In the digital age, your personal information is scattered across thousands of publicly accessible databases, social media profiles, government records, and commercial websites. What most people don’t realize is how easily this seemingly harmless information can be weaponized against them through Open Source Intelligence (OSINT) techniques—sophisticated methods that can reveal shocking details about your life, habits, relationships, and vulnerabilities without ever requiring illegal access to your private accounts.
OSINT practitioners can discover where you live, work, and travel. They can identify your family members, financial status, political views, and personal routines. They can predict your behavior, exploit your relationships, and in some cases, even access your physical location in real-time. This isn’t science fiction—it’s happening right now to millions of people who have no idea they’re being systematically profiled using information they voluntarily made public.
The challenge isn’t just the sophistication of modern OSINT tools—it’s that most people have no concept of their digital exposure level or how to defend against intelligence gathering techniques. Traditional privacy advice focuses on securing accounts and devices while ignoring the massive information trail everyone leaves through public records, social media activity, and commercial data collection.
This comprehensive guide reveals how OSINT techniques work, what information they can discover about you, and most importantly, how to implement effective countermeasures that dramatically reduce your exposure to intelligence gathering while maintaining your digital lifestyle.

Understanding the OSINT Threat Landscape
Open Source Intelligence gathering has evolved from a specialized military and intelligence discipline into a democratized practice accessible to anyone with internet access and basic research skills. The same techniques once reserved for government agencies are now used by private investigators, corporate security teams, criminals, stalkers, and curious individuals who want to learn more about specific targets.
What makes OSINT particularly dangerous is its legal and ethical gray area. All the information gathered comes from publicly available sources, making the practice generally legal while remaining highly invasive. This creates a perfect storm where sophisticated intelligence gathering operates with minimal oversight or protection for targets.
Modern OSINT practitioners don’t just search Google and social media—they use specialized tools, databases, and techniques that can correlate information across hundreds of sources to build comprehensive profiles that reveal far more than any individual source would suggest.
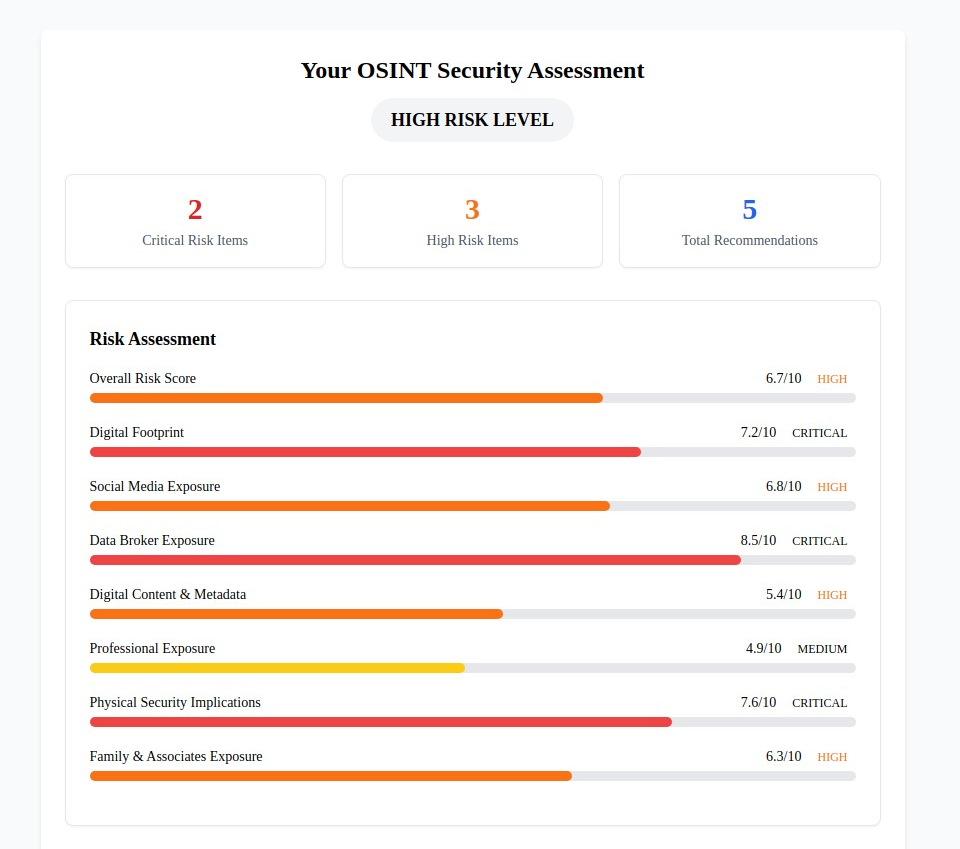
Discover your OSINT exposure level with our comprehensive OSINT Security Self-Assessment. This specialized evaluation analyzes your vulnerability across eight critical categories and provides personalized recommendations to reduce your intelligence gathering exposure.
