On November 12, 2025, Apple quietly launched one of the most significant expansions of digital identity infrastructure in US history. The question isn’t whether it’s convenient—it’s whether we’re trading privacy for that convenience.
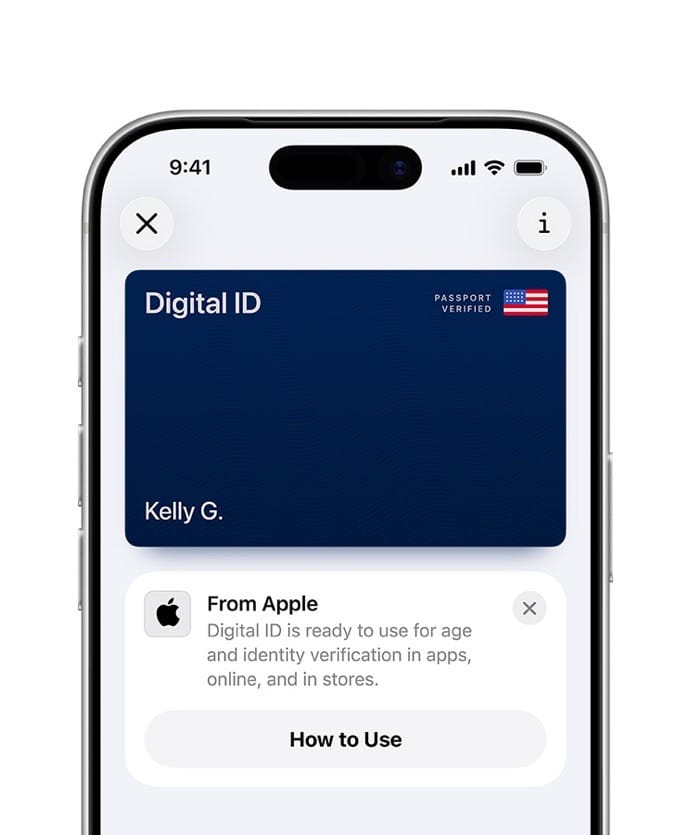
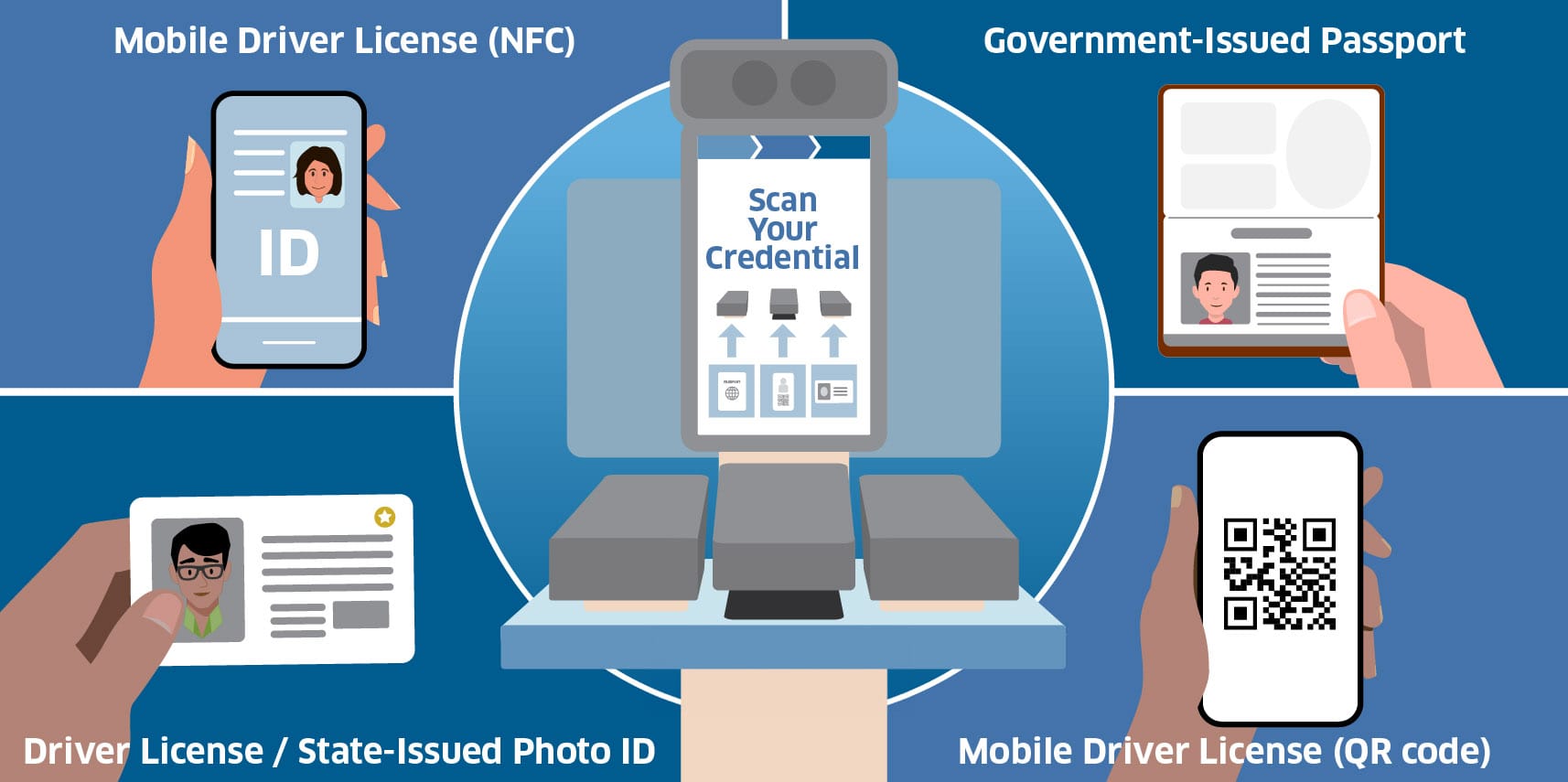
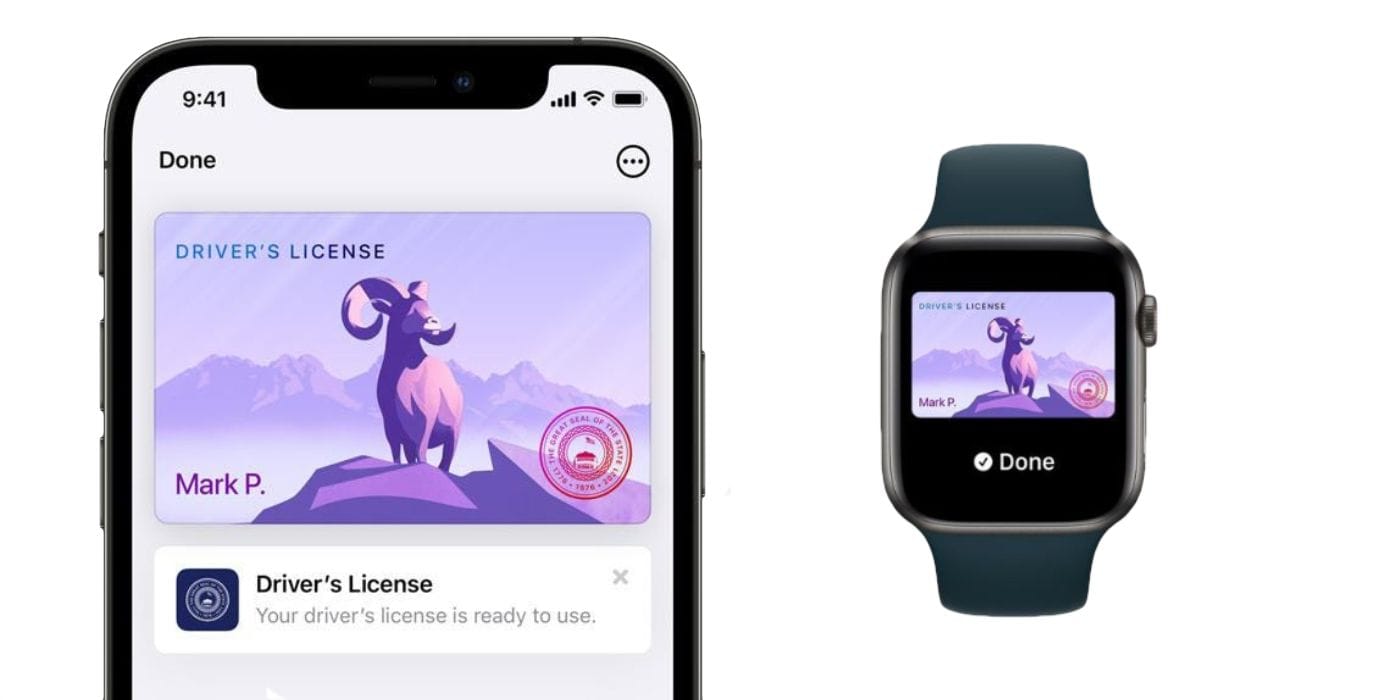
Apple’s new Digital ID feature allows US passport holders to create a digital identity credential stored in Apple Wallet, marking the tech giant’s most ambitious move yet to replace physical identification. Starting at over 250 TSA airport checkpoints nationwide, travelers can now tap their iPhone or Apple Watch to verify their identity—no physical documents required.
