The DOJ’s 3-million-page document dump didn’t just expose financiers and politicians — it pulled back the curtain on a sophisticated technical operation. One man sits at the center of it all, and he’s never been called to testify.
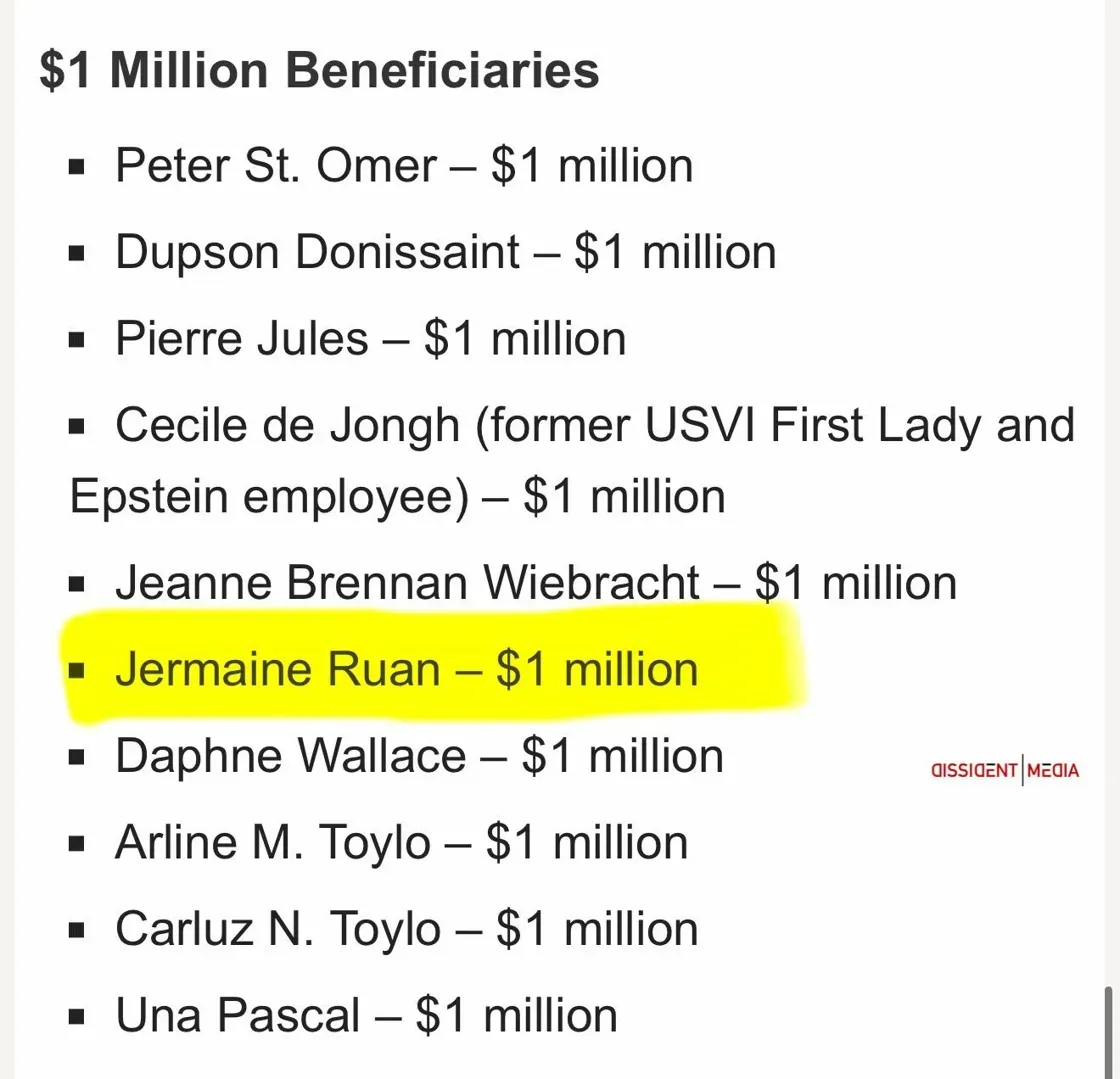
When investigators and citizen researchers began combing through the Department of Justice’s massive release of Epstein files in early 2026, most eyes went to the famous names — politicians, royals, billionaires. But buried in technical emails, island handbooks, and procurement logs was something that cybersecurity professionals immediately recognized: a surprisingly sophisticated surveillance and networking infrastructure, built and maintained by a single IT manager who inherited $1 million from Epstein’s estate and now works for the US Virgin Islands Bureau of Corrections.
His name is Jermaine Ruan. And he has never once been subpoenaed.