The Eight Critical OSINT Exposure Categories
Our analysis of thousands of OSINT investigations reveals that comprehensive intelligence gathering exploits vulnerabilities across eight interconnected categories. Understanding these categories is essential for effective protection:
Digital Information Sources:
- Digital Footprint Overview - Your overall online presence and information discoverability- Social Media Exposure - How your social platforms reveal personal information and behavioral patterns- Data Broker Presence - Your information’s availability through commercial data aggregation services- Digital Content & Metadata - Hidden information in photos, documents, and online content
Real-World Intelligence Vectors:
- Professional Network Exposure - How your career and business activities create intelligence opportunities- Physical Security Implications - How digital information reveals physical locations and routines- Family & Associates Exposure - How your connections and relationships create additional intelligence vectors
Advanced Correlation Techniques:
- Cross-Platform Data Correlation - How information from multiple sources combines to reveal comprehensive profiles
Each category represents a different intelligence gathering opportunity that OSINT practitioners exploit. Weakness in any area can compromise your entire privacy strategy, while strength across all categories creates comprehensive protection against even sophisticated intelligence operations.
How OSINT Techniques Expose Your Life
Social Media Intelligence Mining
Social media platforms function as comprehensive intelligence databases where people voluntarily share detailed information about their lives, opinions, relationships, and activities. OSINT practitioners use specialized tools and techniques that go far beyond casual browsing to extract maximum intelligence value.
Advanced Social Media OSINT Techniques:
- Metadata extraction from photos revealing GPS coordinates, device information, and timestamps- Social network mapping to identify family members, colleagues, and relationship patterns- Behavioral analysis to predict routines, preferences, and future activities- Cross-platform correlation to link accounts and build comprehensive profiles
Information Typically Discovered:
- Home and work addresses through location tagging and background analysis- Family relationships and personal networks through connections and mentions- Financial status indicators through lifestyle posts and purchase displays- Travel patterns and routine activities through check-ins and photos- Political views, personal beliefs, and potential vulnerabilities through posts and interactions
Our social media privacy protection guide provides detailed countermeasures, but OSINT protection requires additional techniques beyond standard privacy settings.
Public Records and Government Database Mining
Government agencies maintain extensive databases of personal information that become powerful intelligence sources when properly exploited. OSINT practitioners know how to navigate these systems to extract comprehensive information about individuals, their assets, and their activities.
Commonly Exploited Public Records:
- Property records revealing home addresses, purchase prices, and ownership histories- Court documents exposing legal issues, divorces, bankruptcies, and business disputes- Business registrations showing corporate affiliations, partnerships, and financial relationships- Professional licenses indicating skills, certifications, and regulatory compliance- Voter registration revealing political affiliation and residential history
Advanced Public Records Techniques:
- Cross-referencing multiple jurisdictions to build comprehensive residential and business histories- Asset discovery through property ownership, business interests, and financial filings- Network analysis using business partnerships and professional relationships- Timeline reconstruction showing life events, moves, and major decisions
For individuals with luxury assets like yachts or private aircraft, public registration databases create additional intelligence exposure requiring specialized protection strategies.
Data Broker and Commercial Intelligence Harvesting
Data brokers operate vast networks that collect, aggregate, and resell personal information from hundreds of sources. These commercial databases often contain more comprehensive and up-to-date information than government records, making them primary targets for OSINT practitioners.
