Social media has fundamentally transformed how we communicate, share experiences, and build relationships. Yet with over 4.8 billion users worldwide sharing unprecedented amounts of personal data, these platforms have become goldmines for data harvesting, surveillance, and privacy violations. Recent revelations about Meta training AI models on user content without explicit consent highlight a disturbing truth: your social media activity is being monetized in ways you never agreed to.
Social Media Risk Assessment Tool
The challenge isn’t just about privacy settings—it’s about understanding the complex web of data collection, cross-platform tracking, and algorithmic analysis that occurs every time you engage with social media. Most users operate with default settings that prioritize platform profits over personal privacy, creating massive vulnerabilities in their digital lives.
This comprehensive guide provides platform-specific strategies to reclaim control over your social media privacy, protect your personal data, and secure your digital presence across all major networks. Whether you’re a casual user or a content creator, these evidence-based techniques will dramatically reduce your privacy risk profile.

 *
t
*
*
t
*
Understanding Your Social Media Privacy Risk Profile
Before diving into platform-specific protections, it’s crucial to understand your current exposure level. Modern social media privacy risks extend far beyond what you post—they encompass your device permissions, cross-platform data sharing, location tracking, AI training data usage, and behavioral analytics.
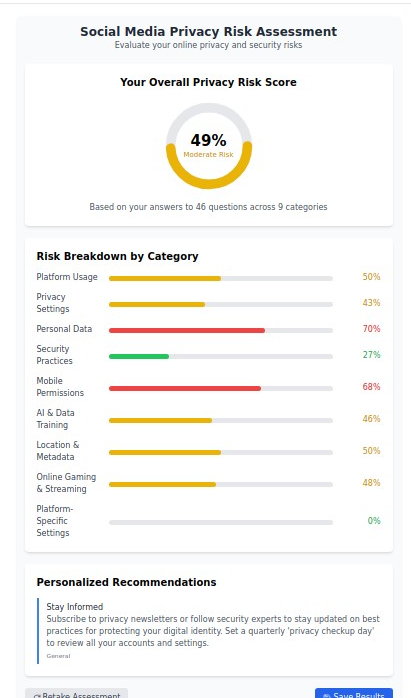
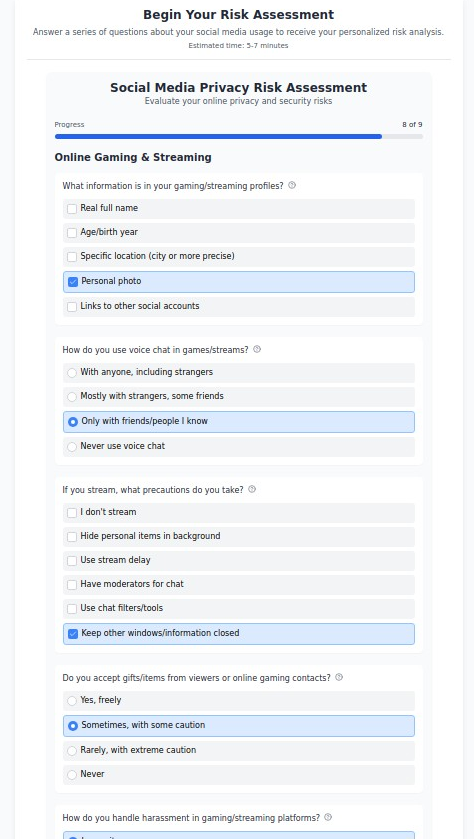
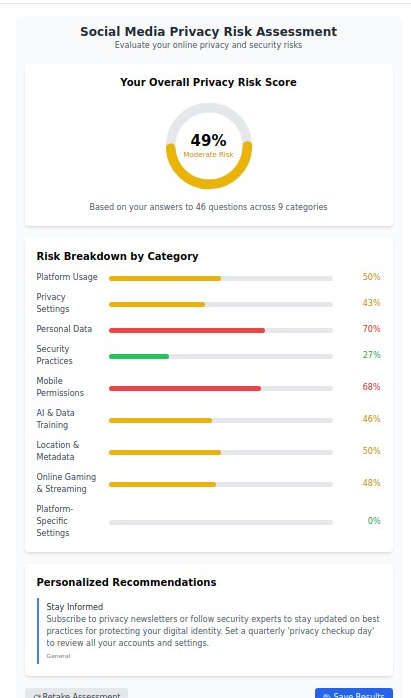
Our research analyzing thousands of social media users reveals that the average person has a moderate to high privacy risk score across nine critical categories:
- Platform Usage Patterns - How your activity creates data profiles- Privacy Settings Configuration - Whether you’ve optimized built-in protections- Personal Data Exposure - What sensitive information you’re inadvertently sharing- Security Practices - Your account protection measures- Mobile Permissions - What device access you’ve granted- AI & Data Training - How your content is used for machine learning- Location & Metadata - Geographic and technical data exposure- Cross-Platform Integration - How platforms share your information- Platform-Specific Vulnerabilities - Unique risks on each network
Take our free Social Media Privacy Risk Assessment to discover your specific vulnerabilities and receive personalized protection recommendations. This confidential analysis evaluates your practices across all major platforms and provides actionable insights for improvement.