The IT Manager Who Built Epstein’s Surveillance Empire
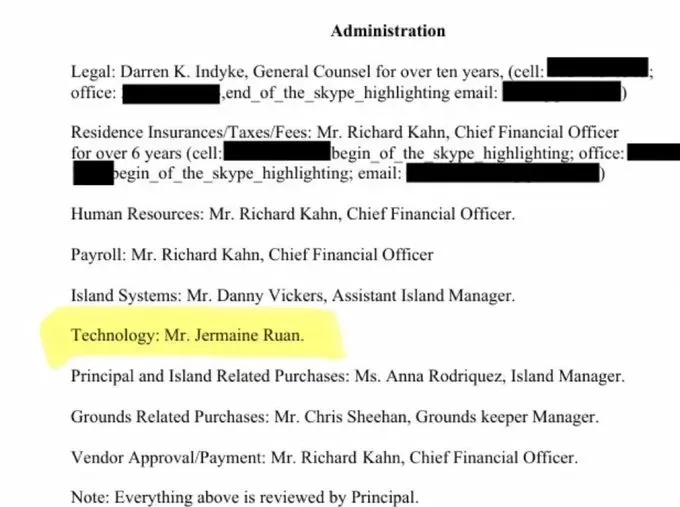
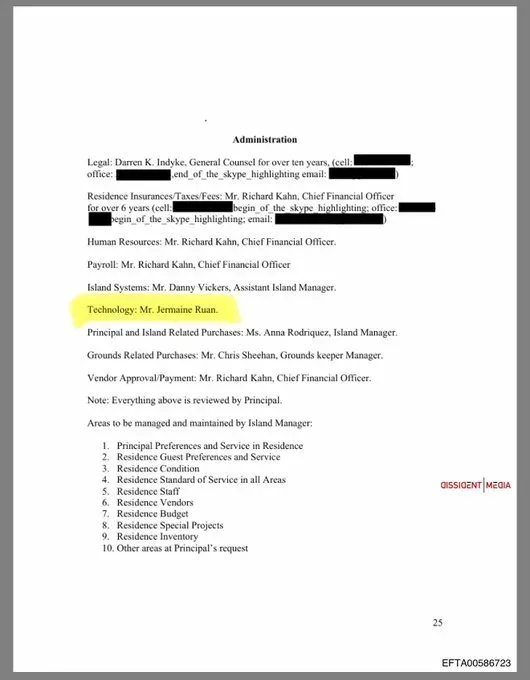
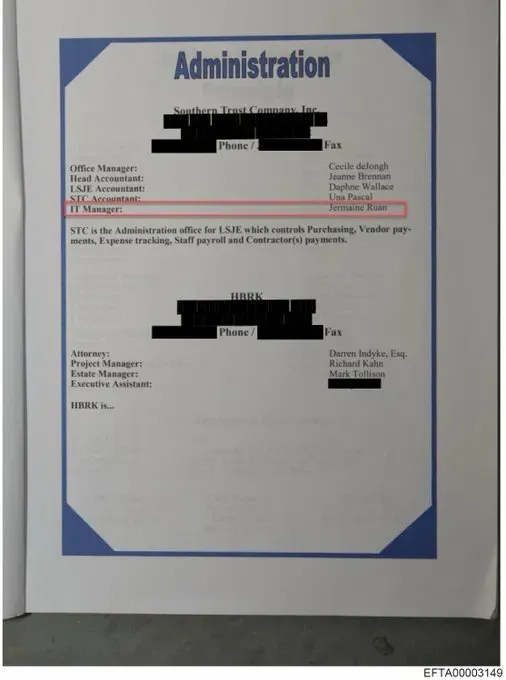
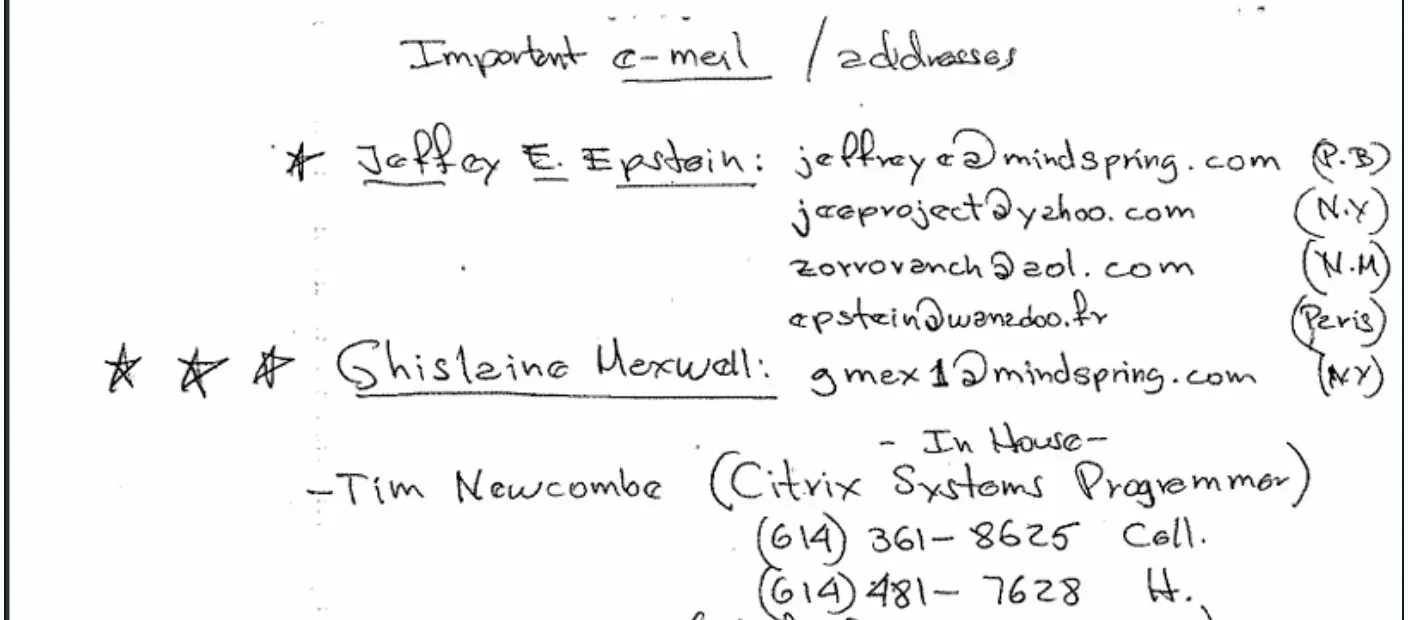
The documents paint a clear picture of Ruan’s role. He appears on page 25 of the Little Saint James Island Handbook under a simple entry: “Technology: Mr. Jermaine Ruan.” In a separate administration document for Epstein’s Southern Trust Company, Ruan is listed as IT Manager — a position that put him at the center of every camera, network, and communications system across Epstein’s properties.