Major Data Broker Intelligence Sources:
- People search engines like WhitePages, Spokeo, and BeenVerified- Professional networking sites including LinkedIn and industry-specific platforms- Consumer databases from retailers, loyalty programs, and marketing companies- Financial databases from credit agencies and commercial lending sources- Specialized databases for specific industries or demographic groups
Information Typically Available:
- Current and historical addresses with residence timelines- Phone numbers including unlisted and mobile numbers- Email addresses across multiple accounts and services- Family member information including names, ages, and relationships- Professional history including employers, positions, and salary estimates- Financial indicators including property values, estimated income, and credit information
Digital Content Analysis and Metadata Exploitation
Every digital file contains hidden information that can reveal far more than the visible content suggests. OSINT practitioners use specialized tools to extract and analyze this metadata to build intelligence profiles and discover sensitive information.
Metadata Intelligence Sources:
- Photo EXIF data revealing GPS coordinates, camera settings, and timestamp information- Document metadata showing creation dates, editing history, and software information- Email headers revealing routing information, server details, and sender verification- Website analytics showing visitor patterns, technology usage, and behavioral data
Advanced Content Analysis Techniques:
- Facial recognition using social media photos to identify individuals across platforms- Reverse image searching to find other instances of photos and identify connections- Linguistic analysis to identify writing patterns, education level, and potential geographic origin- Behavioral pattern recognition to predict future activities and identify vulnerabilities
For content creators and influencers, digital content analysis presents particular risks that require specialized protection strategies beyond standard content creation practices.
Comprehensive OSINT Protection Strategies
Digital Footprint Reduction and Management
Effective OSINT protection starts with understanding and minimizing your digital footprint across all online platforms and databases. This goes far beyond privacy settings to encompass fundamental changes in how you interact with digital services and share information.
Immediate Digital Footprint Actions:
- Complete comprehensive OSINT assessment to understand your current exposure level2. Audit all social media accounts for information that could be used for intelligence gathering3. Review and restrict public profile information across all platforms and services4. Implement systematic content review for posts, photos, and shared information
Advanced Digital Footprint Management:
- Username compartmentalization using different identities for different purposes- Email address segmentation to prevent cross-platform correlation- Information sharing protocols that limit intelligence gathering opportunities- Regular digital footprint auditing to identify new exposure sources
Professional Digital Identity Protection: For individuals requiring enhanced protection—such as those with high-value assets or public-facing careers—digital footprint management becomes a critical security practice requiring professional-grade techniques and ongoing monitoring.
Social Media Counter-Surveillance Implementation
Standard social media privacy settings provide minimal protection against sophisticated OSINT techniques. Effective counter-surveillance requires understanding how intelligence practitioners exploit social platforms and implementing targeted countermeasures.
Essential Social Media OSINT Protection:
- Account privacy hardening beyond standard settings using our comprehensive social media privacy guide- Content sanitization to remove intelligence-useful information from existing posts- Metadata stripping from all uploaded photos and documents- Network obfuscation to prevent relationship mapping and social network analysis
Advanced Counter-Surveillance Techniques:
- Decoy information deployment to confuse intelligence gathering attempts- Behavioral pattern disruption to prevent routine prediction and analysis- Cross-platform isolation to prevent account correlation and profile building- Professional monitoring for unauthorized use of personal information
Family and Associates Protection: OSINT techniques often exploit information shared by family members and associates. Comprehensive protection requires coordinating security measures across your entire social network, including identity protection strategies for family members and education about intelligence gathering risks.
The Complete Guide to Digital Privacy Protection: Your Comprehensive Toolkit for 2025
Data Broker Removal and Commercial Database Protection
Data brokers maintain some of the most comprehensive and accessible personal information databases available to OSINT practitioners. Effective protection requires systematic removal from these databases and ongoing monitoring to prevent information reappearance.
Critical Data Broker Protection Steps:
- Identify major data broker presence through systematic searching across all major platforms2. Submit removal requests to all identified data brokers using proper procedures3. Implement automated monitoring for information reappearance4. Deploy professional removal services for comprehensive and ongoing protection
Major Data Brokers Requiring Removal:
- People search engines (WhitePages, Spokeo, BeenVerified, Intelius)- Professional databases (LinkedIn, industry-specific platforms)- Commercial marketing databases (Epsilon, Acxiom, LexisNexis)- Specialized databases (property records, business registrations, professional licenses)
Ongoing Data Broker Monitoring:
- Monthly searches across major data broker platforms for information reappearance- Google Alerts for your name and associated information- Professional monitoring services for comprehensive coverage and automated removal- Family member monitoring to prevent intelligence gathering through associates
Public Records Privacy and Legal Protection
Government databases present unique challenges because information removal often requires legal procedures and may not be possible in all cases. Protection strategies focus on minimizing future exposure and limiting the intelligence value of existing records.
