Private aviation represents the ultimate in travel convenience and luxury, offering unprecedented freedom from commercial airline schedules, security lines, and public exposure. Yet this freedom comes with a hidden cost that most aircraft owners and operators never fully understand: comprehensive surveillance of your travel patterns, business relationships, and personal activities through mandatory aircraft tracking systems that broadcast your movements in real-time to anyone with basic monitoring equipment.
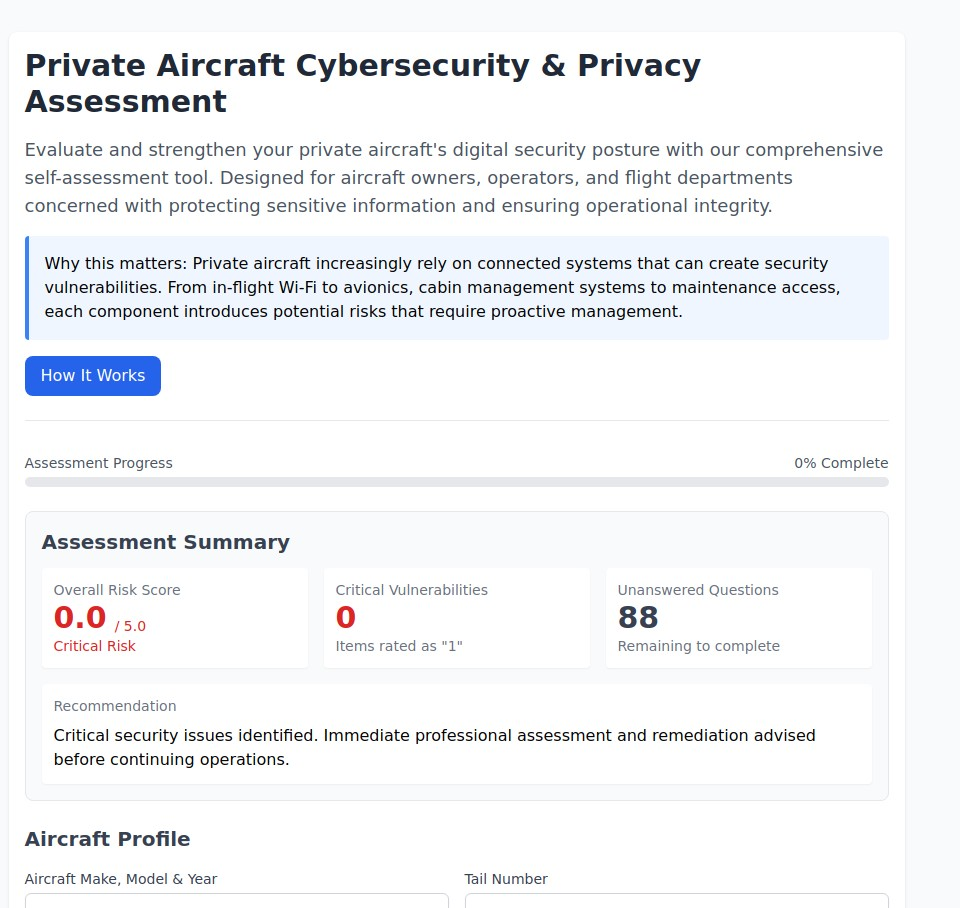
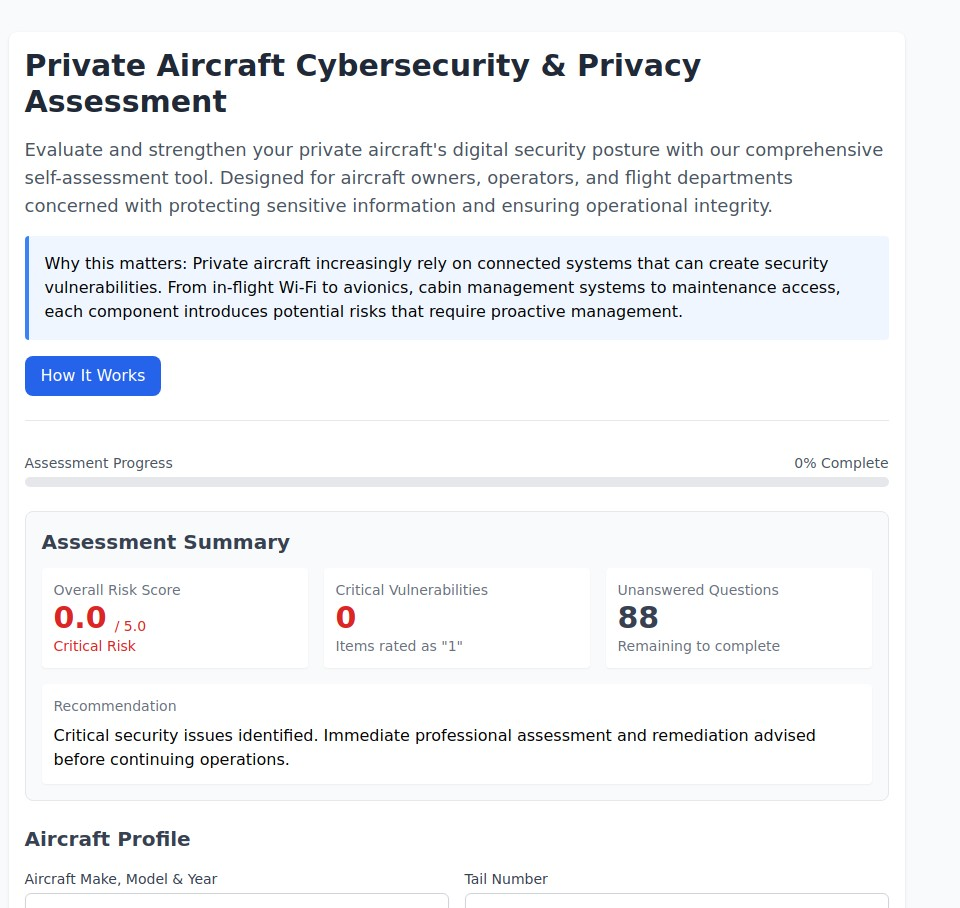
Aircraft Security Assessment Tool
Modern aircraft are required to broadcast their location, altitude, speed, and identification information through Automatic Dependent Surveillance-Broadcast (ADS-B) systems that create a detailed digital trail of every flight. This information is collected by government agencies, commercial tracking services, and amateur enthusiasts who publish flight data online, creating unprecedented transparency into the travel patterns of anyone using private aviation.
The implications extend far beyond simple location tracking. Flight data reveals business relationships through travel coordination, family connections through passenger manifests, financial status through aircraft ownership, and operational patterns that can be exploited by criminals, competitors, or anyone seeking to gather intelligence about high-net-worth individuals and their activities.
This comprehensive guide provides specialized privacy strategies designed specifically for aircraft owners, operators, and flight departments who must balance regulatory compliance with operational security and personal privacy. Whether you own a single aircraft or manage a corporate flight department, these evidence-based techniques will help you minimize surveillance exposure while maintaining the freedom and efficiency that makes private aviation valuable.
Understanding the Aviation Privacy Threat Landscape
Private aircraft operations create unique privacy challenges that extend far beyond the aircraft itself. Modern aviation privacy threats encompass multiple interconnected systems including aircraft tracking, ground operations, digital communications, travel coordination, and vendor relationships that collectively create comprehensive surveillance opportunities for anyone seeking intelligence about your activities.
The Aviation Privacy Paradox: Regulatory requirements mandate that aircraft broadcast their location and identification information for safety and air traffic control purposes, directly conflicting with the privacy and security needs of passengers who choose private aviation specifically to avoid public exposure and maintain operational discretion.
Modern aviation threats target high-value individuals and organizations through sophisticated intelligence gathering that combines publicly available flight tracking data with advanced OSINT techniques to build comprehensive profiles of travel patterns, business relationships, and operational vulnerabilities.
Assess your aviation privacy vulnerabilities with our specialized Private Aircraft Cybersecurity & Privacy Assessment. This comprehensive evaluation analyzes your aircraft operations across critical cybersecurity and privacy domains, providing personalized recommendations for aircraft owners, operators, and flight departments concerned with protecting sensitive information and ensuring operational integrity.
