Identity theft has evolved from opportunistic crimes into a sophisticated criminal enterprise affecting millions of people annually. According to recent FTC data, there were over 1.1 million reports of identity theft in 2024, with overall fraud losses exceeding $12.5 billion—a staggering 25% increase from the previous year. What makes this crisis particularly alarming is that most victims don’t discover the theft until months after criminals have already caused significant damage to their financial lives and credit histories.
The challenge isn’t just the scale of identity theft—it’s the sophistication of modern attacks that exploit multiple vulnerabilities simultaneously. Today’s identity thieves combine traditional methods like mail theft and dumpster diving with advanced digital techniques including social media reconnaissance, data broker exploitation, and social engineering attacks that can deceive even security-conscious individuals.
This comprehensive guide provides evidence-based strategies to assess your identity theft risk, implement proportional protection measures, and create early warning systems that detect threats before they become devastating losses. Whether you’re concerned about basic identity protection or need advanced strategies for high-risk situations, these proven techniques will dramatically strengthen your identity security posture.
Understanding Your Identity Threat Landscape
Modern identity theft operates across multiple attack vectors that most people never consider. Criminals don’t just steal wallets or intercept mail—they systematically gather information from dozens of sources to build comprehensive identity profiles that can bypass traditional security measures.
Identity Threat Detection Calculator | Assess Your Risk
The Eight Critical Identity Security Categories:
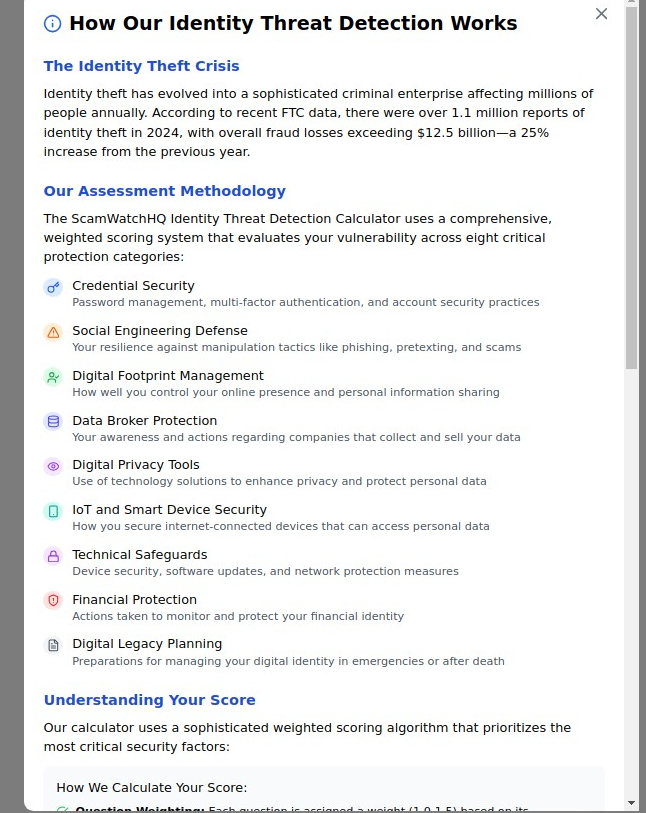
Our research analyzing thousands of identity theft cases reveals that comprehensive protection requires addressing vulnerabilities across eight critical categories. Each category represents a different attack surface that criminals exploit, and weakness in any area can compromise your entire identity security strategy.