Public Records Protection Strategies:
- Asset privacy structures including trusts and business entities to obscure ownership- Address privacy techniques including mail forwarding and registered agent services- Professional license management to limit unnecessary public exposure- Legal consultation for complex privacy situations requiring professional assistance
Physical Security and Location Protection: Public records often reveal physical addresses and locations that create security risks beyond digital privacy concerns. For individuals with elevated physical security needs—including those with luxury assets or public profiles—comprehensive location privacy becomes essential.
Advanced Legal Privacy Techniques:
- Business entity structures to separate personal and professional activities- Offshore privacy considerations for international asset protection- Professional privacy consultation for complex legal and financial situations- Ongoing legal monitoring for new privacy regulations and protection opportunities
OSINT Protection by Risk Level
Basic Protection (Low-Medium Risk Individuals)
Most people require fundamental OSINT protection that addresses common intelligence gathering techniques without requiring sophisticated countermeasures or significant lifestyle changes.
Essential Basic Protection Measures:
- Complete OSINT security assessment to understand specific vulnerabilities2. Implement social media privacy lockdown using comprehensive privacy settings3. Begin data broker removal campaign starting with major people search engines4. Deploy basic digital identity protection including email and username management
Ongoing Basic Maintenance:
- Monthly social media privacy reviews to maintain protection settings- Quarterly data broker monitoring to detect and remove reappearing information- Annual OSINT assessment to identify new vulnerabilities and update protection strategies- Family privacy education to prevent intelligence leakage through associates
Enhanced Protection (Medium-High Risk Individuals)
Individuals with elevated exposure risks—including content creators, business owners, or those involved in controversial activities—require enhanced OSINT protection addressing sophisticated intelligence gathering techniques.
Enhanced Protection Implementation:
- Professional OSINT assessment with detailed vulnerability analysis and customized recommendations- Comprehensive data broker removal across all major databases with ongoing monitoring- Advanced social media counter-surveillance including behavioral pattern disruption- Professional digital identity management with compartmentalized online presence
Specialized Enhanced Measures:
- Professional reputation monitoring for unauthorized information disclosure- Network security hardening to prevent technical intelligence gathering- Physical security integration addressing location privacy and operational security- Legal privacy consultation for complex asset protection and privacy structures
Advanced Protection (High Risk Individuals)
High-risk individuals including public figures, high-net-worth individuals, or those facing specific threats require sophisticated OSINT protection equivalent to professional intelligence countermeasures.
Advanced Protection Strategies:
- Professional OSINT audit by qualified intelligence professionals with comprehensive threat assessment- Automated monitoring systems for real-time intelligence gathering detection- Sophisticated counter-intelligence techniques including disinformation and operational security- Professional security team coordination integrating digital and physical security measures
Specialized High-Risk Considerations: For individuals with significant assets, aviation interests, or complex business activities, OSINT protection must address specialized databases and industry-specific intelligence sources that create unique exposure risks.
Professional and Corporate OSINT Defense
Business Intelligence Protection
Corporate entities and business professionals face sophisticated OSINT attacks designed to gather competitive intelligence, identify vulnerabilities, and exploit business relationships. Professional OSINT protection requires understanding how business activities create intelligence opportunities.
Corporate OSINT Exposure Sources:
- Business registration databases revealing ownership structures and financial relationships- Professional licensing records showing qualifications and regulatory compliance- Court filings and legal documents exposing business disputes and financial difficulties- Industry publications and press coverage providing strategic and operational intelligence
Professional Protection Strategies:
- Business entity privacy structures to obscure ownership and operational details- Professional information management limiting unnecessary public exposure- Competitive intelligence monitoring to detect corporate OSINT targeting- Employee training and awareness to prevent accidental intelligence disclosure
Executive and Leadership Protection
Senior executives and business leaders face targeted OSINT attacks designed to gather intelligence for corporate espionage, social engineering, or direct targeting. Executive protection requires sophisticated countermeasures addressing both personal and professional exposure.