The Six Critical Aviation Privacy Risk Categories
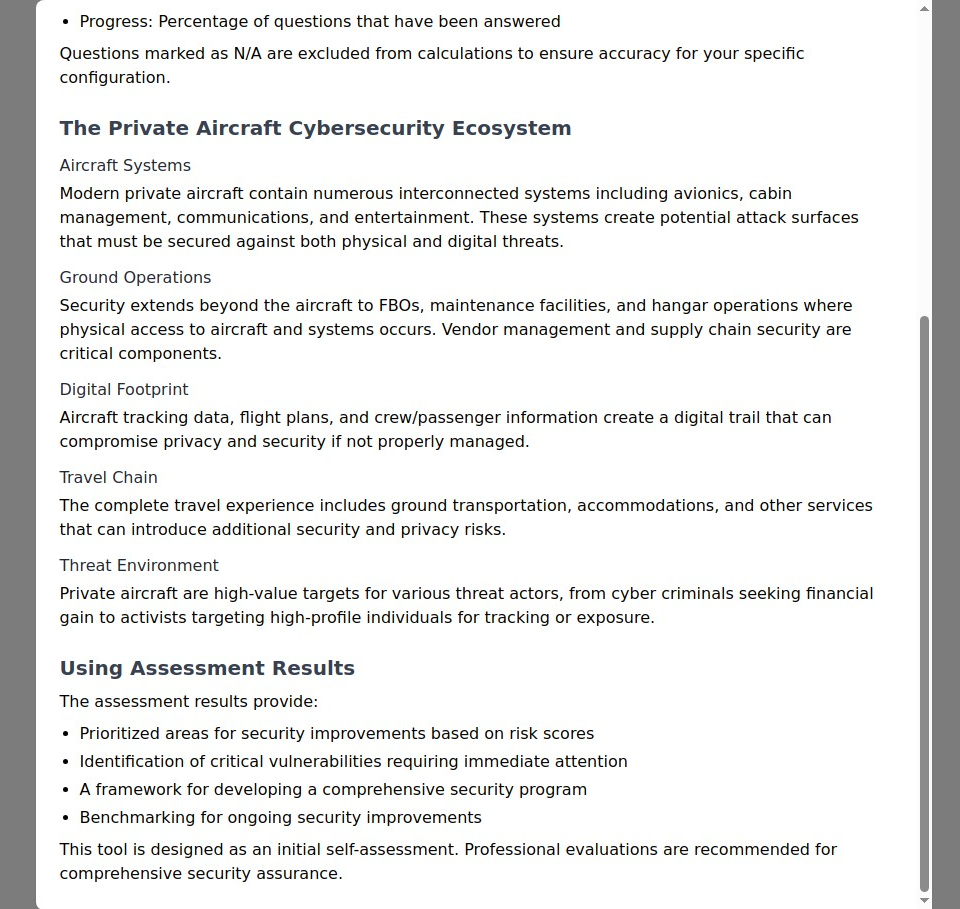
Our analysis of aviation privacy incidents and cybersecurity threats reveals that comprehensive protection requires addressing vulnerabilities across six interconnected operational domains:
Technical Systems Security:
- Aircraft Systems - Avionics, cabin management, communications, and entertainment systems that create potential cybersecurity and privacy vulnerabilities- Ground Operations - FBO services, maintenance facilities, and hangar operations where physical access to aircraft and systems occurs
Information and Intelligence Exposure:
- Digital Footprint - Aircraft tracking data, flight plans, and crew/passenger information that creates intelligence gathering opportunities- Travel Chain - Ground transportation, accommodations, and other services that can introduce additional security and privacy risks
Threat Environment Management:
- Vendor & Supply Chain Security - Third-party service providers and maintenance organizations that require access to aircraft systems and operational information- Threat Environment - Recognition that private aircraft are high-value targets for various threat actors, from cyber criminals seeking financial gain to activists targeting high-profile individuals for tracking or exposure
Each domain represents a different attack surface where aviation privacy can be compromised. Weakness in any area can undermine your entire operational security strategy, while comprehensive protection across all domains creates defense in depth that protects against even sophisticated targeting campaigns.
ADS-B Tracking and Real-Time Surveillance Threats
Automatic Dependent Surveillance-Broadcast (ADS-B) represents the most significant privacy challenge facing private aviation. This mandatory system requires aircraft to continuously broadcast their precise location, altitude, speed, direction, and unique identification code, creating real-time tracking capabilities that anyone with basic equipment can monitor.