Biometric Tracker - Privacy & Security Analysis
While Apple touts encryption and privacy protections, the launch arrives at a critical moment when digital identity systems are rapidly expanding worldwide, often with troubling implications for personal privacy and civil liberties.
What Apple’s Digital ID Actually Does
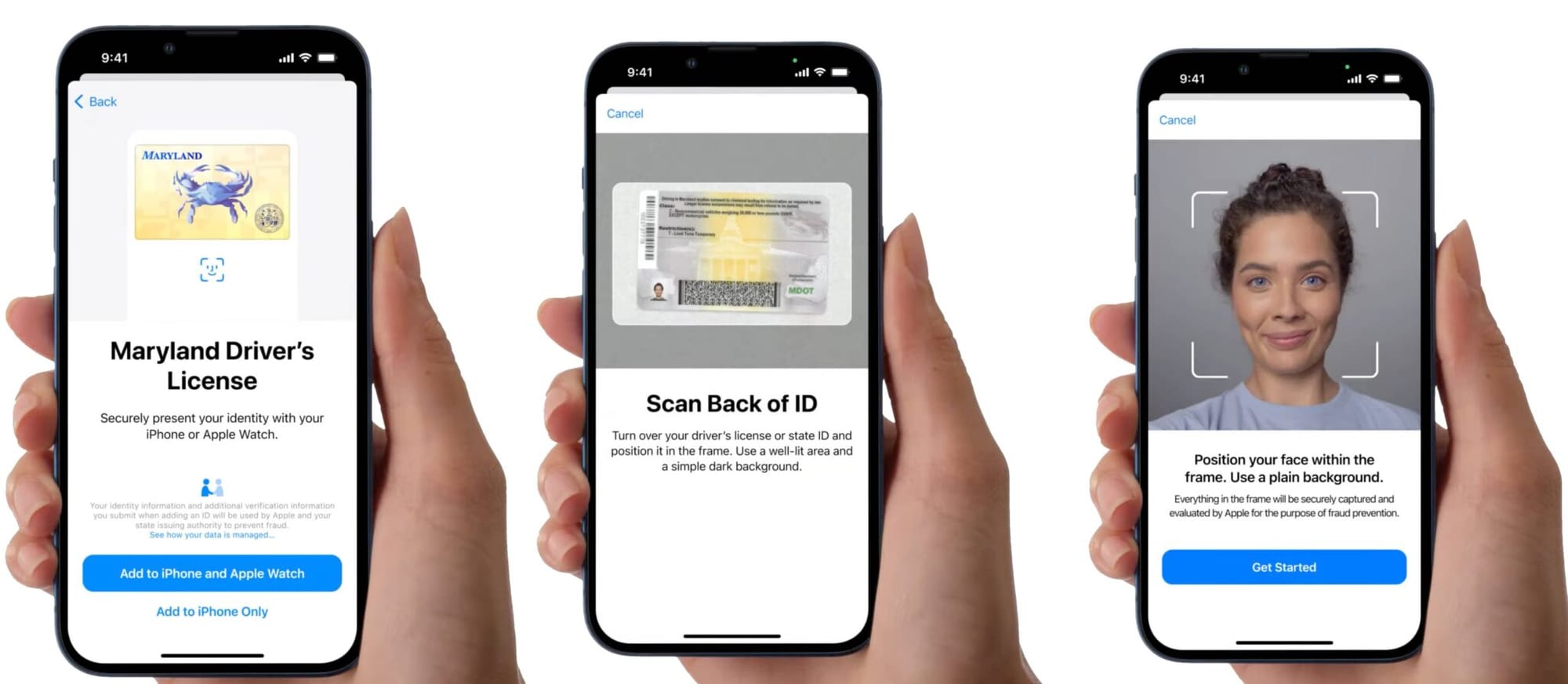
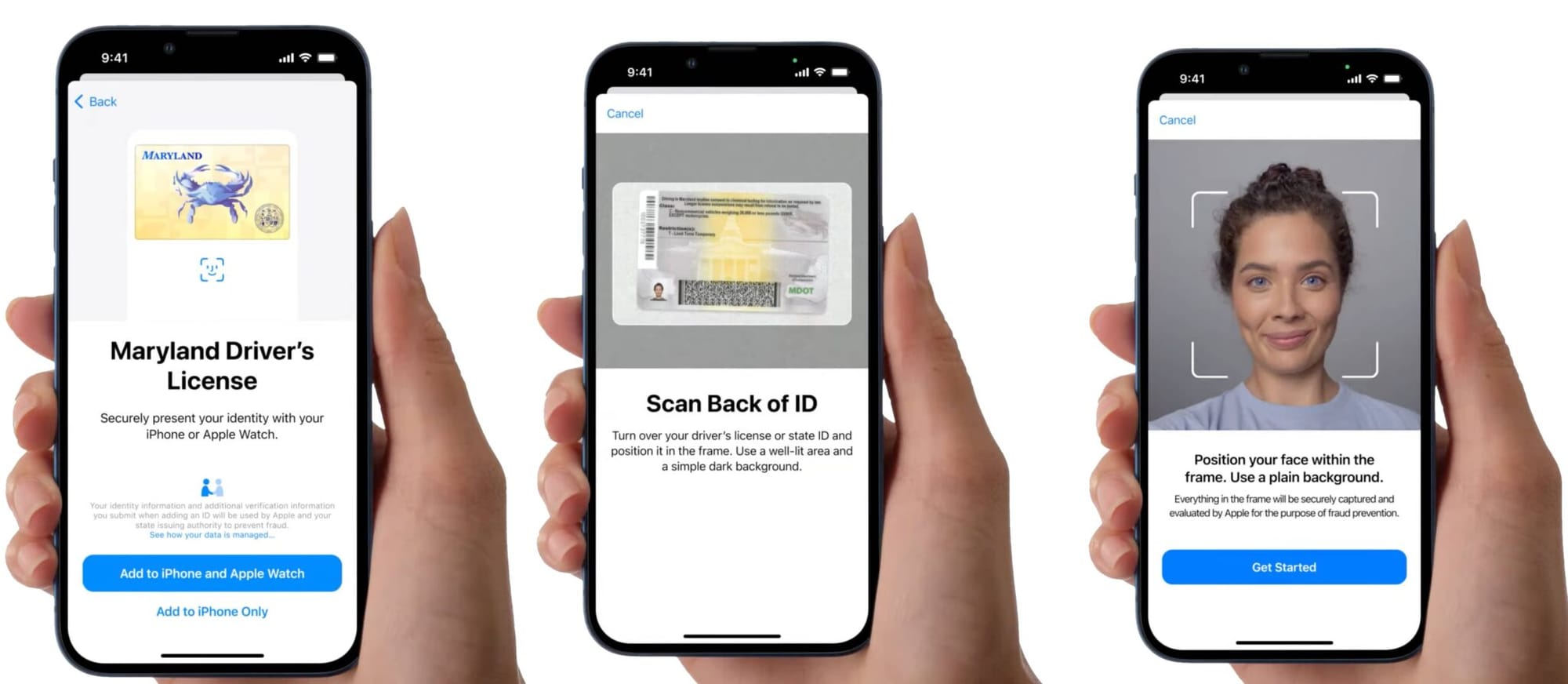
The implementation is straightforward but technically sophisticated. Users with a US passport can create a Digital ID by:
