How a “verified” VPN extension spied on 100,000+ users while Google demands identity verification from Android developers
Google has a problem. While the tech giant aggressively tightens its grip on Android app distribution by requiring developer verification for all apps—even those installed outside the Play Store—it continues to award coveted “verified” badges to Chrome extensions that are actively spying on millions of users.
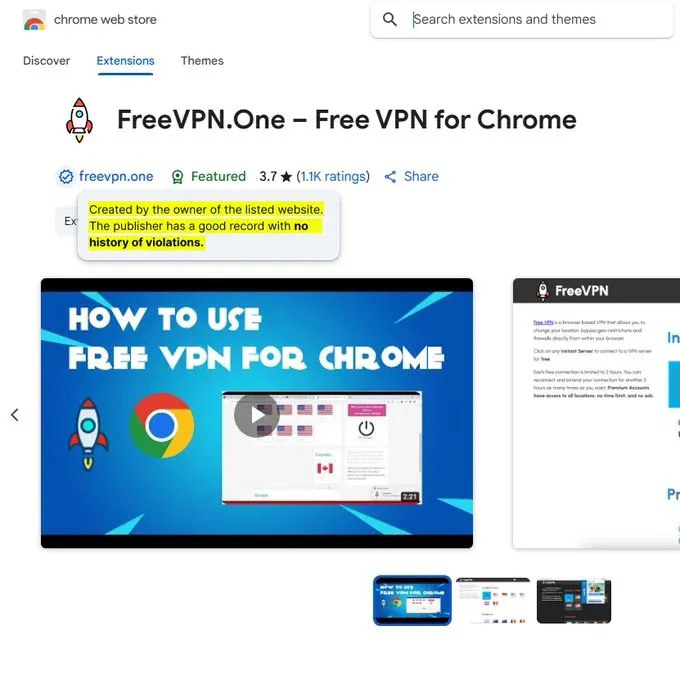
The contradiction became impossible to ignore when cybersecurity researchers recently exposed FreeVPN.One, a Chrome extension that had been screenshotting every website its users visited while proudly displaying Google’s “Featured” and “Verified” badges in the Chrome Web Store.
The FreeVPN.One Betrayal: When “Verified” Means Vulnerable
FreeVPN.One seemed like the perfect choice for privacy-conscious users. With over 100,000 downloads, hundreds of positive reviews, and Google’s official verification badges, it appeared to tick every box for a trustworthy browser extension. The reality was far more sinister.
According to a detailed investigation by cybersecurity firm Koi Security, the extension was operating as sophisticated spyware, automatically capturing screenshots of every webpage users visited within seconds of loading. These screenshots—containing everything from banking credentials and medical records to private photos and sensitive corporate data—were then uploaded to remote servers controlled by anonymous developers.
“Think about your own daily browsing like opening a Google Sheet with sensitive company information, logging into your bank account, browsing a dating app, or viewing private family photos,” the researchers noted. “Every one of those moments, captured as screenshots and shipped away without your consent.”
The most damning detail? Despite the extension’s privacy policy explicitly stating that it “does not collect any data about its users,” it was doing precisely the opposite—all while maintaining Google’s seal of approval.
A Pattern of Systematic Failure
FreeVPN.One isn’t an isolated incident. It’s part of a disturbing pattern that reveals fundamental flaws in Google’s Chrome Web Store security system.
Earlier this year, researchers uncovered the “Malicious11” campaign, where eleven Chrome extensions with verification badges infected over 1.7 million users. More recently, the “RedDirection” campaign exposed 18 malicious extensions across Chrome and Edge that compromised 2.3 million users, many carrying verification badges and featured placements.
What makes these campaigns particularly insidious is their methodology. These extensions don’t start out malicious—they operate legitimately for months or even years, building trust and accumulating positive reviews. Then, through routine automatic updates that install silently without user interaction, they transform into surveillance tools.
“No phishing. No social engineering. Just trusted extensions with quiet version bumps that turned productivity tools into surveillance malware,” researchers explained.
The verification system that users rely on to identify safe extensions has become a weapon against them. Google’s automated scans, human reviews, and behavioral monitoring—the very safeguards meant to protect users—have repeatedly failed to catch sophisticated malware that often operates for months before detection.
Android: The Iron Fist Approach
While Chrome extensions continue to spy on millions with Google’s blessing, the company is taking a radically different approach to Android app security. Starting in October 2025, Google will require all Android app developers to verify their identities—not just those publishing through the Play Store, but anyone creating apps for the platform, including those distributed through sideloading.