Understanding ADS-B Privacy Implications
Real-Time Tracking Capabilities: ADS-B signals can be received by anyone with approximately $20 worth of equipment and basic technical knowledge. Websites like FlightRadar24, FlightAware, and ADSBExchange aggregate this data to provide public access to real-time aircraft tracking information that reveals:
- Precise location data with accuracy measured in meters- Flight patterns and routines that reveal regular travel habits- Aircraft identification linking flights to specific owners and operators- Operational patterns that can predict future travel and availability- Passenger and crew information through correlation with flight plans and manifests
Intelligence Gathering Opportunities: Sophisticated threat actors use ADS-B data combined with other intelligence sources to build comprehensive profiles of aircraft operations, including:
- Business relationship mapping through travel coordination and meeting patterns- Financial intelligence derived from aircraft ownership and operational patterns- Security vulnerability assessment identifying predictable routines and operational weaknesses- Personal activity monitoring tracking family travel, vacation patterns, and lifestyle activities
Legal Privacy Protection Options
FAA Privacy ICAO Address (PIA) Program: The Federal Aviation Administration offers the Privacy ICAO Address program that provides alternate identification codes for aircraft, reducing the ability to quickly identify aircraft ownership while maintaining air traffic control functionality.
PIA Program Benefits:
- Anonymous identification - Aircraft broadcasts a temporary code not linked to owner information in public databases- Maintained safety compliance - All safety and air traffic control functionality remains intact- Reduced tracking correlation - More difficult for third parties to link flights to specific owners or operators- International operation capability - PIA codes work for most international flight operations
PIA Program Limitations:
- Application process requirements including detailed justification and owner verification- Limited availability with program restrictions and potential waiting periods- Operational constraints including specific procedures for international flight operations- Detection possibilities through sophisticated monitoring and correlation techniques
Limiting Aircraft Data Displayed (LADD) Program: The LADD program restricts the distribution of aircraft tracking data through FAA systems, reducing availability of flight information through government data sharing agreements.
LADD Program Protection:
- Government data restriction - Limits FAA sharing of flight data with commercial tracking services- Reduced commercial availability - Decreases aircraft information in many popular flight tracking websites- Historical data protection - Restricts access to past flight information and pattern analysis- Enhanced enforcement - FAA monitoring and penalties for unauthorized data sharing
LADD Program Implementation:
- Simple enrollment process requiring basic aircraft and owner information- Immediate effectiveness with restrictions taking effect shortly after enrollment- No operational impact on aircraft operations or air traffic control services- Ongoing protection with automatic renewal and continued data restriction
Advanced Aviation Privacy Techniques
Third-Party Tracking Opt-Out Procedures: Beyond government programs, aircraft owners must address commercial tracking services that aggregate ADS-B data from private receivers and provide public access to flight information.
Commercial Tracking Service Management:
- Direct opt-out requests to major tracking services including FlightRadar24, FlightAware, and Plane Finder- Ongoing monitoring for unauthorized tracking and data aggregation services- Legal enforcement when tracking services fail to honor legitimate opt-out requests- Alternative tracking detection using specialized monitoring to identify new tracking sources