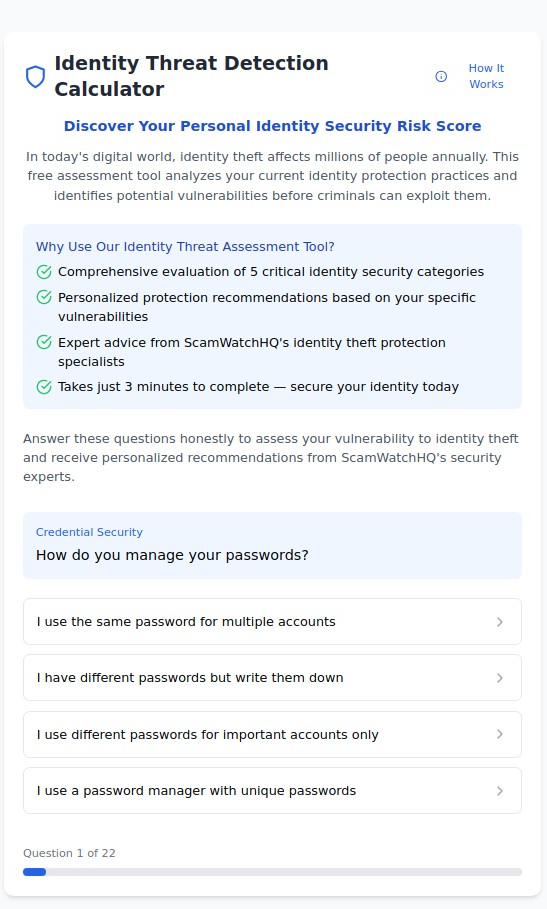
**Take our free **Identity Threat Detection Calculator to discover your specific vulnerabilities across all eight categories and receive personalized protection recommendations from our identity theft prevention specialists.
1. Credential Security: Your First Line of Defense
The Risk: Password reuse, weak authentication, and poor credential management create the most common entry points for identity thieves. Over 80% of data breaches involve compromised credentials that criminals purchase from dark web marketplaces.
Protection Strategies:
- Deploy unique passwords for every account using enterprise-grade password managers- Implement multi-factor authentication with authenticator apps (never SMS-based verification)- Regularly audit account security through credential monitoring services- Use hardware security keys for high-value financial and email accounts
Advanced Credential Protection: For high-risk individuals such as those with significant social media presence or public-facing influencer activities, additional credential security measures become essential. Consider using separate credential systems for personal versus professional accounts, implementing regular password rotation schedules, and deploying advanced threat monitoring for unauthorized access attempts.
The Complete Guide to Digital Privacy Protection: Your Comprehensive Toolkit for 2025
2. Social Engineering Defense: Protecting Against Manipulation
The Risk: Social engineering attacks exploit human psychology to trick victims into revealing sensitive information or performing actions that compromise their security. These attacks often combine information gathered from social media, public records, and data brokers to create convincing impersonation attempts.
Protection Strategies:
- Develop verification protocols for unexpected requests for sensitive information- Limit personal information sharing across all digital platforms- Train family members to recognize common social engineering tactics- Implement communication security protocols for financial and medical decisions
Cross-Platform Vulnerability Assessment: Social engineering attacks often combine information from multiple sources. Criminals might use OSINT techniques to gather background information, then exploit social media oversharing to create convincing pretexts. For high-net-worth individuals with luxury assets like yachts or private aviation access, social engineering risks increase significantly due to the higher potential payoff for criminals.
3. Digital Footprint Management: Controlling Your Online Presence
The Risk: Excessive personal information exposure through social media, public records, and data broker sites creates detailed profiles that identity thieves use for account takeovers and social engineering attacks.
Protection Strategies:
- Conduct regular audits of your online presence across all platforms and databases- Implement data broker removal services to eliminate personal information from people-search sites- Configure strict privacy settings across all social media platforms- Monitor search results for your name and personal information
Specialized Digital Footprint Concerns: Different lifestyles create unique digital footprint risks. Content creators and influencers face heightened exposure risks due to their public-facing activities, while individuals with private aircraft ownership or luxury yacht assets may appear in specialized databases that criminals specifically target for high-value identity theft schemes.
Identity Threat Detection Calculator | Assess Your Risk
4. Data Broker Protection: Limiting Commercial Surveillance
The Risk: Data brokers collect and sell personal information from hundreds of sources, creating detailed profiles available to anyone willing to pay. These profiles often include current and former addresses, phone numbers, email addresses, family member information, and even financial indicators.
Protection Strategies:
- Identify and opt out of major data broker databases systematically- Use privacy-focused services for new account registrations and purchases- Implement address privacy techniques for high-risk situations- Monitor data broker sites regularly for reappearance of your information
Data Broker Removal Services: Professional data removal services can handle the complex and time-consuming process of removing your information from hundreds of data broker sites. For individuals requiring enhanced privacy protection—such as those with significant social media followings or high-value assets—comprehensive data broker removal becomes a critical security investment.
