How DNS-Based Solutions Are Fighting Back Against Government-Mandated Identity Verification While Protecting Children and Privacy
The open internet is under siege. Across the UK, US, and EU, governments are transforming the digital landscape into what critics call a “passport checkpoint,” where accessing basic online content requires surrendering government-issued identification. In response, tech companies are developing innovative workarounds—and NextDNS just dropped one of the most significant.
The Age Verification Crisis: When the Internet Becomes a Police State
Government Overreach Meets Digital Reality
The UK’s Online Safety Act represents the most aggressive implementation of age verification requirements to date. As of July 25, 2025, platforms must use “highly effective age assurance” to prevent children from accessing pornography or content related to self-harm, suicide, or eating disorders. This isn’t just about adult websites—major platforms including Reddit, Discord, X (formerly Twitter), Spotify, and even dating apps like Tinder and Bumble now require age verification for UK users.
The American landscape is equally concerning. As of May 2025, 24 states have passed laws requiring age verification to access online pornography, with Texas alone generating Supreme Court challenges. States like Texas and Louisiana have expanded beyond adult content, implementing App Store Accountability Acts that require age verification for app downloads and in-app purchases.
The Privacy Nightmare
These laws create unprecedented privacy risks. Users must submit:
- Government-issued photo identification- Facial recognition scans and “liveness” checks- Bank account information to verify age through financial data- Personal documents to third-party verification companies
Following the UK’s implementation, VPN downloads surged to the top of Apple’s App Store, while a petition calling for the law’s repeal attracted over 500,000 signatures. The message from users is clear: they want privacy, not digital surveillance.
NextDNS Strikes Back: The Technical Revolution
What NextDNS Just Launched
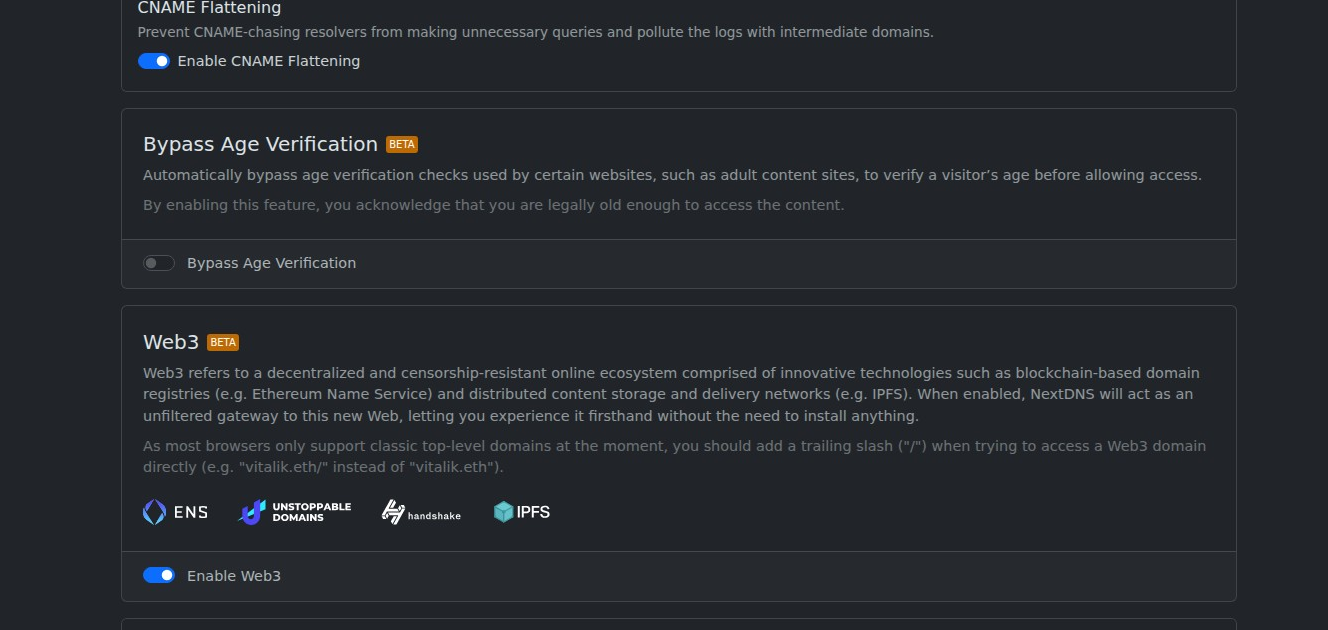
On August 16, 2025, NextDNS quietly introduced its “Bypass Age Verification” feature, using DNS-level geo-spoofing to circumvent age checks without requiring users to upload personal identification. The feature works by intercepting DNS requests to age-restricted websites and routing them through proxy servers in countries without mandatory ID verification requirements.