What exactly did that involve? The DOJ documents reveal a sprawling technical buildout:
Cloud-Based Surveillance Cameras
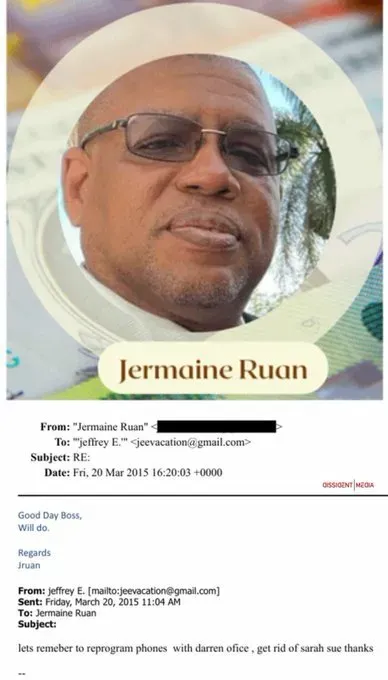
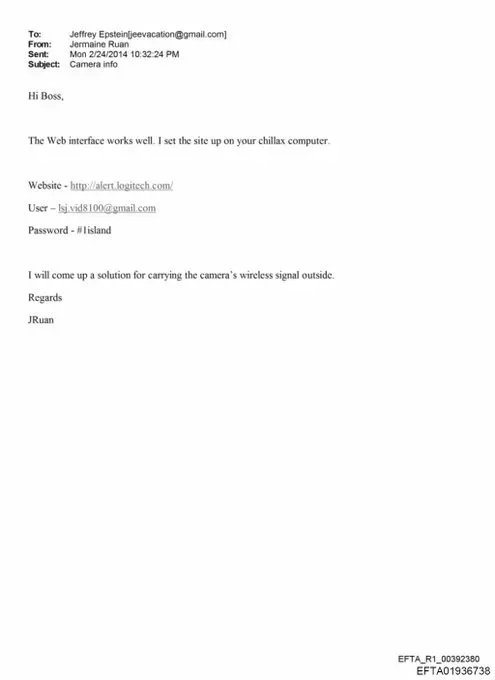
A 2014 email from Ruan to Epstein — addressed “Hi Boss” — references a Logitech Alert camera system with full cloud storage. Ruan set the system up on Epstein’s “chillax computer” and provided login credentials, promising to “come up a solution for carrying the camera’s wireless signal outside.” The significance here is enormous: Logitech’s cloud servers may still contain surveillance footage from Epstein’s island — footage that investigators never subpoenaed and that Epstein could not have destroyed.
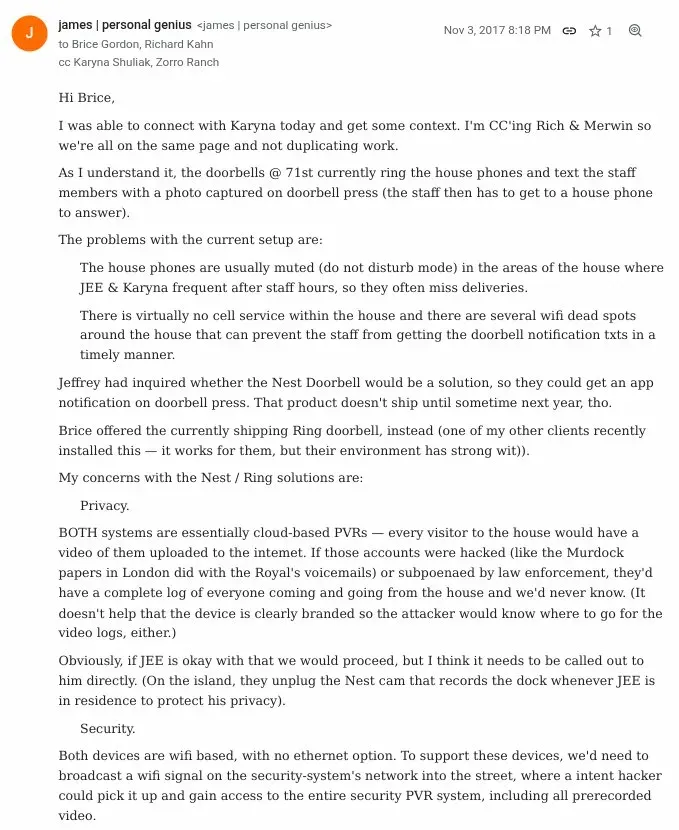
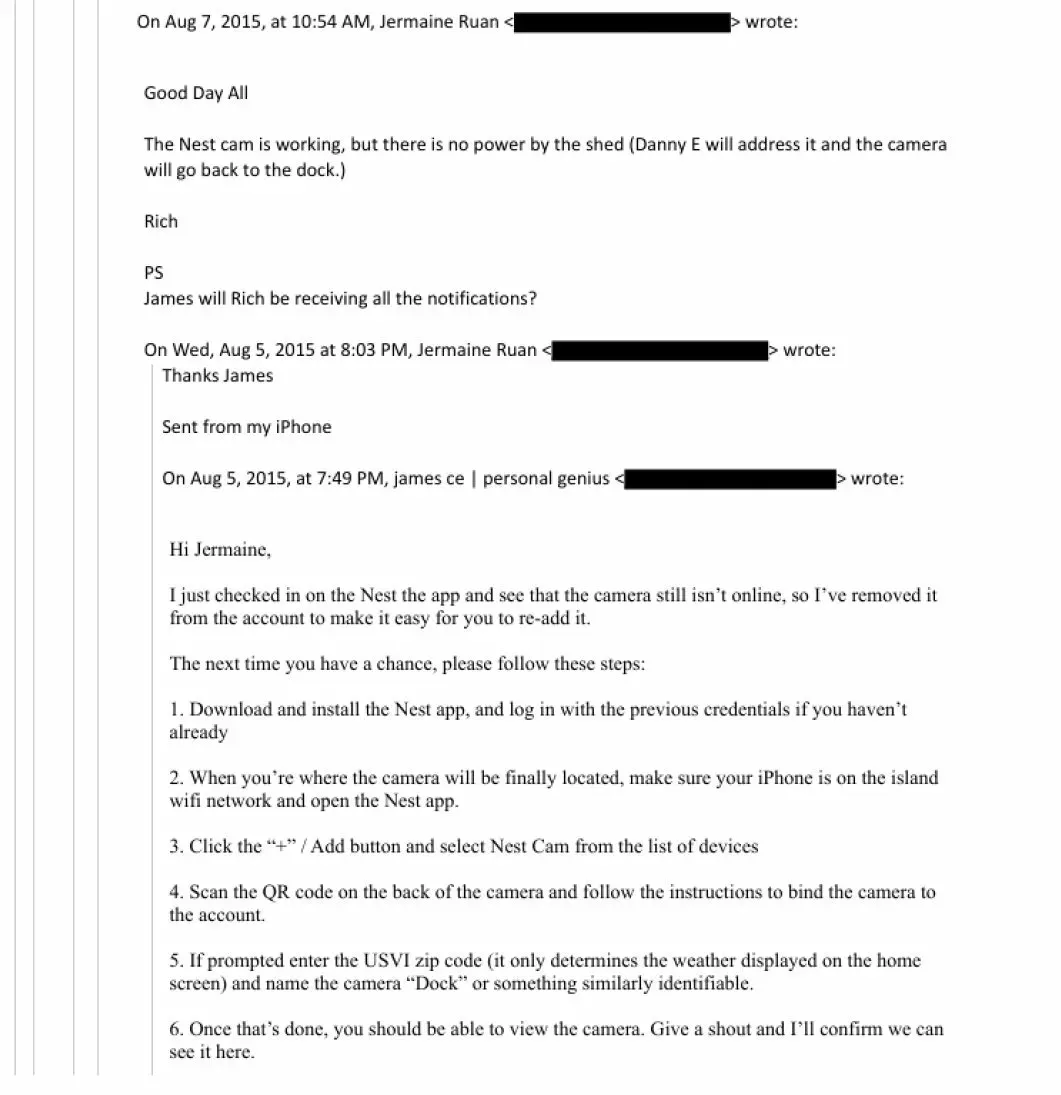
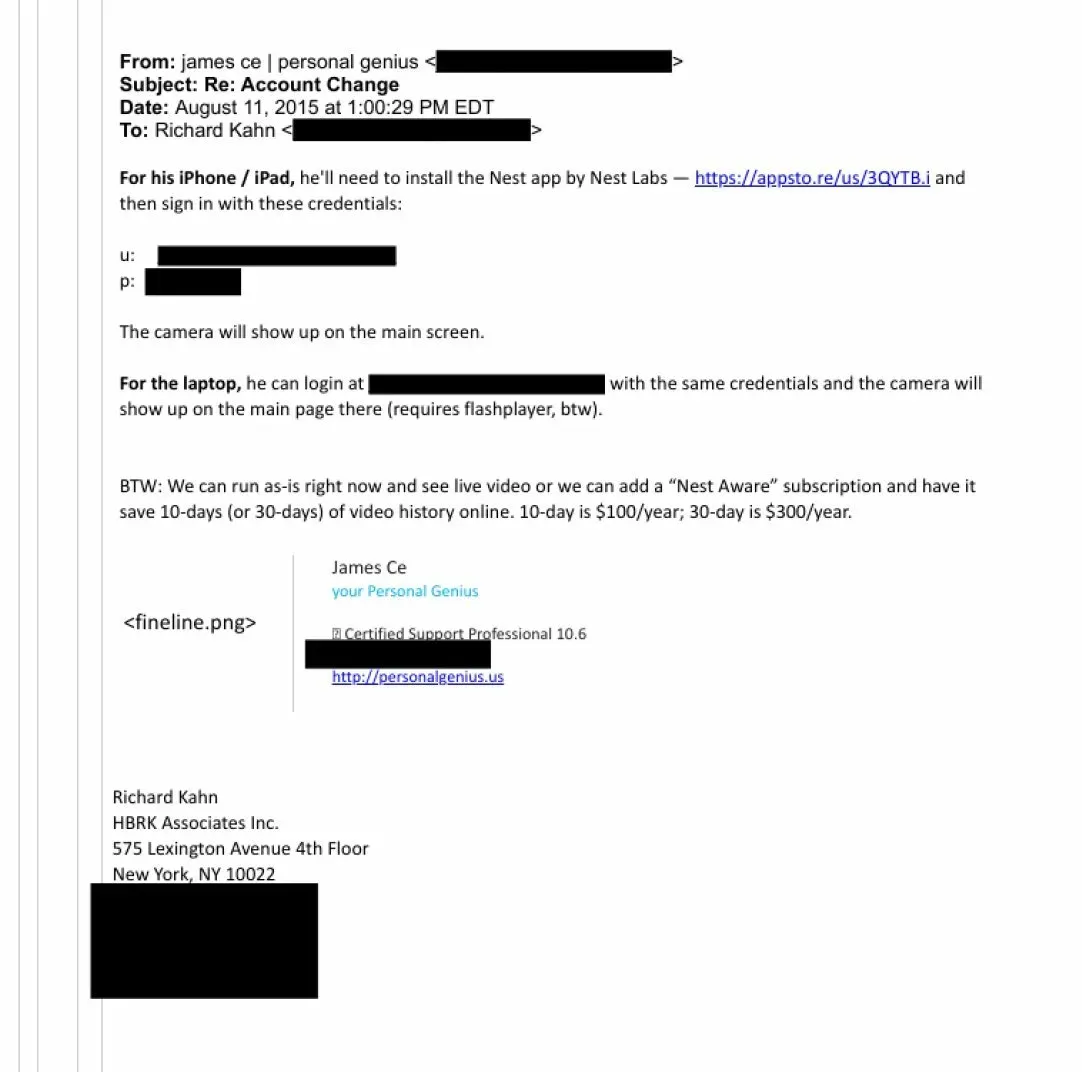
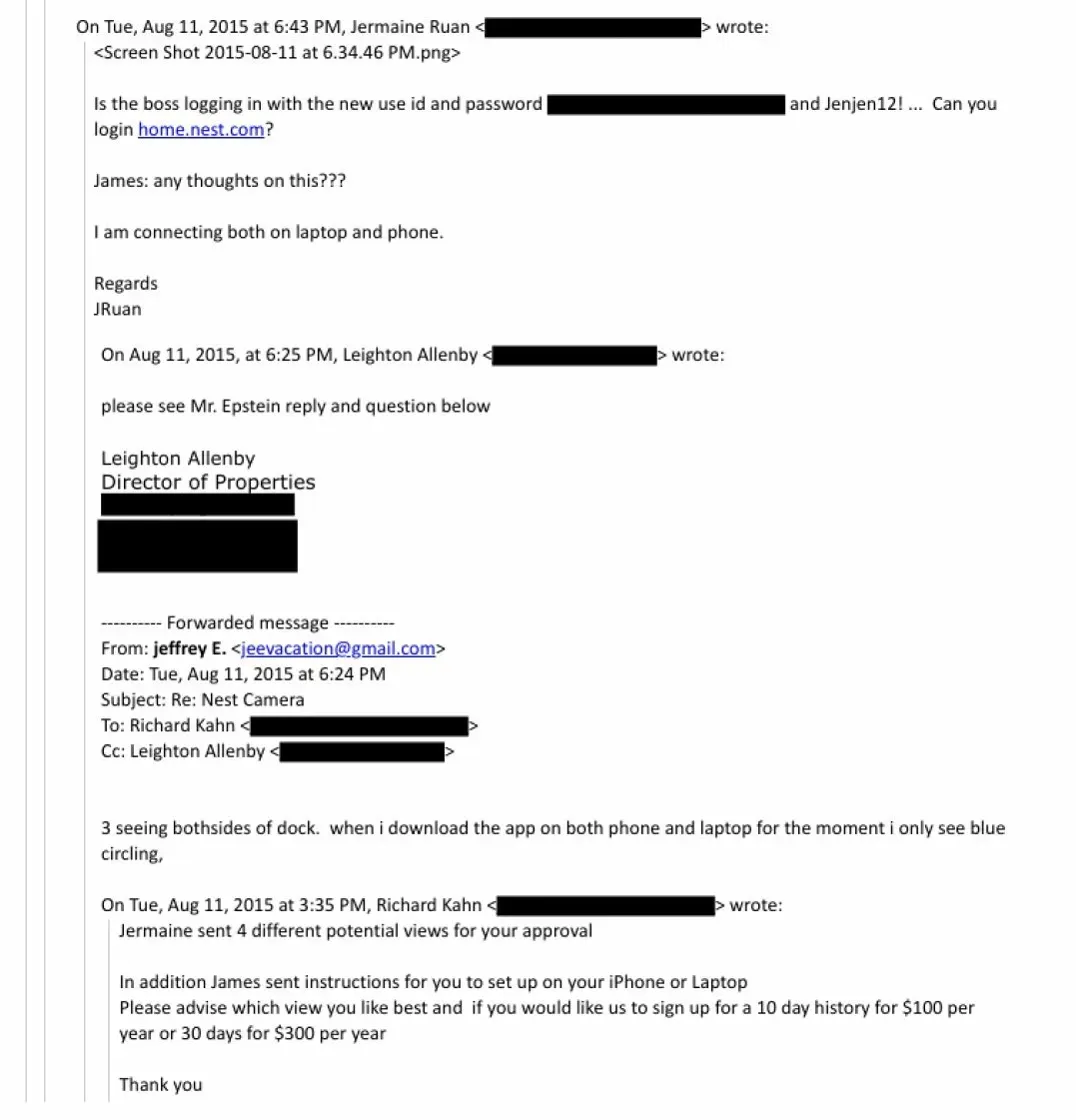