5. Digital Privacy Tools: Technology-Enhanced Protection
The Risk: Inadequate use of privacy-enhancing technologies leaves digital communications, financial transactions, and personal data vulnerable to interception and analysis by both criminals and unwanted surveillance.
Protection Strategies:
- Deploy VPN services for all internet communications- Use encrypted messaging and email services for sensitive communications- Implement privacy-focused browsers and search engines- Configure device-level privacy settings to limit data collection
Comprehensive Privacy Tool Integration: Effective digital privacy requires coordinated tool deployment across multiple platforms and devices. Our personal privacy tools guide provides detailed implementation strategies, while our social media privacy protection offers platform-specific configurations that complement broader digital privacy tools.
6. IoT and Smart Device Security: Protecting Connected Assets
The Risk: Internet-connected devices often lack robust security measures and can provide entry points for criminals to access home networks, personal information, and even physical security systems.
Protection Strategies:
- Implement network segmentation to isolate IoT devices from critical systems- Regularly update firmware and security settings on all connected devices- Use strong authentication for smart home and security systems- Monitor network traffic for unauthorized device communications
Luxury Asset Digital Security: High-net-worth individuals face unique IoT security challenges. Modern yachts contain sophisticated connected systems that can be vulnerable to cyber attacks, while private aircraft increasingly rely on connected navigation and communication systems that require specialized security considerations.
Identity Threat Detection Calculator | Assess Your Risk
7. Technical Safeguards: Advanced Security Measures
The Risk: Inadequate technical security measures leave devices, networks, and accounts vulnerable to sophisticated attacks that can bypass basic security controls.
Protection Strategies:
- Deploy endpoint detection and response tools on all devices- Implement network monitoring and intrusion detection systems- Use encrypted storage for all sensitive information- Maintain regular security assessments and vulnerability scanning
Professional-Grade Security Implementation: Individuals with elevated risk profiles—including public figures and content creators—often require enterprise-level security measures typically deployed by corporations. This includes advanced threat monitoring, professional security assessments, and specialized incident response capabilities.
8. Financial Protection: Securing Your Economic Identity
The Risk: Identity thieves increasingly target financial accounts, investment portfolios, and credit profiles to steal funds directly or establish credit in victims’ names for long-term financial exploitation.
Protection Strategies:
- Implement credit monitoring across all three major credit bureaus- Use credit freezes to prevent unauthorized account openings- Monitor financial accounts daily for unauthorized transactions- Establish fraud alerts and account notifications for all sensitive activities
Enhanced Financial Protection for High-Risk Individuals: Individuals with complex financial profiles, multiple accounts, or significant assets require enhanced financial protection strategies. This includes private banking security measures, advanced investment account monitoring, and specialized identity theft insurance coverage that addresses high-value loss scenarios.
9. Digital Legacy Planning: Protecting Your Identity Beyond Life
The Risk: Inadequate planning for digital asset management and identity protection after death can leave family members vulnerable to identity theft using deceased persons’ information, while valuable digital assets may become inaccessible.
Protection Strategies:
- Create comprehensive digital asset inventories with access instructions- Implement secure digital estate planning with trusted family members or advisors- Establish clear protocols for account closure and digital identity management- Use specialized digital legacy services for complex asset portfolios
Comprehensive Identity Risk Assessment: Understanding Your Vulnerability Profile
Most people dramatically underestimate their identity theft risk because they focus on obvious vulnerabilities while ignoring sophisticated attack vectors that criminals increasingly exploit. Effective identity protection starts with honest assessment of your current practices and exposure level across all critical security categories.
**Complete our **Identity Threat Detection Calculator to receive a comprehensive evaluation of your identity security posture. This advanced assessment tool analyzes your vulnerability across all eight critical protection categories and provides personalized recommendations based on your specific risk profile and lifestyle factors.