The Hidden Costs of Social Media Privacy Neglect
The consequences of inadequate social media privacy protection extend far beyond targeted advertising. Consider these real-world impacts:
Professional Consequences: 70% of employers research candidates on social media, and 54% have decided not to hire someone based on their social media presence. Poor privacy settings can expose personal information that damages professional opportunities.
Personal Safety Risks: Location data, check-ins, and photo metadata can enable stalking, burglary, and physical threats. Content creators and public figures face particularly elevated risks from inadequate privacy protection.
Financial Exploitation: Personal information gathered from social media is increasingly used for social engineering attacks, identity theft, and financial fraud. Even seemingly innocent posts can provide answers to security questions or reveal behavioral patterns.
Relationship and Family Impact: Privacy breaches can expose family members, damage relationships, and compromise children’s safety. Cross-platform data sharing can reveal information about contacts who never consented to surveillance.
Long-term Reputation Damage: Social media content persists far longer than most users realize. Poor privacy practices today can impact opportunities, relationships, and reputation for years to come.
Meta AI’s Privacy Controversy: Instagram and Beyond
Facebook Security Essentials: A 2025 Technical Guide
Platform-Specific Privacy Protection Strategies
Facebook/Meta: Comprehensive Privacy Lockdown
Meta’s ecosystem presents unique challenges due to its integration across Facebook, Instagram, WhatsApp, and Messenger, plus extensive third-party data sharing partnerships.
Essential Privacy Configurations:
Account Privacy Settings:
- Navigate to Settings & Privacy → Privacy → Future Posts and set default audience to “Friends” only- Review “Limit Past Posts” to restrict old content to friends only- Disable “Public Post Comments” to prevent strangers from commenting- Turn off “Story Sharing” to prevent friends from sharing your stories
Data Usage and Training Opt-Outs:
- Access Privacy → Your information on Meta → Information you provide → Object to processing for AI training- Review and limit “Off-Facebook Activity” to prevent external website tracking- Disable “Face Recognition” and delete existing face scan data- Turn off “Location History” and “Nearby Friends” location sharing
Advanced Security Measures:
- Enable two-factor authentication using an authenticator app (never SMS)- Review “Active Sessions” and remove unrecognized devices- Enable “Get alerts about unrecognized logins”- Disable “Login from Saved Devices” on shared computers
Third-Party App Cleanup:
- Review “Apps and Websites” permissions and remove unused applications- Disable “Apps Others Use” to prevent friends’ apps from accessing your data- Turn off “Old Versions of Facebook for Mobile” data access
Cross-Platform Data Sharing Prevention:
- Disable “Upload Contacts” synchronization- Turn off “People You May Know” suggestions based on contact data- Prevent “Search Engine Indexing” of your profile- Limit “Who can look you up” using email and phone number
Instagram Privacy Deep Dive: A Technical Guide to Securing Your Account
Instagram: Advanced Privacy Configuration
Instagram’s visual nature creates unique privacy risks through photo metadata, location exposure, and algorithmic content analysis.