By 2015, Ruan was also coordinating the installation of Nest cameras on Epstein’s dock, working through Richard Kahn (CFO), a tech consultant called “james | personal genius,” and Epstein directly. A thread of emails discusses camera placement, account credentials, and viewing options. Critically, a November 2017 email from “james | personal genius” to Brice Gordon and Richard Kahn flags a key OPSEC observation: “On the island, they unplug the Nest cam that records the dock whenever JEE is in residence to protect his privacy.” The staff was manually disabling cloud-connected cameras whenever Epstein arrived. Someone on the inside was thinking about operational security long before Epstein was arrested.

Enterprise-Grade Networking
By late 2017, Ruan was reaching out to Ubiquiti Networks — a company known for enterprise Wi-Fi and surveillance-grade camera systems — requesting quotes for a comprehensive infrastructure overhaul of Little Saint James. A January 2018 email shows Ruan compiling an “LSJ AMAZON LIST” of Ubiquiti gear. Epstein’s two-word response: “order today.”
Court-recognized digital forensics expert Steven Burgess, reviewing photographs of the installed equipment for research firm Hunterbrook, described the resulting setup as “an enterprise-grade communications operation capable of supporting 800 to 1,000 devices.” This was not a vacation home Wi-Fi setup. This was a deliberately built communications infrastructure.
Ruan’s emails also document fiber optic infrastructure across Zorro Ranch in New Mexico, where he oversaw a self-contained communications network. When fiber was damaged across parts of the island, Ruan coordinated wireless bridge installations to keep all areas connected. He understood both the physical and network layers of these systems.