Operational Security Measures:
- Flight planning privacy avoiding predictable patterns and routine scheduling that enables tracking prediction- Route variation techniques using different airports, routing, and timing to prevent pattern recognition- Communication security protecting flight coordination and planning information from interception- Crew and passenger security training and protocols to prevent information disclosure
Aircraft Cybersecurity and Connected Systems Protection
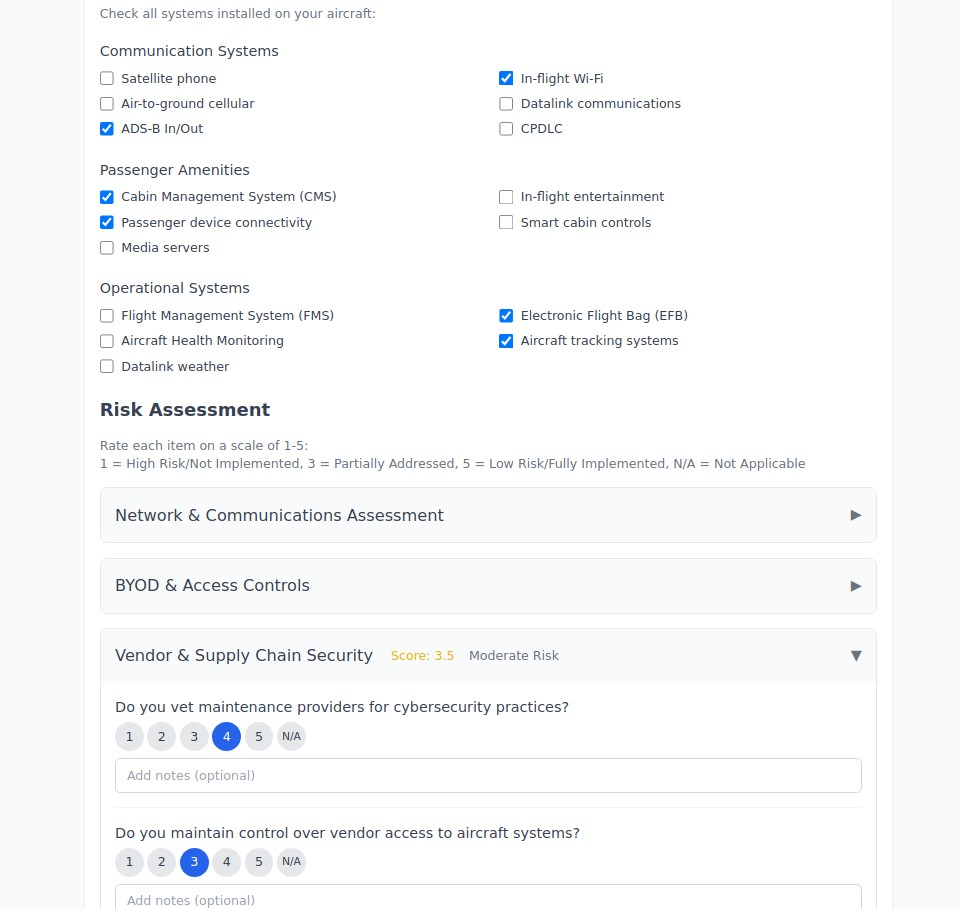
Modern aircraft contain sophisticated interconnected systems including avionics, cabin management, communications, and entertainment that create potential cybersecurity vulnerabilities requiring specialized protection measures.
Aircraft Systems Security Assessment
Communication Systems Vulnerabilities: Modern aircraft communication systems create multiple potential entry points for cybersecurity threats:
- Satellite phone systems that may lack encryption or use vulnerable protocols- Air-to-ground cellular connections that can be intercepted or monitored- ADS-B In/Out systems that receive and transmit data with minimal security protection- Datalink communications including CPDLC and weather systems that may be vulnerable to manipulation- In-flight Wi-Fi systems that create internet connectivity with potential security risks
Passenger Amenity System Risks: Cabin systems designed for passenger convenience often lack robust security measures:
- Cabin Management Systems (CMS) that control lighting, climate, and entertainment may be vulnerable to unauthorized access- Passenger device connectivity allowing personal devices to connect to aircraft systems- Media servers and entertainment systems that may contain vulnerabilities or serve as entry points- In-flight entertainment systems that could be compromised to access other aircraft systems- Smart cabin controls that provide enhanced passenger experience while creating additional attack surfaces
Operational Systems Protection: Critical flight systems require specialized cybersecurity protection:
- Flight Management Systems (FMS) that control navigation and flight planning- Electronic Flight Bag (EFB) systems containing sensitive operational and route information- Aircraft Health Monitoring systems that track aircraft performance and maintenance needs- Weather and navigation systems that provide critical flight information- Aircraft tracking systems beyond ADS-B that may reveal operational information
Cybersecurity Best Practices for Aircraft Operations
Network and Communications Security:
- Network segmentation isolating critical flight systems from passenger and convenience systems- Encryption implementation for all communications and data transmission systems- Access control management restricting system access to authorized personnel only- Regular security updates maintaining current software and firmware across all aircraft systems
Vendor and Supply Chain Security: Aircraft operations depend on numerous third-party service providers who require access to aircraft systems and operational information:
- Maintenance provider vetting ensuring cybersecurity practices for organizations with physical aircraft access- FBO security assessment evaluating fixed base operators for information security and operational security practices- Ground service security protecting aircraft during ground operations including fueling, catering, and cleaning services- Parts and supply chain security ensuring components and systems maintain integrity throughout procurement and installation
Ground Operations and FBO Security
Aircraft security extends beyond the aircraft itself to encompass all ground operations including maintenance, fueling, catering, cleaning, and hangar storage that create opportunities for physical access and information gathering.