Core Privacy Settings:
Account Visibility Controls:
- Switch to Private Account under Settings → Privacy → Account Privacy- Enable “Manual Approval” for all follower requests- Disable “Similar Account Suggestions” to prevent algorithmic recommendations- Turn off “Contacts Syncing” to prevent phone book access
Content Protection Strategies:
- Disable “Allow Sharing” to prevent others from sharing your stories- Turn off “Activity Status” to hide when you’re online- Disable “Read Receipts” in direct messages- Enable “Restrict” mode for problematic followers instead of blocking
Location and Metadata Protection:
- Disable “Location Services” for Instagram in phone settings- Remove location data from existing posts- Turn off “Location History” in account settings- Disable “Precise Location” access in device permissions
Advanced Privacy Features:
- Enable “Two-Factor Authentication” with authenticator app- Review and remove “Authorized Applications”- Disable “Data Download” accessibility for efficiency- Turn off “Interest-Based Ads” in ad preferences
X (Twitter) Security Guide: Protecting Your Account in 2025
Twitter/X: Comprehensive Security Configuration
Twitter’s public-facing nature requires careful balance between engagement and privacy protection.
Essential Security Settings:
Account Protection:
- Enable “Protect Your Posts” for followers-only visibility- Disable “Let Others Find You” by email and phone number- Turn off “Personalized Ads” based on activity and data partnerships- Disable “Track Where You See Twitter Content” across devices
Advanced Privacy Controls:
- Review and revoke “Connected Apps” permissions regularly- Disable “Allow Additional Information Sharing” with business partners- Turn off “Promote Content in Search” engines- Enable “Photo Tagging” restrictions to require approval
Content and Interaction Management:
- Set “Quality Filter” to reduce harmful content exposure- Enable “Safe Search” for sensitive content filtering- Configure “Muted Words” for problematic content- Use “List Management” for controlled content consumption
TikTok Privacy Configuration: A Technical Deep Dive into Security and Control
TikTok: Youth-Focused Privacy Protection
TikTok’s algorithm-driven platform and younger user base require specialized privacy approaches.
Critical Privacy Settings:
Account and Discovery Controls:
- Set account to “Private” to require follower approval- Disable “Suggest Account to Others” using various data sources- Turn off “Profile View History” to prevent tracking who views your profile- Disable “Recently Active” status sharing
Content and Interaction Restrictions:
- Set “Comments” to “Friends Only” or disable entirely- Limit “Duet” and “Stitch” permissions to prevent unauthorized content use- Disable “Download” permissions to prevent content saving- Configure “Direct Messages” to friends only
Data Usage Limitations:
- Turn off “Personalized Ads” in privacy settings- Disable “Off-TikTok Activity” tracking for ad purposes- Limit “Data Usage and Analytics” sharing with third parties- Review and clear “Search History” regularly
LinkedIn Privacy Protection: A 2025 Technical Guide
LinkedIn: Professional Privacy Management
LinkedIn requires careful privacy management to balance professional networking with personal data protection.
Professional Privacy Settings:
Profile Visibility Controls:
- Configure “Public Profile” visibility to limit information available to search engines- Disable “Profile Viewing Options” to browse anonymously- Turn off “Profile Photo Visibility” for non-connections- Limit “Contact Info” visibility to first-degree connections only
Activity and Engagement Privacy:
- Disable “Activity Broadcast” to prevent notifications of profile changes- Turn off “Mentions in the News” automatic content generation- Disable “Data Export” capabilities for contacts- Limit “Who Can See Your Connections” to prevent network harvesting
Communication and Contact Management:
- Configure “Messaging” preferences to prevent spam- Disable “Calendar Syncing” to prevent contact harvesting- Turn off “Email and Phone” discoverability- Enable “Two-Step Verification” for account security
Discord Privacy & Security Guide: 2025 Technical Deep Dive
Discord: Gaming and Community Privacy
Discord’s community-focused platform requires specialized privacy configurations for server participation.