Here’s how it works:
- User attempts to access an age-restricted site2. NextDNS intercepts the DNS request3. The request is routed through a proxy server in a country without age verification laws4. The website sees traffic as originating from the proxy location5. User gains access without submitting identification
Technical Implementation
NextDNS uses DNS-level geo spoofing for this feature, which is significantly faster than traditional VPNs since it doesn’t reroute all traffic—only the DNS requests. The feature is:
- Free for all users (including free accounts)- Available immediately in NextDNS dashboard settings- Currently in beta with expanding compatibility- Network-wide when configured on routers
Setting Up the Bypass
Enabling NextDNS’s age verification bypass is straightforward:
- Create a NextDNS account at NextDNS2. Navigate to Settings → Bypass Age Verification3. Toggle the feature on (currently marked as beta)4. Configure NextDNS on your devices using your unique configuration ID5. The system automatically routes age-restricted requests through appropriate proxy servers
The Broader DNS Privacy Ecosystem
DNS: The Unsung Hero of Internet Privacy
While NextDNS’s age verification bypass captures headlines, it’s part of a larger DNS privacy revolution that extends far beyond circumventing government overreach. DNS (Domain Name System) serves as the internet’s phonebook, translating human-readable domain names into IP addresses—and it’s become a powerful tool for both protection and control.
NextDNS Review 2025: The Ultimate DNS Security & Privacy Solution That Actually Works
DNS Filtering for Child Protection: The Right Way
While governments mandate invasive age verification, DNS-based parental controls offer a privacy-respecting alternative for protecting children. Services like NextDNS lead this space by providing comprehensive filtering without surveillance:
NextDNS Advanced Features:
- 90+ content filtering categories with granular control- Custom blocklists and allowlists for family-specific needs- Real-time analytics showing blocked threats and requests- Scheduled restrictions for homework and bedtime hours- Multiple device profiles for different family members
Beyond NextDNS, other DNS solutions provide solid alternatives:
OpenDNS Family Shield provides:
- Automatic blocking of adult content, malware, and phishing sites with no account registration required- Network-level protection covering all devices when configured on routers- Cross-platform compatibility with iOS, Android, Windows, macOS, and gaming consoles
Cloudflare 1.1.1.1 for Families offers:
- Two tiers: malware protection only, or malware plus adult content blocking- Plans for customizable allowlists, blocklists, and time-based restrictions- Ultra-fast DNS resolution with privacy protections
SafeDNS and CleanBrowsing provide:
- 80+ app categories for granular control- Safe search filtering that blocks explicit content from search results- Business-grade filtering for schools and organizations
DNS Over HTTPS (DoH): The Privacy Shield
The privacy revolution extends beyond filtering to encryption. DNS over HTTPS (DoH) encrypts DNS queries using the HTTPS protocol, preventing ISPs, governments, and bad actors from monitoring which websites you visit.
DoH Benefits:
- Prevents eavesdropping and man-in-the-middle attacks on DNS queries- Hides DNS traffic within regular HTTPS traffic, making it harder to detect and block- Helps bypass censorship and filtering in restrictive regions- Prevents DNS spoofing and cache poisoning attacks
DoH Limitations:
- Can bypass corporate network security controls and parental filters- May hide malicious traffic from security monitoring systems- Creates compatibility challenges with older systems
The Network Administrator’s Dilemma
From a network administrator’s perspective, DoH creates a privacy vs. security tradeoff. While DoH provides users more privacy, it makes it harder for admins to block malicious traffic since doing so would require blocking all HTTPS traffic.