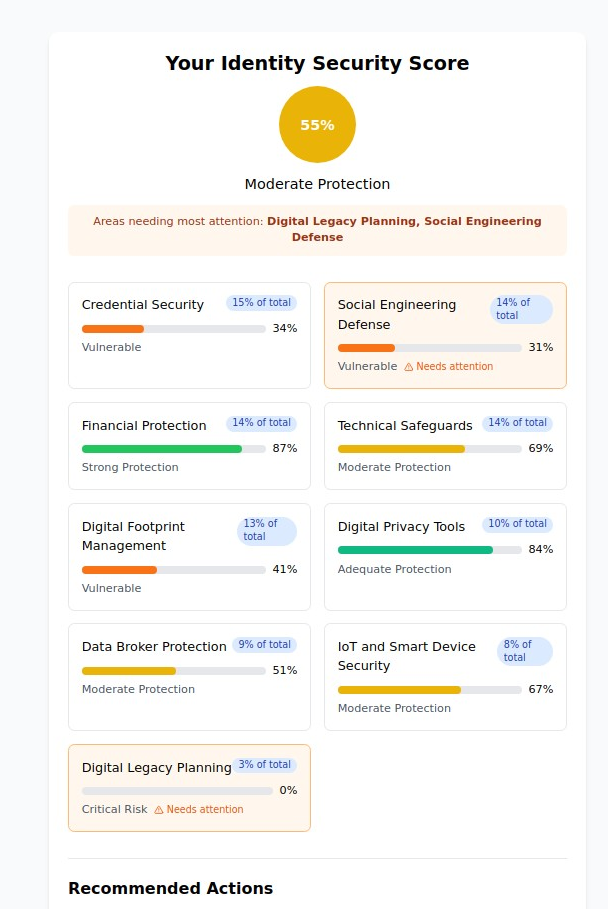
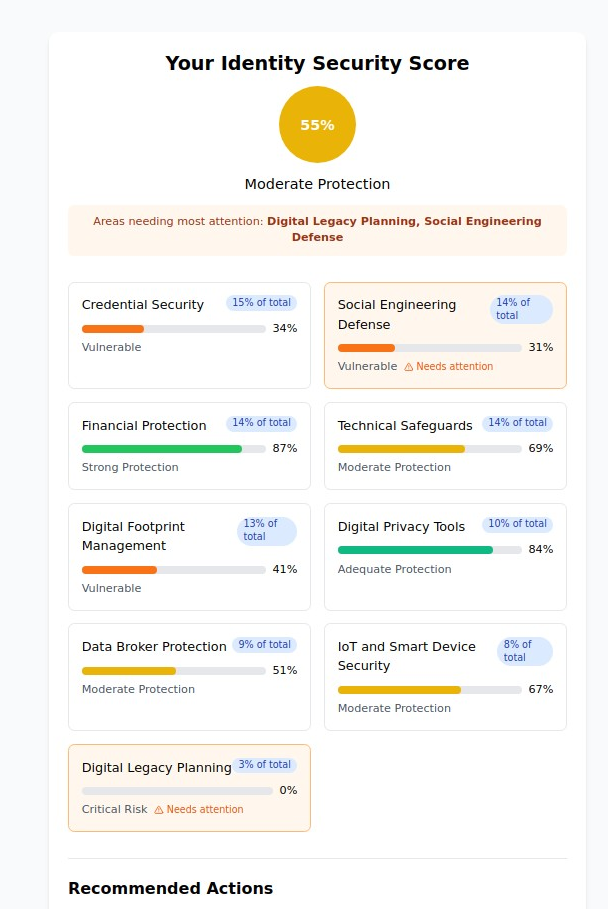
Understanding Your Identity Security Score
Our assessment methodology uses a sophisticated weighted scoring system that prioritizes the most critical security factors based on real-world identity theft patterns and criminal exploitation techniques. Unlike generic checklists, our calculator evaluates your specific vulnerability profile and provides actionable recommendations tailored to your situation.
Score Interpretation Guidelines:
85-100% (Strong Protection): You maintain excellent identity security practices across most critical categories. Focus on maintaining current protections and staying updated on emerging threats.
65-84% (Moderate Protection): You have solid foundational security but significant gaps in several critical areas. Prioritize the highest-risk vulnerabilities first.
45-64% (Basic Protection): Your current practices provide minimal protection against sophisticated identity theft attacks. Immediate action across multiple categories is essential.
Below 45% (High Risk): Your identity security posture leaves you extremely vulnerable to multiple types of attacks. Comprehensive security overhaul is urgently needed.