Server and Communication Privacy:
Account Security Fundamentals:
- Enable “Two-Factor Authentication” with authenticator app- Disable “Use Current Location” for timezone detection- Turn off “Sync Contacts” to prevent phone book access- Configure “Friend Requests” to mutual server members only
Message and Content Protection:
- Disable “Developer Mode” unless specifically needed- Turn off “Message Requests” from non-friends- Configure “Screen Reader” accessibility without data sharing- Enable “Safe Direct Messaging” content filtering
Privacy in Server Participation:
- Review “Server Privacy Settings” for each community- Disable “Activity Status” broadcasting to other users- Turn off “Game Activity” sharing and rich presence- Configure “Voice & Video” settings to prevent automatic camera activation
Snapchat Safety Guide: A Technical Deep Dive into Privacy and Protection
Additional Platform Protections
Snapchat Security:
- Enable “Login Verification” two-factor authentication- Configure “Contact Privacy” to prevent friend suggestions- Disable “Location Sharing” and Snap Map visibility- Turn off “Data Export” and “Interest-Based Advertising”
Reddit Privacy:
- Disable “Activity Visibility” in profile settings- Turn off “Content Visibility” in search engines- Configure “Messaging” to prevent unwanted contact- Enable “Two-Factor Authentication” for account security
Telegram Security:
- Use “Secret Chats” for sensitive communications- Enable “Two-Step Verification” with recovery password- Configure “Privacy and Security” for phone number and profile visibility- Disable “Data and Storage” automatic media downloads
Telegram Security Guide: Protecting Your Privacy in 2025
Social Media Risk Assessment Tool
Cross-Platform Privacy Protection Strategies
Universal Security Practices
Multi-Factor Authentication Implementation: Deploy authenticator apps (Google Authenticator, Authy, 1Password) across all platforms instead of SMS-based verification, which is vulnerable to SIM swapping attacks.
Password Security Management: Use unique, complex passwords for each platform managed through reputable password managers like Bitwarden, 1Password, or Keeper. Never reuse social media passwords elsewhere.
Regular Security Audits: Conduct monthly reviews of active sessions, connected apps, and privacy settings across all platforms. Set calendar reminders for quarterly comprehensive audits.
Device-Level Protection: Configure device permissions carefully, limiting social media apps’ access to camera, microphone, location, and contacts unless absolutely necessary for functionality.
Reddit Privacy Guide: Securing Your Presence in 2025
Advanced Privacy Techniques
Data Compartmentalization: Use separate email addresses for social media accounts, preferably with different providers to prevent cross-platform correlation. Consider privacy-focused email services like ProtonMail or Tutanota.
Network-Level Protection: Deploy VPN services when accessing social media, especially on public networks. Consider privacy-focused DNS services like Cloudflare (1.1.1.1) or Quad9 to reduce tracking.
Browser-Based Privacy: Use privacy-focused browsers (Firefox with strict settings, Brave, or Tor) for social media access. Deploy ad blockers, tracker blockers, and script controls to limit data collection.
Content Strategy Privacy: Implement strict content sharing policies: avoid location-identifiable backgrounds, limit personal information disclosure, and use privacy-focused image editing to remove metadata before posting.
The Complete Guide to Digital Privacy Protection: Your Comprehensive Toolkit for 2025
Family and Children’s Social Media Privacy
Parental Control Strategies
Account Supervision Configuration: Most platforms offer parental supervision tools—configure these proactively rather than reactively. Set up notifications for new friend/follower requests and content interactions.
Educational Privacy Training: Teach children about privacy implications before allowing social media access. Explain how posts, comments, and interactions create permanent digital footprints that can impact future opportunities.
Technical Protection Implementation: Use router-level filtering, screen time controls, and family safety software to supplement platform-level protections. Consider dedicated devices for social media use with enhanced monitoring.
Content Creator and Influencer Protection
Professional Privacy Management: Separate personal and professional social media accounts completely. Use business entity information for professional accounts to protect personal data.
Advanced Threat Protection: Implement additional security measures including security keys, dedicated devices for content creation, and professional reputation monitoring services.
Legal Protection Considerations: Understand platform terms of service regarding content ownership, data usage rights, and privacy obligations. Consider legal consultation for significant monetization activities.
