Qwen2.5-Max: A New Contender in AI Performance Benchmarks
Introduction Alibaba's latest AI model, Qwen2.5-Max , is making waves in the artificial intelligence landscape with its impressive benchmark results. ...
619 articles on data privacy, breach protection, and cybersecurity insights.

Introduction Alibaba's latest AI model, Qwen2.5-Max , is making waves in the artificial intelligence landscape with its impressive benchmark results. ...

As technology companies continue to integrate artificial intelligence and data-driven features into their products, privacy concerns have become a maj...

In a groundbreaking lawsuit, Texas Attorney General Ken Paxton has accused Allstate Corporation of illegally collecting and monetizing drivers' person...

In January 2025, Apple agreed to a $95 million settlement to resolve a class-action lawsuit alleging that its voice assistant, Siri, had inadvertently...

Introduction For several years, the social media landscape has been buzzing with debates over the popular video-sharing platform TikTok. With over a b...

As we navigate 2025, the landscape of data privacy is undergoing significant transformations. Businesses and consumers alike must stay informed about ...
As artificial intelligence (AI) continues to evolve, it brings forth significant privacy challenges that both individuals and organizations must addre...

In an increasingly digital world, our smartphones have become indispensable tools for communication, navigation, and productivity. However, these devi...

As online interactions and digital services increasingly integrate into the everyday lives of children, concerns over the protection of their personal...

The sources, the Microsoft Digital Defense Report 2024 and the Unit 42 2024 Incident Response Report, paint a clear picture: the methods attackers use...

The recent legal and commercial battle between WordPress co-creator Matt Mullenweg and WP Engine has raised several privacy concerns, especially regar...
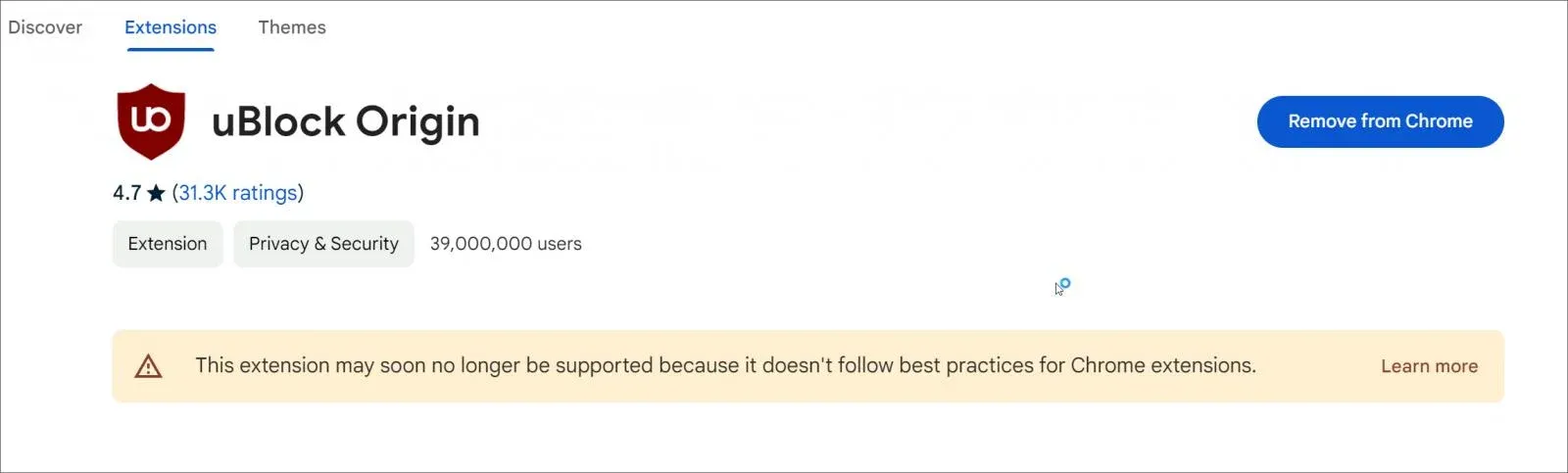
In recent years, uBlock Origin has become a go-to solution for millions of internet users who seek enhanced privacy and control over online ads. Howev...