Reddit Privacy Guide: Securing Your Presence in 2025
With over 430 million active users, Reddit remains a hub for niche communities and candid discussions. However, its public nature demands robust priva...
619 articles on data privacy, breach protection, and cybersecurity insights.

With over 430 million active users, Reddit remains a hub for niche communities and candid discussions. However, its public nature demands robust priva...

With over 200 million active users, Discord remains a hub for gaming, professional communities, and social interaction. However, its decentralized ser...

With over 140 million monthly active users, Twitch remains a hub for live streaming and community interaction. However, its open nature demands robust...

With over 2.7 billion monthly active users, YouTube remains a cornerstone of digital content consumption. However, its vast ecosystem demands meticulo...

Snapchat’s ephemeral messaging model and location-based features demand robust safety protocols to balance user engagement with privacy. This guide di...
With over 1.7 billion active users, TikTok’s blend of viral content and algorithmic curation demands robust privacy tools to protect users across age ...

Introduction In today's interconnected world, social media platforms have become integral to our daily lives, serving as spaces for personal expressio...
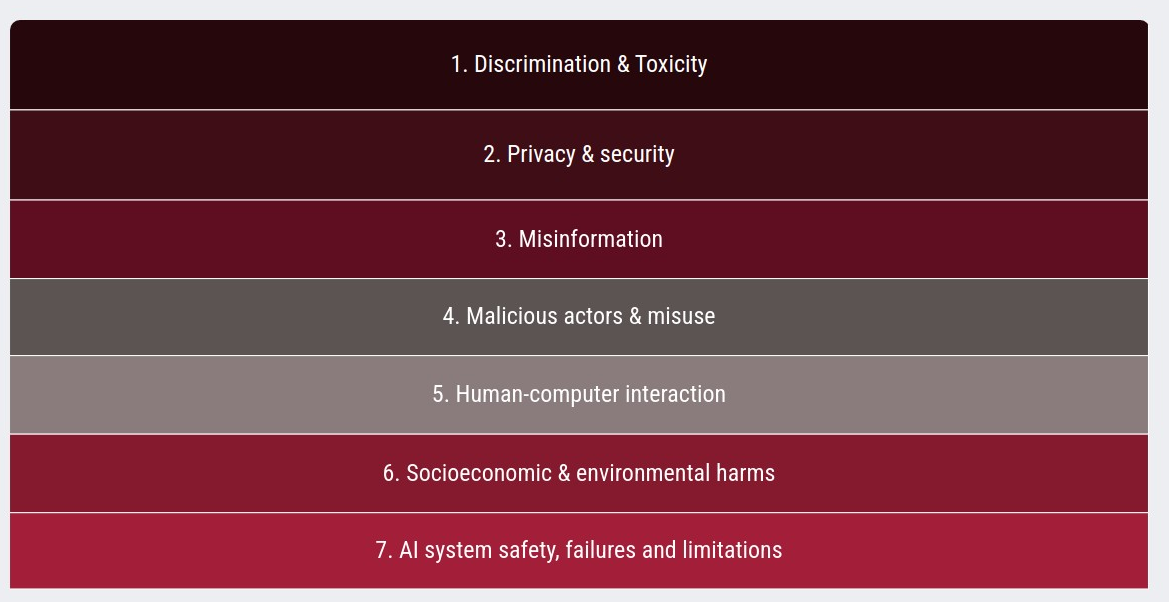
Artificial Intelligence (AI) poses risks of considerable concern to academics, auditors, policymakers, AI companies, and the public. An AI Risk Reposi...
Overview DeepSeek, an AI-powered platform, has come under investigation across multiple European Union countries due to concerns over data privacy, po...

US Defense Department employees accessed a Chinese AI startup's chatbot for two days before cybersecurity officials blocked the service, raising quest...

WhatsApp, the popular messaging platform owned by Meta, has successfully thwarted a hacking campaign that targeted approximately 90 users, including.....

In a significant shift in content moderation policies, Meta, the parent company of Facebook, Instagram, and other social media platforms, has announce...