Emerging Privacy Threats and Future Protection
AI and Machine Learning Implications
Social media platforms increasingly use artificial intelligence to analyze content, predict behavior, and create detailed user profiles. These systems can infer sensitive information including health conditions, financial status, political views, and relationship dynamics from seemingly innocent posts and interactions.
Current AI Privacy Risks:
- Facial recognition and biometric data extraction from photos- Behavioral analysis predicting future actions and interests- Sentiment analysis revealing emotional and mental health patterns- Social graph analysis exposing relationships and influence networks
Protection Strategies:
- Minimize facial photos and use privacy-focused image editing- Vary posting patterns to confuse behavioral algorithms- Use privacy-focused social media alternatives when possible- Regularly review and object to AI training data usage
Regulatory and Legal Developments
Privacy regulations like GDPR, CCPA, and emerging state-level laws provide new rights and protections, but require active user engagement to implement effectively.
Current Privacy Rights:
- Right to access collected data through platform download tools- Right to deletion (though implementation varies significantly)- Right to object to certain data processing activities- Right to data portability for switching platforms
Future Regulatory Trends:
- Increased restrictions on cross-platform data sharing- Enhanced protections for children and teenagers- Stricter consent requirements for AI training data usage- Greater transparency requirements for algorithmic content curation
Maintaining Long-Term Social Media Privacy
Ongoing Privacy Maintenance
Monthly Tasks:
- Review privacy settings for changes or new features- Audit connected applications and remove unused services- Check active device sessions and remove unrecognized access- Update passwords and security questions as needed
Quarterly Tasks:
- Complete comprehensive privacy settings review across all platforms- Download and review collected data to understand platform knowledge- Update emergency contacts and account recovery information- Assess overall privacy risk profile and adjust strategies accordingly
Annual Tasks:
- Conduct complete social media privacy audit with updated threat models- Review and update family/children’s privacy protection strategies- Evaluate new platforms and privacy tools for potential adoption- Update legal and business entity information for professional accounts
Building Privacy-Conscious Social Media Habits
Content Sharing Best Practices:
- Implement the “public scrutiny test”—assume every post could become public- Use privacy-focused alternatives for sensitive communications- Regularly clean up old posts that no longer reflect current privacy preferences- Maintain consistent privacy practices across all platforms and devices
Social Engineering Resistance:
- Be skeptical of unsolicited friend requests, especially from attractive strangers- Avoid sharing personal information that could be used for identity verification- Resist social pressure to share location, financial, or family information- Verify requests for sensitive information through alternative communication channels
Social Media Risk Assessment Tool
The Path Forward: Reclaiming Your Digital Privacy
Social media privacy protection isn’t about retreating from digital connection—it’s about engaging on your terms with appropriate protections in place. The strategies outlined in this guide provide comprehensive protection against current threats while positioning you to adapt to future privacy challenges.
Immediate Action Steps:
- Complete our Social Media Privacy Risk Assessment to understand your current vulnerability level2. Implement basic security measures across all platforms (two-factor authentication, password updates, permission reviews)3. Configure platform-specific privacy settings using our detailed guides above4. Establish ongoing maintenance routines to keep protections current and effective
Long-term Privacy Strategy:
- Stay informed about platform policy changes and new privacy features- Regularly reassess your social media usage and privacy needs- Consider privacy-focused alternatives as they mature and gain adoption- Maintain awareness of emerging threats and protection techniques
Your social media privacy is ultimately about maintaining control over your digital identity and personal information in an increasingly connected world. By implementing these comprehensive protection strategies, you can enjoy the benefits of social media connection while minimizing the risks to your privacy, security, and personal well-being.
The choice is yours: continue operating with default settings that prioritize platform profits over your privacy, or take control with evidence-based protection strategies that put your interests first. Your digital freedom depends on the actions you take today.
Ready to secure your social media presence? Start with our free Privacy Risk Assessment to identify your specific vulnerabilities and receive personalized protection recommendations. Your comprehensive social media privacy strategy begins with understanding exactly what you need to protect.
Social Media Risk Assessment Tool