The “Test” Email Sent in June 2019
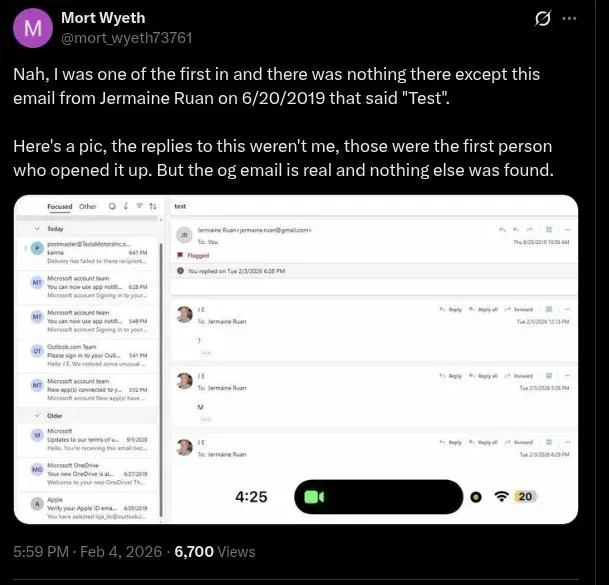
Perhaps the strangest data point: when the DOJ files were released and citizen researchers found what appeared to be Epstein’s Outlook password in the documents (the credential “#1Island” appears in a 2014 email from Ruan to Epstein), some users reported logging into the account. According to screenshots circulated on social media and reported by IBTimes, the account was largely empty — except for one email dated June 20, 2019, from Jermaine Ruan, with the subject line “Test” and a blank body.
That date is roughly six weeks before Epstein died in federal custody. Whether that email represents a routine system check or something more significant, only Ruan could say. He hasn’t been asked.
The Southern Trust Connection: DNA, Algorithms, and Rothschild Money
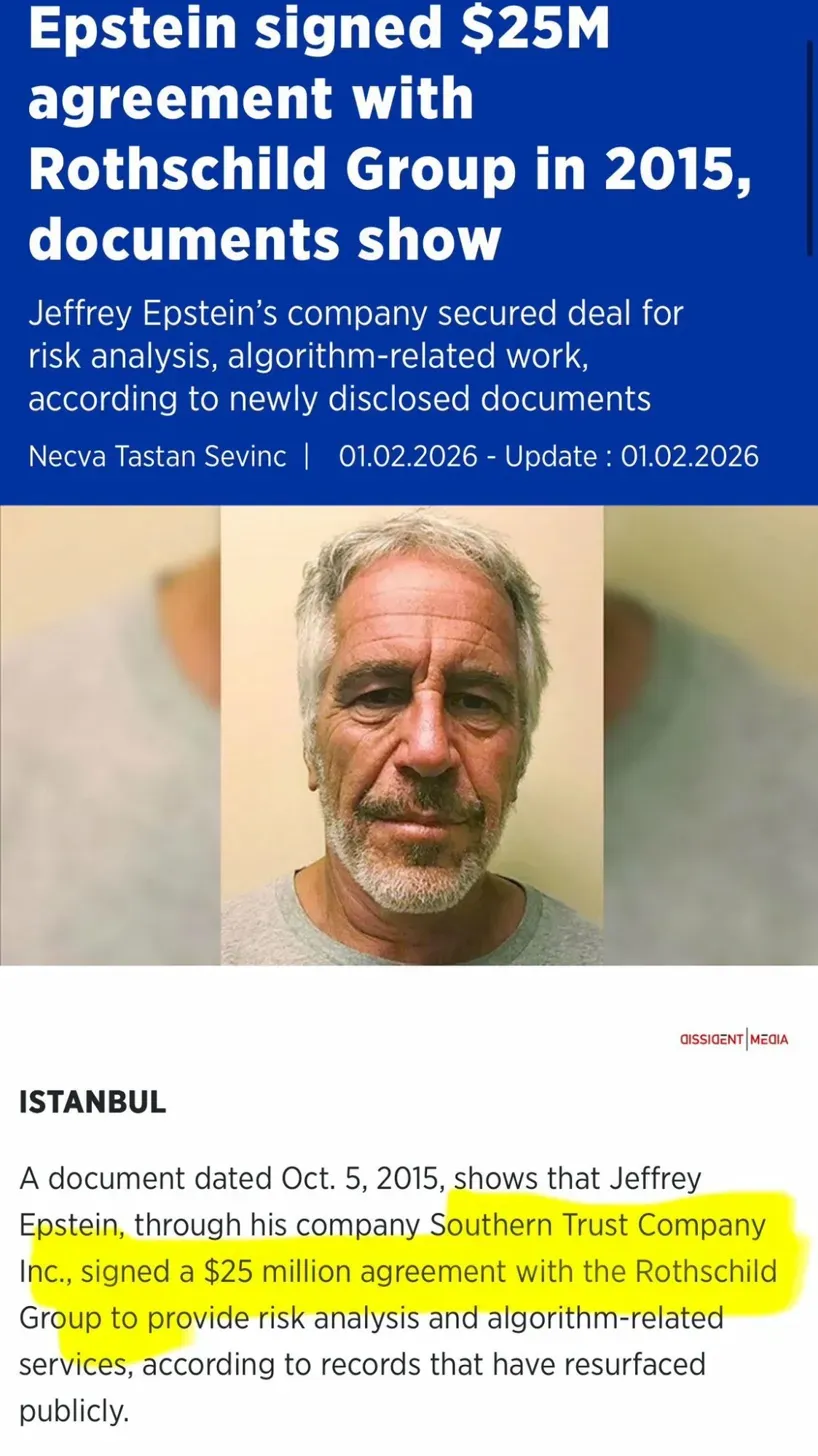
Ruan’s IT role extended beyond the islands. He was listed as IT Manager of Southern Trust Company, Inc. — Epstein’s USVI-registered entity that, on paper, described itself as a “DNA database consulting and data analysis company.”
The reality was more complex. Southern Trust secured significant Economic Development Commission tax benefits by claiming it conducted cutting-edge genetic research for medical organizations. Investigators found no evidence of legitimate scientific work. Instead, it functioned primarily as a financial vehicle — managing payments, contractor compensation, and asset transfers across Epstein’s network.