- Scanning their passport’s photo page2. Reading the embedded NFC chip on the passport’s back cover3. Taking a selfie for facial verification4. Completing a series of head and facial movements to prevent spoofing
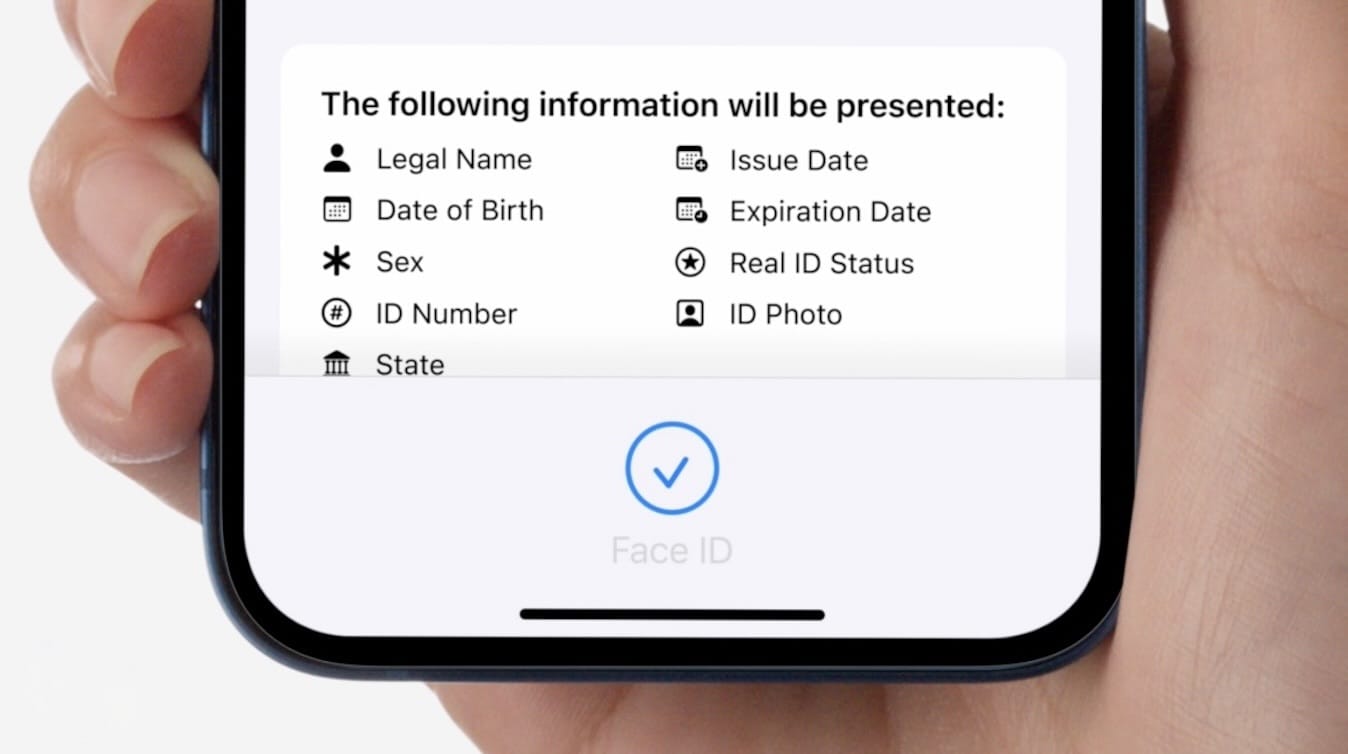
Once created, the Digital ID lives in Apple Wallet and can be presented at TSA checkpoints by double-clicking the iPhone’s side button and authenticating with Face ID or Touch ID. The system shows users exactly what information is being shared before transmission, and no device unlocking or physical handover is required.
PII Compliance Navigator | U.S. State Privacy Law Sensitive Data Categories
Apple emphasizes that the Digital ID is not a replacement for physical passports and cannot be used for international travel or border crossings. It’s designed as a convenience feature for domestic air travel—at least for now.