Personalized Protection Roadmaps
Based on your assessment results, you’ll receive customized protection strategies that address your specific vulnerabilities and lifestyle factors. Our recommendations consider your unique risk profile, including:
- Professional Exposure: Public-facing careers or high-visibility positions that increase targeting risk- Asset Complexity: Luxury assets, private aviation, or complex financial portfolios- Digital Presence: Social media usage patterns and online visibility levels- Technical Sophistication: Current security tool usage and technical implementation capabilities
Identity Monitoring and Early Warning Systems
Proactive identity monitoring provides crucial early warning when criminals begin exploiting your personal information. Rather than discovering identity theft months after the damage occurs, comprehensive monitoring systems can detect suspicious activity within hours or days of initial criminal access.
Credit Monitoring: Beyond Basic Services
Most people rely on basic credit monitoring that only detects hard credit inquiries and new account openings. Comprehensive credit protection requires monitoring across multiple categories:
Essential Credit Monitoring Components:
- Real-time monitoring across all three credit bureaus (Experian, Equifax, TransUnion)- Soft credit inquiry monitoring for account review and pre-approval activities- Public record monitoring for court judgments, bankruptcies, and liens- Address change monitoring to detect unauthorized contact information updates
Advanced Credit Protection Strategies:
- Credit freezes on all three bureaus (free and highly effective)- Fraud alerts for additional verification requirements on new accounts- Specialized monitoring for business credit profiles and professional licenses- International credit monitoring for individuals with overseas financial exposure
Dark Web Monitoring: Detecting Compromised Information
Criminals often sell stolen personal information on dark web marketplaces months before using it for identity theft. Dark web monitoring can provide early warning when your information appears in criminal databases.
Critical Information Categories to Monitor:
- Social Security numbers and government identification numbers- Credit card and bank account information- Email addresses and account credentials- Driver’s license and passport information- Medical information and insurance details
Financial Account Monitoring: Real-Time Fraud Detection
Daily monitoring of financial accounts provides the fastest detection of identity theft in progress. Modern monitoring systems can detect suspicious patterns that human review might miss.
Advanced Financial Monitoring Techniques:
- Real-time transaction alerts for all account activity- Velocity monitoring for unusual spending patterns- Geographic monitoring for out-of-area account usage- Merchant category monitoring for suspicious purchase types- Balance and credit limit monitoring for unauthorized changes
Identity Theft Recovery and Restoration
Despite best prevention efforts, some individuals will experience identity theft. Rapid response and systematic restoration minimize damage and restore financial stability more quickly than ad hoc recovery attempts.
Immediate Response Protocol (First 24 Hours)
Hour 1-2: Damage Assessment
- Review all financial accounts for unauthorized transactions- Check credit reports from all three bureaus for new accounts or inquiries- Document all suspicious activity with screenshots and account statements- Contact financial institutions to report suspected fraud
Hour 3-8: Account Security
- Change passwords for all potentially compromised accounts- Enable two-factor authentication where not already implemented- Place fraud alerts with all three credit bureaus- Contact relevant financial institutions to freeze affected accounts
Hour 9-24: Documentation and Reporting
- File police report for identity theft (required for many restoration processes)- Report identity theft to FTC through IdentityTheft.gov- Begin detailed documentation of all fraud-related communications- Contact employers and known associates if business identity theft is suspected
Systematic Restoration Process
Week 1: Immediate Stabilization
- Work with financial institutions to dispute fraudulent transactions- Close compromised accounts and establish new accounts with enhanced security- Implement credit freezes across all credit bureaus- Begin communication with creditors about fraudulent accounts
Month 1: Comprehensive Recovery
- Dispute all fraudulent information with credit bureaus using proper documentation- Work with creditors and collection agencies to remove fraudulent debts- Rebuild damaged credit profiles through authorized user or secured credit strategies- Implement enhanced monitoring systems to prevent re-victimization
Months 2-6: Long-term Restoration
- Monitor credit reports monthly for complete fraud removal- Gradually restore normal financial activities while maintaining enhanced security- Document complete recovery for future reference and legal purposes- Implement lessons learned to strengthen long-term identity security
Professional Identity Restoration Services
Complex identity theft cases often require professional assistance to navigate the bureaucratic maze of credit bureaus, financial institutions, and government agencies.
