an inflection point in the history of cybersecurity. The same AI technologies that are revolutionizing medicine, education, and communication are being weaponized by criminals with increasing sophistication and scale. The choice is clear: we can either educate ourselves and our communities about these threats, or we can remain vulnerable to them.
The AI Security Defense Hub isn’t just another cybersecurity resource – it’s a comprehensive defense system for the AI age. It’s designed to evolve with emerging threats, provide practical protection strategies, and empower individuals with the knowledge they need to stay safe in an increasingly complex digital landscape.
Join the Defense
Cybersecurity in the AI era isn’t just about technology – it’s about community. Every person who learns to identify a deepfake, every family that establishes voice verification protocols, and every organization that implements AI-aware security policies contributes to our collective defense against these threats.
Visit ai.myprivacy.blog today and take the first step toward comprehensive AI security awareness. Because in the age of artificial intelligence, the best defense is an informed community.
The AI Security Defense Hub is a free educational resource developed by the MyPrivacy.blog team. No registration required, no data collection, just comprehensive security education when you need it most.
**Ready to defend yourself against AI-powered threats? Start your journey at **ai.myprivacy.blog
About MyPrivacy.blog
MyPrivacy.blog is dedicated to providing practical, evidence-based privacy and security education without commercial interests or data collection. Our resources are developed by privacy experts and updated continuously to address emerging threats in our rapidly evolving digital landscape.
Connect with us:
- Main site: myprivacy.blog- AI Security: ai.myprivacy.blog- Social Media Privacy: socmed.myprivacy.blog- Digital Wealth Protection: digitalwealthshield.com