Apple’s Privacy Architecture: Better Than Most, But Still Concerning
To Apple’s credit, the company has implemented stronger privacy protections than many competing digital identity systems. The architecture includes several key safeguards:
 On-Device Encryption: All Digital ID data is encrypted and stored locally on the device, not in Apple’s cloud infrastructure. This represents a significant departure from centralized identity databases that create single points of catastrophic failure.
On-Device Encryption: All Digital ID data is encrypted and stored locally on the device, not in Apple’s cloud infrastructure. This represents a significant departure from centralized identity databases that create single points of catastrophic failure.
Minimal Data Sharing: Users see and approve exactly what information is transmitted before sharing. The system employs selective disclosure, sending only the data necessary for each transaction rather than exposing complete identity records.
No Apple Tracking: According to Apple’s documentation, the company cannot see when, where, or how users present their Digital ID. This stands in contrast to many digital identity platforms that create comprehensive tracking profiles.
Biometric Authentication: Face ID or Touch ID requirements ensure only the device owner can present credentials, adding a layer of protection against unauthorized access.
These protections place Apple’s implementation ahead of many government-run digital identity schemes. However, comparing Apple favorably to poorly designed government systems sets an exceptionally low bar.
US State Privacy Rights Comparison Tool | 20 States, 21 Rights
The Broader Context: A Global Digital ID Infrastructure
Apple’s launch doesn’t exist in isolation. It’s part of a massive global expansion of digital identity systems that privacy advocates have been warning about for years.
As documented in our comprehensive Global Digital ID Systems Status Report, over 100 countries have now implemented or are developing national digital identity systems. Governments have issued approximately 5 billion digital identities globally, with 186 out of 198 countries maintaining foundational ID systems where identity records are stored in digital format.
This rapid proliferation creates several interconnected concerns:
Function Creep: Systems implemented for one limited purpose—like airport security—inevitably expand into other areas. Apple already signals this trajectory, stating that “in the future, users will be able to present their Digital ID at additional select businesses and organizations for identity and age verification in person, in apps, and online.”
What starts as optional convenience at airports can quickly become mandatory verification for accessing websites, entering buildings, purchasing age-restricted products, or proving eligibility for services. Each expansion normalizes digital identity requirements in contexts where they previously didn’t exist.
Normalization of Constant Identification: Stanford University fellow Elizabeth Renieris articulated the core concern in 2021 when Apple first announced wallet-based IDs: “The sleeker these credentials are, the more they’re embedded into things we’re always attached to like a mobile device, which we take everywhere, the more there’s an incentive to introduce identity requirements in contexts where it never existed before. We’re running a risk where we’ll be in a situation where we always have to identify ourselves.”
That risk has only intensified with passport-based Digital IDs. The combination of convenience and ubiquity creates pressure to identify yourself constantly—at retail stores, entertainment venues, websites, and public spaces. This fundamentally alters the relationship between individuals and institutions.
Infrastructure for Comprehensive Surveillance: While Apple’s current implementation may preserve privacy, the infrastructure being built could easily be repurposed for surveillance if standards change, regulations weaken, or systems are breached.
The Honeypot Problem: What Happens When Systems Fail
Apple has an excellent security track record, but no system is impenetrable. The concentration of sensitive identity credentials creates what security researchers call “honeypots”—high-value targets that inevitably attract sophisticated attackers.
Our investigation into The Digital Honeypot: Breaches and System Failures in Centralized Digital Identity reveals the devastating consequences when identity systems fail:
Biometric Data Breaches Are Permanent: Unlike passwords that can be changed, compromised biometric data creates permanent vulnerabilities. When fingerprints or facial recognition data are stolen, victims face lifelong identity theft risks with no recourse for protection. As one security researcher noted: “You can change a password easily, but not your passport.”
Third-Party Verification Services Fail Catastrophically: The Israeli firm AU10TIX, which provides identity verification for X (formerly Twitter), LinkedIn, PayPal, and other major platforms, suffered a massive security incident after failing to secure an admin login for 18 months. The breach exposed identity information including names, birthdates, nationalities, ID numbers, and ID images for millions of users across multiple platforms.