When to Consider Professional Help:
- Multiple fraudulent accounts across different institutions- Business or professional identity theft affecting career prospects- Medical identity theft involving insurance and healthcare records- Criminal identity theft involving law enforcement and court records- International identity theft crossing multiple jurisdictions
Advanced Identity Protection for High-Risk Individuals
Certain individuals face elevated identity theft risks due to their profession, public visibility, or asset complexity. These situations require specialized protection strategies beyond standard identity security measures.
Public Figure and Influencer Protection
Content creators and public figures face unique identity theft risks due to their high visibility and the personal information they often share publicly. Criminal targeting increases significantly for individuals with large social media followings or public recognition.
Enhanced Protection Strategies:
- Professional identity monitoring services with faster response times- Advanced social media security protocols and content review processes- Legal entity structures to separate personal and professional financial activities- Specialized insurance coverage for reputation damage and professional losses
High-Net-Worth Identity Protection
Individuals with significant assets, complex financial portfolios, or luxury possessions face sophisticated targeting from organized criminal groups specializing in high-value identity theft.
Specialized Security Measures:
- Private banking security protocols and enhanced authentication measures- Asset protection strategies including legal structures and offshore considerations- Executive protection services integration with digital identity security- Specialized recovery services for complex financial restoration
Luxury Asset Considerations: Ownership of high-value assets creates unique identity theft risks. Private yacht ownership and aircraft ownership often appear in specialized databases that criminals target for high-value identity theft schemes. Protection strategies must address both digital and physical security concerns.
Professional and Business Identity Protection
Individuals whose identity theft could impact their professional standing or business operations require specialized protection addressing both personal and professional consequences.
Business-Grade Identity Security:
- Corporate identity monitoring systems adapted for personal use- Professional reputation monitoring and crisis management capabilities- Enhanced verification systems for business and professional communications- Specialized legal and insurance coverage for professional impact scenarios
Technology Tools and Services for Identity Protection
Modern identity protection requires deploying multiple specialized tools and services that work together to create comprehensive coverage across all attack vectors.
Essential Identity Protection Technology Stack
Password Management and Authentication:
- Enterprise-grade password managers (1Password Business, Bitwarden, or Dashlane)- Hardware security keys for critical accounts (YubiKey or similar devices)- Authenticator apps for multi-factor authentication (Authy, Google Authenticator)
Privacy and Communication Security:
- VPN services for secure internet communications (ExpressVPN, NordVPN, or Surfshark)- Encrypted email services (ProtonMail or Tutanota for sensitive communications)- Secure messaging applications (Signal for private communications)
Monitoring and Detection Systems:
- Comprehensive credit monitoring across all three bureaus- Dark web monitoring services for compromised information detection- Financial account monitoring with real-time transaction alerts- Social media monitoring for unauthorized use of personal information
Professional-Grade Security Tools
For individuals requiring enhanced protection, professional-grade security tools provide enterprise-level capabilities adapted for personal use.
Advanced Security Technologies:
- Endpoint detection and response (EDR) software for device protection- Network monitoring tools for home and office environments- Threat intelligence feeds for proactive threat awareness- Professional digital forensics capabilities for incident investigation
Building Long-Term Identity Security Habits
Sustainable identity protection requires developing security habits that become second nature rather than relying on periodic security reviews or reactive measures.