The new policy will roll out gradually, becoming mandatory in select regions by September 2026, with broader global expansion expected starting in 2027. The justification? Google’s research showing that apps downloaded outside the Play Store are over 50 times more likely to contain malware.
“This isn’t about malware. This is about de-anonymizing the internet,” one critic observed. “This is yet more censorship and control disguised as for our ‘safety’. It’s our phone, not Google or Apple’s.”
The Double Standard Exposed
The contrast is striking. On Android, Google demands identity verification from every developer—including hobbyists creating free apps and students working on non-commercial projects. Yet in the Chrome Web Store, extensions developed by anonymous entities behind suspicious domains can obtain verification badges while actively harvesting sensitive user data.
Consider the scope of the threat: recent studies suggest that over 50% of browser extensions present a high security risk—a figure that rivals or exceeds the Android threat level Google uses to justify its platform lockdown. Yet browser extensions receive a fraction of the scrutiny applied to Android apps.
The timing makes the contradiction even more glaring. Google’s Android crackdown comes just weeks after expanding YouTube’s controversial AI age-estimation system to the US, leading critics to argue that the company is “steadily tightening its grip on the open internet.”
Why This Matters More Than You Think
This isn’t just about technical policy—it’s about trust and user safety. When Google awards verification badges to malicious extensions, it’s not just failing to protect users; it’s actively making them less safe by encouraging downloads of harmful software.
The FreeVPN.One case perfectly illustrates this problem. Users who did their due diligence—checking for verification badges, reading reviews, and choosing extensions with high download counts—were actually more likely to install the malicious software because of Google’s endorsement.
“Even if someone did the proper research on which extensions to trust, every extension can turn malicious at any moment,” security researchers warn.
The Broader Implications
Google’s selective approach to security reveals troubling priorities. While positioning itself as protecting user safety through increasingly strict controls on Android, it operates a Chrome extension marketplace where verified malware can thrive for months or years.
This raises fundamental questions about Google’s commitment to user security versus platform control. The company that demands identity verification from Android hobbyists apparently sees no problem awarding trust badges to anonymous surveillance operations.
For enterprise users, the implications are particularly serious. Employees who install “verified” extensions for personal use can inadvertently expose sensitive corporate data, creating security risks that traditional IT monitoring might miss.
Protecting Yourself in an Untrustworthy System
Given the systematic failures in Google’s verification process, users need to take extra precautions:
Immediate Actions:
- Audit your installed Chrome extensions and remove any you don’t absolutely need- Pay special attention to VPN extensions, color pickers, and productivity tools—categories frequently targeted by malware campaigns- Clear your browser data if you’ve used potentially compromised extensions- Run a full system malware scan- Change passwords for sensitive accounts, especially if you accessed them while suspicious extensions were installed
Ongoing Security Practices:
- Treat verification badges as meaningless—they provide no real security assurance- Research extension developers thoroughly, looking for legitimate company profiles and contact information- Be suspicious of extensions that request broad permissions like access to all websites- Monitor extension update notifications and investigate significant permission changes- Consider using dedicated security tools instead of browser extensions for sensitive functions like VPN services
The Need for Accountability
The FreeVPN.One scandal and similar incidents highlight the urgent need for meaningful reform in how browser extension marketplaces operate. Google’s current system—which prioritizes automated processing at scale over thorough security review—has repeatedly failed users.
The company’s response to these revelations will be telling. Will Google implement more rigorous verification processes that actually verify security, or will it continue to prioritize the appearance of safety over genuine protection?
🎧 Related Podcast Episode
Conclusion: Trust, But Verify Everything
Google’s security double standard reveals a troubling truth: the company’s verification systems cannot be trusted as genuine indicators of safety. While demanding unprecedented control over Android app distribution in the name of security, Google continues to operate a Chrome extension marketplace that actively endangers users through misleading trust signals.
For users, the lesson is clear: verification badges, high download counts, and positive reviews are no guarantee of safety. In a digital ecosystem where even “verified” privacy tools can be surveillance operations, skepticism isn’t paranoia—it’s survival.
The next time you see a Chrome extension with Google’s verification badge, remember FreeVPN.One. That badge might not be protecting you—it might be the very thing putting you at risk.
Have you been affected by malicious browser extensions? Share your experience in the comments below, and don’t forget to audit your Chrome extensions today—your privacy might depend on it.