Scale Magnifies Damage: When India’s Aadhaar biometric ID system experienced breaches, between February 2017 and May 2018 alone, there were nearly 40 isolated incidents. The leaked data included not just Aadhaar numbers and demographics, but highly sensitive information about pregnancy status, religion, caste, and bank details—demonstrating how identity database breaches expose far more than basic identification.
Apple’s on-device storage mitigates some centralized database risks, but creates new vulnerabilities around device security, backup systems, and the broader ecosystem of identity readers and verification infrastructure.
Law Enforcement Access and Fourth Amendment Concerns
A particularly troubling aspect of storing identification on smartphones involves law enforcement access. According to nonprofit Upturn, approximately 2,000 law enforcement agencies across all 50 states possess tools capable of extracting data from iPhones.
The Fourth Amendment protects against illegal search and seizure, and the Electronic Communications Privacy Act (ECPA) of 1986 establishes procedures law enforcement must follow. However, the practical reality is more complicated:
Border Exception Doctrine: Constitutional protections weaken at borders and international airports—precisely where Apple’s Digital ID is designed for use. Customs and Border Protection claims authority to search electronic devices without warrants at ports of entry.
Compelled Device Access: Courts have issued conflicting rulings about whether law enforcement can compel individuals to unlock biometric-protected devices. While Fifth Amendment protections may prevent compelling passcode disclosure, some courts have ruled that biometric authentication (the same Face ID or Touch ID protecting Digital ID) can be compelled.
Pretextual ID Checks: If showing your Digital ID requires unlocking your device and accessing Apple Wallet, it creates opportunities for pretextual access to your phone during routine identification checks. The ACLU has highlighted how digital ID on smartphones could become a backdoor requiring device unlocking under the pretext of verifying identification.
Technology Evolution: Phone cracking tools continue advancing. What seems secure today may be trivially bypassed tomorrow, and historical identity data remains vulnerable as security is compromised.
The REAL ID Connection and Regulatory Pressure
Apple’s Digital ID launch timing is strategic. REAL ID enforcement for domestic air travel became mandatory in May 2025, creating millions of travelers who might not have compliant identification. Digital ID positioned as a federal alternative to REAL ID compliance.
This regulatory pressure is part of broader government efforts to standardize and expand digital identity verification. While REAL ID focused on physical document security, the shift toward digital credentials enables far more extensive verification requirements:
Age Verification Mandates: Multiple jurisdictions are implementing laws requiring platforms to verify user ages to restrict minor access to certain content. These regulations create demand for reliable, scalable age verification—making digital identity systems from companies like Apple valuable compliance infrastructure.
Cross-Border Standards: Apple’s implementation supports the W3C Digital Credentials API, enabling cross-platform interactions and setting groundwork for international digital identity interoperability. This standardization facilitates global identity tracking mechanisms.
Private Sector Adoption: Once TSA checkpoints accept Digital ID, bars, retailers, financial institutions, and online platforms will face pressure to implement similar verification. The infrastructure being built for airports becomes general-purpose identity verification for society.
The Accessibility and Equity Dimension
Digital identity systems create new forms of inequality. Studies show approximately 40% of people over 65 and about 25% of people earning less than $30,000 annually lack smartphones. If digital identification becomes standard or mandatory, these populations face significant barriers.
The ACLU has warned that legal requirements for digital ID would “further disadvantage marginalized communities” by creating technological gatekeeping around essential services and rights.
Additionally, the requirement for recent-model devices (iPhone 11 or later, Apple Watch Series 6 or later) creates economic barriers. Families that can’t afford cutting-edge technology get excluded from systems increasingly designed around assumption of device ownership.
Current Limitations and Implementation Challenges
Apple’s Digital ID faces practical obstacles beyond privacy concerns:
Inconsistent Acceptance: TSA checkpoint acceptance varies significantly across airports. Equipment malfunctions, inconsistent agent training, and policy variations between locations create unreliable experiences. Digital ID holders report sometimes presenting credentials successfully, other times needing physical documents when readers fail.
Deployment Ambiguity: The passport feature’s absence from iOS 26’s September release frustrated early adopters. Apple’s website no longer mentions requiring software updates, creating uncertainty about server-side activation versus point updates.
Limited Utility: Currently restricted to domestic TSA checkpoints, Digital ID offers minimal advantage over carrying physical identification. Until adoption expands significantly, users must carry traditional documents anyway.