Fixed Base Operator (FBO) Security Assessment
Information Security at FBOs: FBOs maintain extensive records about aircraft operations, passenger information, and operational patterns that create intelligence gathering opportunities:
- Flight planning and scheduling information that reveals travel patterns and operational routines- Passenger manifest and contact information that identifies travelers and their relationships- Fuel and service records that indicate aircraft operational patterns and capabilities- Ground transportation coordination that extends tracking and surveillance beyond the aircraft- Communication and coordination records that reveal business relationships and operational security
Physical Security Considerations:
- Aircraft access control ensuring only authorized personnel have access to aircraft during ground operations- Hangar and ramp security protecting aircraft from unauthorized access and tampering- Service provider vetting ensuring ground service personnel meet appropriate security standards- Equipment and system security protecting against unauthorized access to aircraft systems during maintenance and service
Enhanced FBO Security Measures: For high-profile aircraft operations, additional security considerations include:
- Private hangar facilities providing enhanced physical security and operational privacy- Dedicated ground services using vetted personnel and enhanced security protocols- Secure communication systems protecting operational coordination and passenger information- Advanced access control including biometric systems and enhanced personnel screening
Maintenance and Service Provider Security
Maintenance Facility Security: Aircraft maintenance creates extensive access to aircraft systems and operational information requiring specialized security measures:
- Personnel security screening ensuring maintenance technicians and facility staff meet appropriate security standards- Information handling protocols protecting operational and ownership information during maintenance activities- System access controls restricting maintenance access to necessary systems while protecting sensitive operational data- Documentation security protecting maintenance records and operational information from unauthorized disclosure
Mobile and Remote Service Security:
- Mobile maintenance security protecting aircraft during on-site maintenance and service activities- Remote diagnostic security ensuring aircraft health monitoring and remote system access maintains appropriate security- Emergency service security maintaining security protocols during aircraft system failures or emergency situations- International service coordination managing security requirements for maintenance and service in foreign locations
International Aviation Privacy Considerations
International private aviation operations create additional privacy and security challenges through varying regulatory requirements, border security procedures, and international data sharing agreements that affect operational privacy and passenger protection.
International Flight Privacy Planning
Regulatory Compliance Across Jurisdictions: Different countries maintain varying requirements for aircraft identification, passenger information, and operational reporting:
- ICAO address requirements understanding how different countries handle aircraft identification and privacy protection- Flight plan and manifest requirements managing passenger information disclosure requirements across different jurisdictions- Customs and immigration coordination protecting passenger privacy while meeting international entry and exit requirements- International tracking and surveillance understanding how different countries monitor and track aircraft operations
Cross-Border Data Protection:
- Passenger information protection ensuring personal information receives appropriate protection across different privacy law jurisdictions- Operational data security protecting flight planning, routing, and operational information during international operations- Communication security maintaining secure communications across international boundaries and varying regulatory environments- Documentation management protecting sensitive operational and passenger information in international filing requirements
International Privacy Protection Strategies
Advanced International Privacy Techniques:
- International entity structures using appropriate business entities to protect aircraft ownership information in international operations- Diplomatic and government relations understanding how diplomatic status and government relationships affect aviation privacy- International legal consultation working with legal professionals who understand aviation privacy across multiple jurisdictions- Cultural and operational security adapting privacy and security measures to different cultural and operational environments
For aircraft owners with complex international business activities or high-profile public visibility, international aviation privacy requires coordination with broader identity protection strategies and comprehensive personal privacy measures.
Business Aviation Privacy Strategies
Corporate flight departments and business aviation operations face unique challenges balancing operational efficiency with privacy protection for executives, clients, and business activities that require specialized privacy strategies.