Executive OSINT Targeting Techniques:
- Social network mapping to identify family members and personal relationships- Financial intelligence gathering to understand assets and potential vulnerabilities- Operational pattern analysis to predict schedules and identify opportunities- Reputation intelligence to identify potential leverage or embarrassment opportunities
Executive Protection Implementation:
- Comprehensive digital identity audit addressing both personal and professional exposure- Advanced privacy structures including legal entities and asset protection- Professional monitoring services for ongoing threat detection and intelligence gathering- Family and associate protection extending security measures to personal networks
Technology Tools for OSINT Defense
Detection and Monitoring Systems
Effective OSINT protection requires understanding when you’re being targeted and what information is being gathered. Detection systems provide early warning of intelligence gathering activities and help assess the effectiveness of protection measures.
Essential Monitoring Tools:
- Google Alerts for your name and associated information across the internet- Social media monitoring for unauthorized use of personal information or photos- Dark web monitoring for personal information appearing in criminal databases- Professional reputation monitoring for business and career-related intelligence gathering
Advanced Detection Systems:
- Professional OSINT monitoring services providing comprehensive coverage across multiple intelligence sources- Automated data broker scanning to detect information reappearance across commercial databases- Network traffic analysis to detect technical reconnaissance and intelligence gathering attempts- Physical security integration to correlate digital and physical surveillance activities
Counter-OSINT Technology Deployment
Specialized tools and technologies can actively interfere with OSINT gathering techniques while providing enhanced privacy protection for high-risk individuals.
Counter-OSINT Technologies:
- Advanced VPN services with specialized features for intelligence gathering protection- Anonymous communication tools preventing correlation and network analysis- Metadata stripping software to remove intelligence-useful information from digital content- Professional privacy software designed specifically for high-risk intelligence environments
Operational Security (OPSEC) Integration: For individuals requiring maximum protection, OSINT defense must integrate with broader operational security practices addressing behavioral patterns, communication security, and activity monitoring that could compromise protection effectiveness.
Building Long-Term OSINT Resistance
Sustainable Privacy Practices
Effective OSINT protection requires developing sustainable privacy practices that become second nature rather than relying on periodic security reviews or reactive measures after intelligence gathering is detected.
Daily OSINT Protection Habits:
- Information sharing assessment before posting or sharing any personal information- Metadata review for all photos and documents before uploading or sending- Privacy setting verification across all platforms and services used throughout the day- Digital footprint awareness maintaining consciousness of intelligence gathering opportunities
Weekly Protection Maintenance:
- Social media content review assessing recent posts and interactions for intelligence value- Search result monitoring checking for new information appearing in search engines- Data broker scanning using automated tools to detect information reappearance- Family and network coordination ensuring protection measures remain effective across associates
Advanced Operational Security Integration
For high-risk individuals, OSINT protection must integrate with comprehensive operational security practices that address behavioral patterns, communication security, and activity monitoring.
Professional OPSEC Integration:
- Behavioral pattern disruption to prevent routine analysis and prediction- Communication security protocols preventing intelligence gathering through interaction monitoring- Activity compartmentalization isolating different aspects of personal and professional life- Ongoing threat assessment adapting protection measures to changing risk levels and intelligence gathering techniques
Measuring OSINT Protection Effectiveness
Assessment and Monitoring Metrics
Quantitative Protection Indicators:
- Search result reduction in personal information available through major search engines- Data broker presence elimination across major commercial databases- Social media exposure reduction in discoverable personal information and metadata- Public records minimization where legally possible and appropriate
Qualitative Protection Assessment:
- Intelligence gathering difficulty increase for potential adversaries attempting reconnaissance- Information correlation reduction preventing comprehensive profile building across multiple sources- Family and associate protection extending security measures across personal networks- Professional reputation security maintaining appropriate business exposure while protecting personal privacy
Regular Protection Evaluation:
- Monthly OSINT assessment using our comprehensive evaluation tool to track improvement- Quarterly professional consultation for high-risk individuals requiring ongoing threat assessment- Annual comprehensive audit reviewing all protection measures and updating strategies for emerging threats- Ongoing education and training staying current with new OSINT techniques and protection methods
The Future of OSINT and Privacy Protection
Emerging Intelligence Gathering Techniques
Artificial Intelligence and Machine Learning: AI systems increasingly analyze vast amounts of public information to identify patterns, predict behavior, and discover non-obvious connections that human analysts might miss. Future OSINT protection must address algorithmic analysis and automated intelligence gathering.