Southern Trust also had a $25 million contract with the Edmond de Rothschild Group, signed in October 2015, for “risk analysis and the application and use of certain algorithms.” Whether Ruan’s IT management role touched any of those technical operations is unknown. What is known is that he was the designated technology point of contact for an organization receiving tens of millions in financial contracts.
DEF CON Bans Three: The Hacker World’s Epstein Reckoning
While Ruan has flown under the radar, the cybersecurity conference community has not been so quiet about its own connections to Epstein.
In February 2026, DEF CON — one of the world’s largest and longest-running hacking conferences — publicly added three individuals to its banned list after their names surfaced in the DOJ document release:
Vincenzo Iozzo, CEO of identity management firm SlashID and former CrowdStrike director, was in contact with Epstein between 2014 and 2018. He offered to procure DEF CON badges for Epstein and reportedly visited Epstein’s New York residence multiple times. An FBI document released in the files, as reported by Nextgov/FCW, closely links him to the description of someone described by a bureau informant as “Epstein’s personal hacker.” A spokesperson for Iozzo called the ban “entirely performative” and “a rush to judgment.”
Pablos Holman, now a general partner at venture capital firm Deep Future, had contact with Epstein dating to 2010. Emails show he worked with Epstein associate Al Seckel to scrub negative Epstein coverage from Google search results for approximately $25,000. He also planned to stay at Epstein’s New York apartment in 2013 and appears to have coordinated DEF CON attendance with Epstein.
Joichi “Joi” Ito, former director of the MIT Media Lab, resigned from that role in 2019 when his financial relationship with Epstein became public. The DOJ documents renewed scrutiny. Ito and Iozzo appear in multiple Epstein emails together.
Black Hat, DEF CON’s corporate sister conference, also quietly removed Iozzo from its review board pages in the weeks following the document release. Code Blue, a Japanese security conference, followed suit.
DEF CON founder Jeff Moss stated he has “never met or been introduced to Jeffrey Epstein” and that, to his knowledge, Epstein never attended DEF CON — though emails show Epstein actively sought to. In one 2016 message to Iozzo, Epstein wrote that he hoped to attend with several people, including former Israeli Prime Minister Ehud Barak, billionaire Tom Pritzker, and “four girls.”
The OPSEC Picture: More Careful Than Anyone Realized