Corporate Flight Department Security
Executive Protection Integration: Business aviation privacy must integrate with broader executive protection and corporate security strategies:
- Travel coordination security protecting executive travel information and operational planning- Business relationship privacy preventing unauthorized disclosure of business meetings and relationships through flight tracking- Competitive intelligence protection securing operational information from competitors and business adversaries- Client and customer privacy protecting client information and business relationships during corporate flight operations
Corporate Information Security:
- Business communication security protecting corporate communications and coordination during flight operations- Document and information handling securing sensitive business information during corporate flight operations- Meeting and event coordination protecting information about corporate meetings, events, and business activities- Financial and operational security protecting corporate financial information and operational intelligence
The Complete Guide to Digital Privacy Protection: Your Comprehensive Toolkit for 2025
Flight Department Operational Security
Internal Security Measures:
- Personnel security protocols ensuring flight department staff maintain appropriate security standards and information handling practices- Information sharing limitations restricting access to corporate flight information on a need-to-know basis- Communication security standards implementing secure communication systems for corporate flight coordination- Vendor and service provider management ensuring third-party aviation service providers meet corporate security standards
Advanced Corporate Aviation Privacy:
- Multiple aircraft strategies using fleet management techniques to obscure travel patterns and operational routines- Scheduling obfuscation implementing scheduling techniques that prevent pattern recognition and predictive tracking- International corporate aviation managing privacy and security requirements for international corporate flight operations- Crisis management and emergency response maintaining privacy and security during corporate aviation emergencies and unusual situations
Technology Solutions for Aviation Privacy
Aviation Privacy Technology Stack
Aircraft System Security Tools:
- Cybersecurity monitoring systems for detecting unauthorized access attempts and system vulnerabilities- Communication encryption securing aircraft communications and data transmission- System access controls restricting and monitoring access to critical aircraft systems- Threat detection systems identifying potential cybersecurity threats and unauthorized system access
Flight Operations Security:
- Secure flight planning systems protecting flight planning information and operational coordination- Encrypted communication tools for secure coordination between aircraft, ground operations, and passengers- Operational security software managing and protecting sensitive operational information- Privacy monitoring services detecting unauthorized flight tracking and information disclosure
Professional Aviation Security Services:
- Aviation cybersecurity consultation specialized expertise in aircraft system security and operational protection- Flight tracking monitoring professional services to detect and manage unauthorized flight tracking- International aviation privacy consultation for complex international operations requiring specialized privacy protection- Corporate aviation security enterprise-level security services for corporate flight departments and business aviation operations
Advanced Aviation Privacy Technology
Cutting-Edge Aviation Security:
- Advanced encryption systems for aircraft communications and operational systems- Behavioral monitoring systems detecting unusual system access or operational patterns that may indicate security threats- International privacy coordination technology solutions for managing privacy requirements across multiple jurisdictions- Professional threat monitoring specialized services for high-risk aviation operations requiring advanced threat detection and response
Building Sustainable Aviation Privacy Practices
Daily Aviation Security Operations
Pre-Flight Security Protocols:
- Aircraft system security verification ensuring all aircraft systems maintain appropriate security settings and configurations- Communication security setup verifying secure communication systems for flight operations and passenger coordination- Operational information protection securing flight planning, passenger, and operational information before departure- Ground operations security implementing security measures for ground operations including fueling, catering, and passenger boarding
In-Flight Security Management:
- Communication security protocols maintaining secure communications during flight operations- System monitoring procedures ongoing monitoring of aircraft systems for security threats and unauthorized access- Information handling standards protecting sensitive information and communications during flight- Emergency security procedures protocols for handling security incidents during flight operations
Monthly Aviation Privacy Assessment
Comprehensive Aviation Security Review:
- Aircraft system security audit monthly evaluation of all aircraft systems for security vulnerabilities and configuration issues- Operational security assessment reviewing ground operations, vendor relationships, and service provider security practices- Flight tracking and surveillance monitoring detecting unauthorized tracking and information gathering activities- International compliance review ensuring ongoing compliance with privacy and security requirements across operational jurisdictions
Strategic Aviation Privacy Planning:
- Threat environment assessment evaluating current threat levels and adjusting security measures accordingly- Technology and system updates implementing security updates and system improvements to maintain optimal protection- Personnel and vendor security review ongoing evaluation of personnel security and vendor compliance with security standards- Privacy protection effectiveness measurement assessing the effectiveness of current privacy protection measures and identifying areas for improvement
Measuring Aviation Privacy Protection Effectiveness
Aviation Privacy Metrics
Quantitative Security Indicators:
- Flight tracking exposure reduction measurable decrease in unauthorized flight tracking and public availability of flight information- System security improvement enhanced cybersecurity posture across aircraft systems and operational infrastructure- Operational security enhancement improved protection of operational information and business intelligence- Vendor and service provider security enhanced security standards and compliance across aviation service providers
Qualitative Privacy Assessment:
- Operational confidence level comfort and confidence in aircraft operations and privacy protection- Business relationship protection successful protection of business relationships and operational intelligence- Executive and passenger satisfaction satisfaction with privacy protection during aircraft operations- International operational security successful privacy protection during international flight operations
Professional Aviation Security Evaluation
Aviation Privacy Effectiveness Review:
- Monthly aviation security assessment using our comprehensive evaluation tool to track security improvements and identify emerging vulnerabilities- Quarterly professional consultation for aircraft operations requiring ongoing threat assessment and security planning- Annual comprehensive security audit for high-profile aircraft operations requiring sophisticated protection measures- Ongoing education and training staying current with new aviation threats and protection techniques
The Future of Aviation Privacy and Security
Emerging Aviation Threats
Next-Generation Surveillance Technologies: New surveillance technologies including enhanced satellite tracking, artificial intelligence analysis of flight patterns, and improved correlation techniques will create additional challenges for aviation privacy protection.