Internet of Things (IoT) Exploitation: Connected devices create new intelligence gathering opportunities through ambient data collection, behavioral monitoring, and involuntary information disclosure. OSINT protection must evolve to address ubiquitous sensing and data collection.
Biometric and Behavioral Analysis: Advanced recognition technologies can identify individuals across multiple platforms and locations using facial features, voice patterns, writing styles, and behavioral characteristics. Protection strategies must address biological and behavioral privacy.
Regulatory and Legal Developments
Enhanced Privacy Rights: New privacy regulations provide stronger protection against unauthorized intelligence gathering, but require active engagement to implement effectively. Understanding and exercising these rights becomes crucial for comprehensive OSINT protection.
Intelligence Gathering Regulations: Increasing regulation of commercial intelligence activities and data broker operations creates new protection opportunities but also new complexities in understanding rights and remedies.
International Coordination: Cross-border intelligence gathering and international data sharing affect how individuals protect themselves in globally connected environments requiring coordination across multiple jurisdictions.
Taking Action: Your OSINT Protection Implementation
Effective OSINT protection requires systematic implementation of countermeasures appropriate to your specific risk profile and threat level. Most people dramatically underestimate their intelligence gathering exposure while remaining unaware of simple protective measures that dramatically improve their security posture.
Start with comprehensive assessment: Understanding your current OSINT exposure is essential for implementing effective protection measures. Generic privacy advice often misses critical vulnerabilities while recommending unnecessary protections that don’t match your actual risk profile.
Complete our OSINT Security Self-Assessment to discover your specific vulnerabilities across all eight critical categories and receive personalized recommendations prioritized by risk level. This comprehensive evaluation helps you focus your protection efforts where they’ll have the greatest impact.
Phase 1: Critical Risk Mitigation (Week 1)
Immediate Priority Actions:
- Complete OSINT security assessment to identify critical vulnerabilities requiring urgent attention2. Implement data broker removal campaign starting with the most exposed commercial databases3. Deploy physical security protection addressing location privacy and operational security gaps4. Execute social media privacy lockdown using comprehensive privacy settings and content review
Phase 2: Comprehensive Protection Implementation (Month 1)
Enhanced Security Deployment:
- Complete digital identity protection audit addressing username management and information compartmentalization2. **Implement advanced **social media counter-surveillance including metadata stripping and behavioral pattern disruption3. Deploy professional monitoring systems for ongoing threat detection and intelligence gathering awareness4. **Establish **personal privacy tool integration coordinating OSINT protection with broader privacy strategies
Phase 3: Advanced and Specialized Protection (Month 2+)
Risk-Specific Enhancement: Based on your assessment results and lifestyle factors, implement specialized protections:
- High-net-worth intelligence protection for complex asset portfolios and luxury lifestyle exposure- Professional aviation intelligence security for private aircraft ownership and travel pattern protection- Content creator counter-surveillance for public-facing individuals and social media presence- Advanced identity protection integration for comprehensive personal security coordination
Ongoing Protection Maintenance
Monthly Security Reviews:
- Reassess OSINT exposure using our comprehensive evaluation tool- Monitor for new information appearing in search engines and data broker databases- Review and update protection measures based on changing risk factors and threat levels- Coordinate protection strategies across family members and business associates
Quarterly Professional Assessment:
- Comprehensive OSINT audit for high-risk individuals requiring ongoing threat assessment- Update protection strategies based on new intelligence gathering techniques and threat indicators- Review legal and regulatory changes affecting OSINT protection rights and opportunities- Professional consultation for complex protection scenarios requiring specialized expertise
Your information is already being gathered, analyzed, and potentially exploited through sophisticated OSINT techniques. The question isn’t whether you need protection—it’s whether you’ll implement effective countermeasures before this intelligence is used against you.
Take control of your intelligence exposure today. Complete our comprehensive OSINT Security Self-Assessment and discover exactly what information can be gathered about you and how to protect against it. Your digital freedom and personal security depend on understanding and defending against intelligence gathering techniques that most people never even realize exist.
OSINT protection is most effective when implemented before you become a target. Assess your intelligence gathering exposure today and take control of your information before others take control of your life.