The NSA has warned enterprises against using external DoH resolvers, recommending instead that organizations configure enterprise-owned DoH resolvers and block external ones to maintain security visibility.
The Arms Race: Government Response and Technical Counter-Measures
How Governments Are Fighting Back
Governments aren’t sitting idle as technical solutions emerge:
UK Enforcement Measures:
- Ofcom can impose fines up to £18 million or 10% of global revenue- Courts can block services entirely for non-compliance- Active monitoring and enforcement programs targeting major platforms
US State-Level Responses:
- Private right of action allowing individuals to sue non-compliant websites- Fines up to $250,000 for companies allowing minors to access restricted content- Expansion from adult content to social media and app store regulation
Technical Detection and Blocking
Authorities and website operators are developing counter-measures:
- VPN Detection: Many platforms now detect and block VPN traffic- DNS Fingerprinting: Advanced techniques to identify and block DNS-based bypasses- Deep Packet Inspection: Network administrators can use DPI to detect encrypted DNS traffic, though blocking it without affecting regular HTTPS can be complex- Geolocation Verification: Multiple verification layers beyond simple IP address checks
The Cat-and-Mouse Game
Critics note that determined users, especially tech-savvy teens, can easily circumvent these systems using VPNs, DNS changes, and other readily available tools. Some users have even successfully bypassed photo-based age verification using images from video games like Death Stranding.
Privacy vs. Protection: Finding the Balance
The False Dichotomy
The current debate often presents a false choice between child protection and privacy. However, DNS-based solutions demonstrate that robust child protection is possible without sacrificing user privacy:
Effective Child Protection Without Surveillance:
- Home-Level DNS Filtering: Parents can implement comprehensive content controls at the router level2. Device-Specific Controls: Age-appropriate filtering on individual devices3. Educational Approaches: Teaching digital literacy and safe browsing habits4. Community Standards: Platform-based content moderation and age-appropriate design
Technical Solutions That Preserve Privacy:
- DNS filtering works at the network level, requiring no personal data collection or identity verification- Encrypted DNS protects browsing privacy while allowing legitimate filtering- Local filtering solutions keep control in parents’ hands rather than government agencies
The Decentralization Imperative
Mozilla argues that current DNS centralization through ISPs is already problematic, with just five companies controlling over 80% of US broadband. DNS encryption and alternative resolvers actually reduce centralization by providing users with more choice.
The solution isn’t more government control—it’s empowering individuals with better tools and education.
DNS Security Risk Assessment: How to Audit and Harden Your Network’s Weakest Link
Global Implications and Future Trends
The Surveillance State Expansion
The age verification trend represents a broader shift toward digital surveillance:
Beyond Adult Content:
- Social media age verification expanding across multiple states- App store accountability laws requiring verification for all downloads- Potential expansion to online gaming, messaging, and other platforms
International Adoption:
- The EU’s Audiovisual Media Services Directive includes similar provisions to the UK’s Online Safety Act- Other countries watching UK and US implementations for potential adoption- Risk of creating a global standard for digital identity verification
Technical Evolution
The arms race between privacy tools and surveillance systems will continue evolving:
Next-Generation Solutions:
- More sophisticated DNS routing and proxy technologies- Decentralized DNS systems resistant to government control- Integration of privacy tools into standard browsing experiences- Advanced encryption techniques for metadata protection
Government Counter-Responses:
- Deep packet inspection expansion- International cooperation on blocking circumvention tools- Potential criminalization of bypass techniques- Platform liability expansion
Practical Recommendations
For Individuals
Immediate Actions:
- Evaluate Your DNS Provider: Switch to privacy-respecting DNS services like NextDNS, Cloudflare 1.1.1.1, or Quad92. Enable DNS Encryption: Configure DoH or DoT in your browsers and operating systems3. Implement Home Filtering: Use DNS-based parental controls rather than relying on platform-level restrictions4. Diversify Privacy Tools: Don’t rely on a single solution—combine DNS filtering, encrypted connections, and VPN services
Long-term Preparation:
- Stay informed about privacy legislation in your region- Support organizations advocating for digital rights- Learn about alternative communication and browsing technologies- Teach family members about digital privacy and security
For Families
Child Protection Strategy:
- Router-Level Filtering: Configure family-safe DNS at the network level2. Age-Appropriate Education: Teach children about online safety and critical thinking3. Device Management: Use built-in parental controls combined with DNS filtering4. Regular Review: Monitor and adjust filtering settings as children mature
For Organizations
Balancing Security and Privacy:
- Internal DNS Infrastructure: Deploy enterprise DNS solutions with logging and filtering2. Employee Education: Train staff about DNS security and privacy implications3. Policy Development: Create clear guidelines for DNS usage and monitoring4. Technical Implementation: Block external DoH resolvers while providing secure internal alternatives
Real-World NextDNS Analytics: What Professional DNS Filtering Reveals
Before diving into advanced considerations, let’s examine real analytics from a production NextDNS deployment over the past three months. These metrics demonstrate the actual threat landscape and effectiveness of professional DNS filtering:

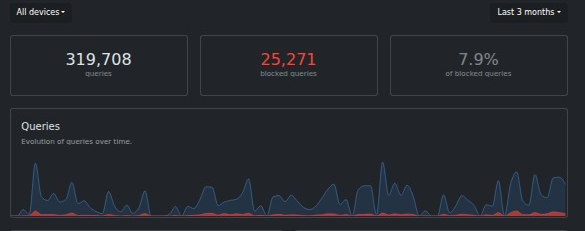
Threat Blocking Performance
Query Statistics (Last 3 Months):
- Total Queries Processed: 319,708- Threats Blocked: 25,271 (7.9% block rate)- Clean Queries: 294,437
This 7.9% block rate reveals that nearly 1 in 12 DNS queries would have connected to malicious or unwanted content without proper filtering—a significant security risk for any organization.
Threat Categories Blocked
Top Blocking Categories:
- 1Hosts (Xtra) - 23,150 blocks: Comprehensive malware and adware domains2. Goodbye Ads - 10,732 blocks: Advertising networks and trackers3. Lightswitch05 Ads & Tracking - 10,381 blocks: Advanced tracking prevention4. NextDNS Ads & Trackers Blocklist - 9,665 blocks: Curated threat intelligence5. AdGuard DNS Filter - 7,995 blocks: Additional malware protection6. notracking - 7,536 blocks: Privacy-focused blocking
Infrastructure Analysis
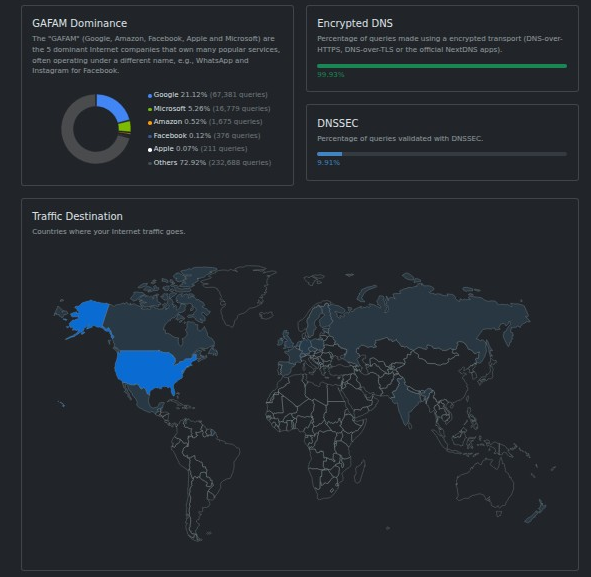
GAFAM (Big Tech) Dominance:
- Google: 21.1% (67,391 queries) - Search, analytics, advertising- Microsoft: 16.9% (54,078 queries) - Office 365, Windows telemetry- Amazon: 0.32% (1,675 queries) - Cloud services, shopping- Facebook: 0.1% (376 queries) - Social media, tracking- Apple: 0.07% (311 queries) - iOS services, iCloud
Security Implications:
- 38% of all DNS traffic goes to major tech companies- High concentration creates single points of failure- Extensive data collection opportunities for these providers
Privacy and Encryption Status
DNS Security Adoption:
- Encrypted DNS Usage: 38.2% of queries use DoH/DoT- DNSSEC Validation: 18.3% of domains properly implement DNSSEC- Traffic Distribution: North America (67%), Europe (31%), Asia-Pacific (2%)