Device Dependence: Dead batteries, broken phones, software glitches, or forgotten devices leave users unable to verify identity. Physical documents provide backup that digital-only systems lack.
What This Means for Privacy-Conscious Users
For individuals concerned about privacy, Apple’s Digital ID presents a complex calculation:
Convenience vs. Normalization: Using Digital ID may speed up airport security, but contributes to normalizing smartphone-based identity verification that could expand into constant identification requirements.
Better Than Alternatives: If digital identity becomes unavoidable, Apple’s privacy-preserving architecture is superior to centralized government databases or poorly secured third-party verification systems. However, this is choosing the least problematic option rather than a truly privacy-respecting solution.
Infrastructure Risk: Supporting Digital ID adoption builds infrastructure that could be repurposed for surveillance even if Apple’s current implementation is relatively privacy-protective.
Personal Threat Modeling: The right decision depends on individual circumstances. High-risk individuals—journalists, activists, lawyers, anyone with sensitive client information—face greater dangers from smartphone-based identity systems than average users.
Recommendations for Privacy Protection
For those choosing to use Apple’s Digital ID despite privacy concerns:
- Maintain Physical Backups: Always carry physical identification. Don’t become completely dependent on digital systems.2. Understand Biometric Vulnerabilities: Remember that Face ID and Touch ID can potentially be compelled by law enforcement in ways passcodes cannot. Know your legal rights regarding device access.3. Limit Scope Expansion: Resist pressure to use Digital ID for non-essential purposes. Each additional use case normalizes constant identification and expands tracking opportunities.4. Monitor Function Creep: Watch for Digital ID expanding beyond current airport security applications. Oppose regulations making digital identity mandatory for accessing services or content.5. Support Privacy Legislation: Advocate for comprehensive federal data privacy laws that would restrict how companies and government agencies can collect, use, and share identity information.6. Consider Alternatives: For those uncomfortable with digital identity systems, maintaining REAL ID-compliant physical documents remains an option—for now.
The Bigger Picture: A Watershed Moment for Digital Privacy
Apple’s Digital ID launch represents more than a convenient airport feature. It’s a watershed moment in the infrastructure being built for comprehensive digital identity verification.
As detailed in our analysis of Digital IDs and Personal Privacy: Navigating the Benefits and Risks, the fundamental tension is between efficiency and privacy. Digital identity systems promise streamlined processes and reduced fraud, but create unprecedented opportunities for surveillance, tracking, and control.
The broader pattern is unmistakable. From Australia’s mandatory Digital ID system to the UK’s proposed mandatory “Brit Card” to expanding age verification requirements across Europe, governments worldwide are constructing digital identity infrastructure that fundamentally reshapes the relationship between individuals and institutions.
Apple’s implementation may be more privacy-preserving than government-run alternatives, but it still contributes to normalizing constant digital identification. The infrastructure being built today will be difficult to dismantle tomorrow, and the privacy protections Apple promises can erode through regulatory changes, security breaches, or corporate policy shifts.
🎧 Related Podcast Episode
Conclusion: Proceed with Caution
Apple’s Digital ID is technically impressive and more privacy-conscious than many digital identity systems. For frequent travelers, it may offer genuine convenience. But that convenience comes with significant privacy trade-offs that extend far beyond individual user choices.
By making smartphone-based identity verification seamless and ubiquitous, Apple is accelerating the shift toward a future where constant identification becomes normalized. Once that infrastructure is established, restricting its scope or removing it becomes exponentially more difficult.
The question isn’t whether Apple’s current implementation protects privacy better than alternatives—it likely does. The question is whether we want to build infrastructure that makes comprehensive identity tracking technically feasible and socially acceptable, regardless of current privacy protections.
For privacy-conscious individuals, the calculus is personal. But for society, Apple’s Digital ID represents another step toward a world where anonymity and untracked movement become increasingly impossible—even when the tracking is done through encrypted, privacy-preserving systems.
The most important privacy protection isn’t technical—it’s the decision about whether to participate in digital identity systems at all.
For more analysis of digital identity systems and privacy threats, explore our coverage of global digital ID implementation, biometric database breaches, and the broader surveillance infrastructure being constructed worldwide.