Cybersecurity Evolution: Aircraft systems continue becoming more connected and sophisticated, creating new cybersecurity vulnerabilities while also providing enhanced security capabilities for appropriately protected aircraft.
Regulatory and International Developments: Changing aviation regulations, international agreements, and privacy laws will affect how aircraft operations can be protected while maintaining regulatory compliance.
Aviation Privacy Technology Advancement
Enhanced Protection Systems:
- Advanced encryption and security systems providing improved protection for aircraft communications and operational systems- Artificial intelligence threat detection using advanced monitoring systems to detect and respond to emerging threats- International privacy coordination improved technology solutions for managing privacy across multiple jurisdictions- Professional aviation security services enhanced professional services designed specifically for high-risk aviation operations
Taking Action: Your Aviation Privacy Protection Plan
Private aviation should enhance your privacy and security, not compromise it. The techniques outlined in this guide provide comprehensive protection that allows you to enjoy the benefits of private aviation while maintaining appropriate operational security and personal privacy.
Start with professional assessment: Aviation privacy requires understanding your specific operational vulnerabilities, threat environment, and regulatory requirements. Generic security advice often misses critical aviation-specific risks while recommending inappropriate measures that don’t match aircraft operational realities.
Complete our Private Aircraft Cybersecurity & Privacy Assessment to evaluate your aircraft operations across all critical cybersecurity and privacy domains. This comprehensive tool is designed specifically for aircraft owners, operators, and flight departments concerned with protecting sensitive information and ensuring operational integrity.
Phase 1: Critical Aviation Security Implementation (Week 1)
Immediate Priority Actions:
- Complete comprehensive aviation privacy assessment to identify critical vulnerabilities requiring urgent attention2. Enroll in FAA privacy protection programs including LADD and PIA programs to reduce flight tracking exposure3. Implement aircraft system security measures addressing critical cybersecurity vulnerabilities in aircraft systems4. Establish operational security protocols protecting flight planning, passenger information, and operational coordination
Phase 2: Comprehensive Aviation Privacy Protection (Month 1)
Advanced Security Deployment:
- Deploy advanced aircraft cybersecurity measures including network segmentation, communication encryption, and access controls2. Implement vendor and service provider security ensuring all aviation service providers meet appropriate security standards3. Establish international privacy protection for aircraft operations across multiple jurisdictions4. **Coordinate **comprehensive identity protection extending protection to personal and business information
Phase 3: Advanced and Specialized Aviation Protection (Month 2+)
Risk-Specific Enhancement: Based on your assessment results and operational profile, implement specialized protections:
- High-net-worth privacy coordination for complex asset portfolios and luxury lifestyle coordination- Advanced OSINT protection for aircraft operations facing sophisticated intelligence gathering- Executive and public figure protection for high-profile aircraft operations requiring specialized security- Comprehensive personal privacy integration coordinating aviation privacy with broader privacy strategies
Ongoing Aviation Privacy Maintenance
Pre-Flight Security Checks:
- Verify aircraft system security settings and configurations- Review operational security protocols and passenger information protection- Confirm vendor and service provider security compliance- Check flight tracking and surveillance monitoring systems
Monthly Professional Assessment:
- Reassess aviation privacy using our comprehensive evaluation tool- Review and update protection strategies based on changing threat levels and operational requirements- Coordinate with professional aviation security consultants as needed- Update crisis response and emergency procedures based on evolving threats
Your aircraft represents significant investment and operational capability that deserves appropriate protection. The privacy and security measures you implement today determine whether you can enjoy the benefits of private aviation while maintaining the operational security and personal privacy that make private aviation valuable.
Take control of your aviation privacy today. Complete our Private Aircraft Cybersecurity & Privacy Assessment and discover exactly what vulnerabilities could be compromising your aircraft operations and personal security. Your operational freedom and personal safety depend on the aviation privacy protection decisions you make now.
Aircraft Security Assessment Tool
Aviation privacy protection is most effective when implemented before you become a target. Assess your aircraft privacy vulnerabilities today and build the protection you need to safely operate your aircraft while maintaining operational security and personal privacy.