Daily Identity Security Practices
Morning Security Routine (5 minutes):
- Review overnight account notifications and alerts- Check for unusual device login notifications- Verify no unexpected password reset or security emails- Monitor news for new data breaches affecting your service providers
Evening Security Review (10 minutes):
- Review daily financial account activity across all accounts- Check social media for unauthorized posts or account access- Verify no unexpected friend requests or connection attempts- Review and clear browser history and temporary files
Weekly Security Maintenance
Account Security Audit:
- Review recent login activity across all major accounts- Check for new devices or sessions requiring authorization- Update any weak or reused passwords identified during the week- Review and adjust privacy settings on frequently used platforms
Financial Security Review:
- Comprehensive review of all financial account activity- Check credit card and bank statements for unusual transactions- Monitor investment accounts for unauthorized changes or access- Review recurring subscription and payment authorizations
Monthly Comprehensive Assessment
Identity Security Health Check:
- Complete credit report review across all three bureaus- Dark web monitoring result analysis and action item identification- Social media privacy settings review and adjustment- Update emergency contact and account recovery information
Technology Security Maintenance:
- Software updates across all devices and security applications- Security software scan and threat detection review- Backup verification and data recovery testing- Network security assessment and Wi-Fi security verification
The Future of Identity Theft and Protection
Identity theft continues evolving as criminals adopt new technologies and exploit emerging vulnerabilities. Understanding future threats helps build protection strategies that remain effective as the threat landscape changes.
Emerging Identity Theft Techniques
Artificial Intelligence and Machine Learning Exploitation: Criminals increasingly use AI to automate social engineering attacks, create convincing deepfake communications, and analyze vast amounts of personal data to identify vulnerable targets.
Synthetic Identity Theft: Rather than stealing complete identities, criminals combine real and fabricated information to create new identities that can evade traditional detection methods while building credit and financial profiles over time.
IoT and Smart Device Exploitation: As homes and vehicles become increasingly connected, criminals exploit vulnerable IoT devices to gather personal information, monitor daily routines, and even gain physical access to homes and offices.
Regulatory and Legal Developments
Enhanced Consumer Protection Laws: New state and federal regulations provide stronger identity theft protections, but require active consumer engagement to implement effectively.
International Coordination: Cross-border criminal activity necessitates international cooperation in identity theft prevention and prosecution, affecting how individuals protect themselves in globally connected environments.
Technology Company Liability: Increasing corporate liability for data breaches and privacy violations creates new protections for consumers but also new complexities in understanding rights and remedies.
Taking Action: Your Identity Protection Implementation Plan
Effective identity protection requires systematic implementation of security measures appropriate to your specific risk profile and lifestyle factors. Start with fundamental protections, then add specialized measures based on your assessment results and unique circumstances.
Phase 1: Foundation Security (Week 1-2)
Immediate Priority Actions:
- **Complete our **Identity Threat Detection Calculator for personalized risk assessment2. Implement strong credential security across all major accounts3. Deploy credit monitoring and place fraud alerts with all three bureaus4. **Review and configure **social media privacy settings across all platforms
Phase 2: Comprehensive Protection (Month 1)
Enhanced Security Implementation:
- Deploy professional monitoring services for credit, dark web, and financial accounts2. Implement data broker removal across major people-search databases3. **Establish **advanced digital privacy tools including VPN and encrypted communications4. Create systematic monitoring routines for ongoing identity security maintenance
Phase 3: Specialized Protection (Month 2-3)
Risk-Specific Security Measures: Based on your lifestyle and risk factors, implement specialized protections:
- Influencer and public figure protection for individuals with public visibility- High-net-worth security measures for complex asset portfolios- Professional aviation security for private aircraft ownership- Advanced OSINT protection for high-risk threat environments
Ongoing Maintenance and Updates
Identity protection is an ongoing process requiring regular maintenance, updates, and threat awareness. Establish routines that maintain your security posture while adapting to new threats and life changes.
Quarterly Security Reviews:
- Comprehensive reassessment using our identity threat calculator- Update protection strategies based on life changes or new threats- Review and refresh all security tools and service subscriptions- Conduct family security training and update emergency procedures
Your identity is the foundation of your financial security, professional reputation, and personal safety. In an era where criminals can steal and exploit identities with unprecedented sophistication, proactive protection isn’t optional—it’s essential.
The strategies outlined in this guide provide comprehensive protection against current threats while positioning you to adapt to future identity theft techniques. By implementing systematic security measures appropriate to your risk profile, you can enjoy the benefits of our connected world while maintaining control over your personal information and financial security.
Ready to assess your identity theft risk? Complete our Identity Threat Detection Calculator to discover your specific vulnerabilities and receive personalized protection recommendations. Your financial security and peace of mind depend on the actions you take today.
Identity theft protection is most effective when implemented before you become a victim. Start your comprehensive identity security assessment today and take control of your digital identity before criminals take control of your life.