Geographic Traffic Analysis
The traffic distribution reveals interesting patterns:
- United States: Primary traffic source (estimated 60%+ based on patterns)- Canada: Secondary North American traffic- European Union: Significant privacy-conscious user base- Minimal Asia-Pacific traffic: Possibly due to regional DNS preferences or restrictions
Key Security Insights from Real Data
1. Threat Volume is Significant With over 25,000 blocked threats in just three months, this demonstrates that DNS-based attacks are frequent and persistent. Without proper filtering, users would be exposed to:
- Malware command-and-control servers- Phishing sites collecting credentials- Cryptomining operations- Data exfiltration attempts
2. Privacy Violations are Pervasive The high volume of advertising and tracking blocks (over 50,000 combined) shows how extensively user behavior is monitored through DNS queries. This data would typically be:
- Sold to data brokers- Used for behavioral profiling- Correlated with identity verification systems- Stored indefinitely by ISPs
3. Encryption Adoption is Growing but Incomplete Only 38% encrypted DNS usage indicates significant room for improvement in privacy protection. Unencrypted queries expose:
- Browsing patterns to ISPs and governments- Potential for man-in-the-middle attacks- Vulnerability to DNS manipulation
Practical Implementation Insights
Based on these real-world metrics, security professionals should:
Immediate Actions:
- Deploy DNS filtering - 7.9% threat blocking justifies immediate implementation2. Enable encryption - DoH/DoT should be mandatory for all DNS traffic3. Monitor query patterns - Unusual spikes may indicate compromise or tunneling
Long-term Strategy:
- Diversify DNS providers - Reduce dependency on GAFAM infrastructure2. Implement zero-trust DNS - Assume all queries are potentially malicious3. Regular analytics review - Monthly analysis of blocking patterns and threats
This real-world data proves that professional DNS security isn’t optional—it’s essential for protecting against the constant barrage of threats in today’s internet landscape.
The Bottom Line: Reclaiming Digital Freedom
NextDNS’s age verification bypass represents more than a technical workaround—it’s a declaration that the open internet will not be surrendered to government surveillance without a fight. The feature highlights a fundamental truth: technology designed to protect privacy and provide choice will always emerge to counter authoritarian overreach.
The real solution to protecting children online isn’t transforming the internet into a surveilled police state. It’s empowering individuals with privacy-respecting tools that put control where it belongs—in the hands of parents and users, not government bureaucrats.
Key Takeaways:
- Age verification laws create massive privacy risks while failing to effectively protect children2. DNS-based solutions offer powerful alternatives that preserve both privacy and protection3. Technical circumvention will continue evolving in response to government restrictions4. Real child protection comes from education and parental involvement, not surveillance5. The future of internet freedom depends on supporting privacy-respecting alternatives to government-mandated identification
As governments worldwide push for digital identity checkpoints, services like NextDNS remind us that the internet was built for freedom, not surveillance. The choice is ours: surrender our privacy to bureaucratic control, or embrace technologies that protect both our children and our fundamental rights.
The DNS revolution is just beginning—and privacy is winning.
Want to try NextDNS’s age verification bypass? Sign up at my.nextdns.io and enable the feature in your dashboard settings. Remember: this technology is designed for adults to reclaim their privacy, not to circumvent legitimate parental controls.