One of the more striking revelations from the IT-related documents is how deliberately Epstein managed his technical exposure. Beyond unplugging dock cameras on arrival, the November 2017 security email from “james | personal genius” explicitly warned against Nest and Ring doorbell cameras because both systems are cloud-based, meaning every visitor’s image would be uploaded to company servers — servers that could be hacked or subpoenaed.
The memo raised concerns about:
- Privacy: Cloud PVR systems would create a permanent log of everyone entering and leaving, accessible to law enforcement via subpoena or to hackers via account compromise- Security: Both Nest and Ring required broadcasting Wi-Fi onto Epstein’s security network, potentially exposing the entire PVR system to outside access- Brand visibility: The clearly branded devices would advertise which cloud services to target
The concern wasn’t consumer paranoia. It was the kind of analysis you’d see in a corporate threat model — or a TSCM (Technical Surveillance Countermeasures) assessment. Someone in Epstein’s orbit understood surveillance security at a professional level.
Which raises the central unanswered question: if Epstein’s team was this deliberate about managing camera footage, what did they do with recordings that did exist? And who had the technical knowledge and access to answer that question?
Jermaine Ruan — listed as the technology point of contact for Epstein’s island, Zorro Ranch, and Southern Trust — has the answers. He currently earns $69,890 annually as a Management Information System Administrator for the US Virgin Islands Bureau of Corrections. He has never been subpoenaed by Congress or federal investigators.
The Nest Account That May Still Have Data
The images emerging from the DOJ document release add a layer of specificity that changes the conversation entirely.
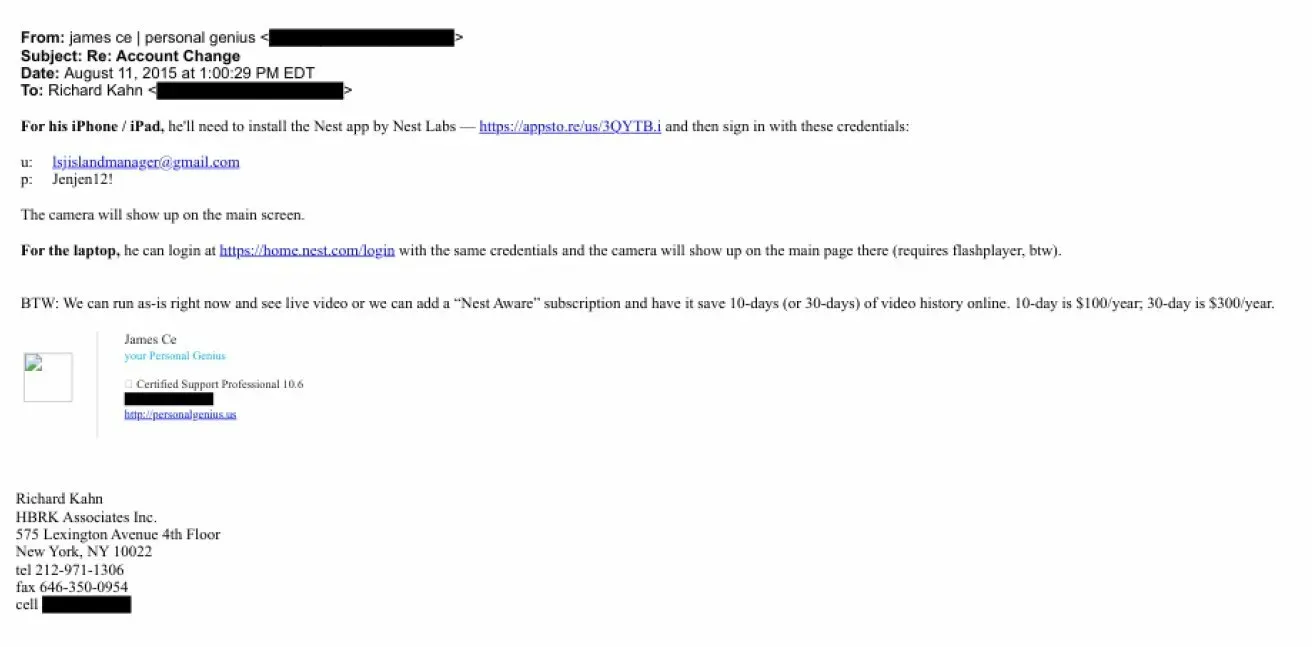
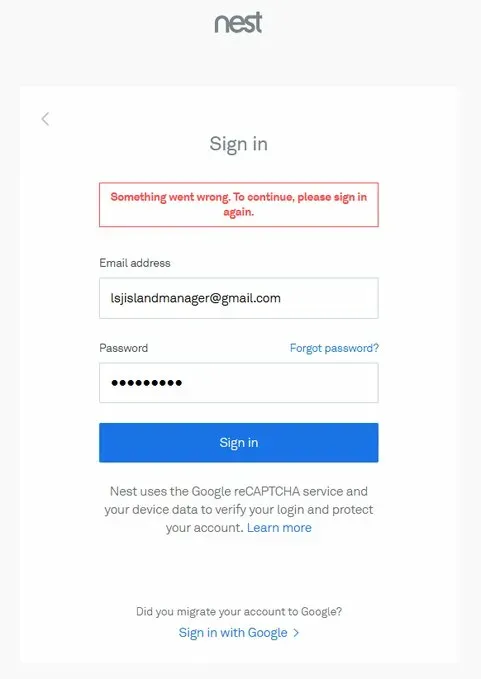
A 2015 email from “james | personal genius” to Richard Kahn — with Epstein CC’d at his jeevacation@gmail.com address — reveals the actual Nest account credentials used to manage the island dock camera:
- Username: lsjislandmanager@gmail.com- Password: Jenjen12! (as it appeared in the 2015 email)
That account, set up for Epstein’s Little Saint James island, was the central login for at least one Nest camera system monitoring the dock. The email notes the account worked on both iPhone/iPad via the Nest app and on laptop via home.nest.com, and discussed the “Nest Aware” subscription option that would store 10 to 30 days of video history in Google’s cloud for $100–$300 per year.
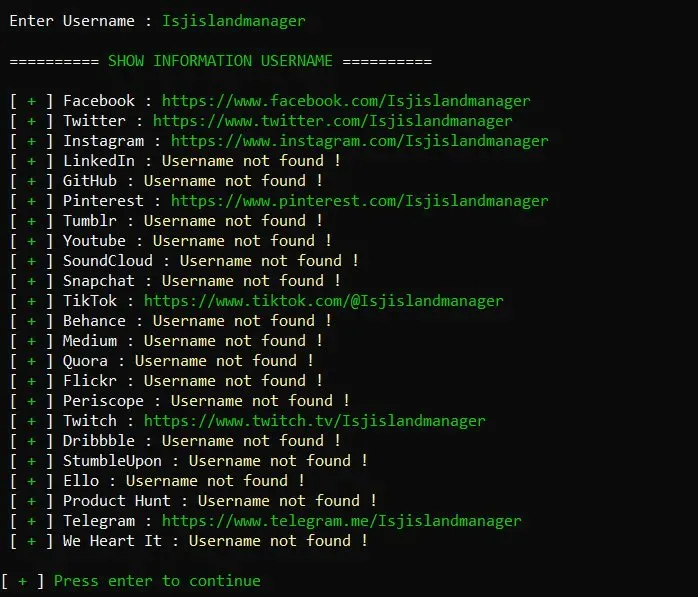
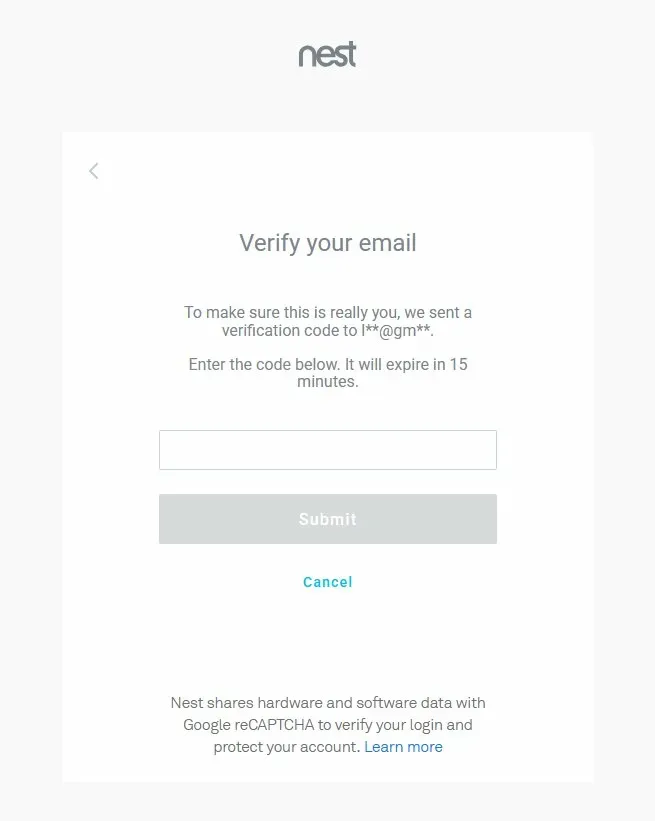
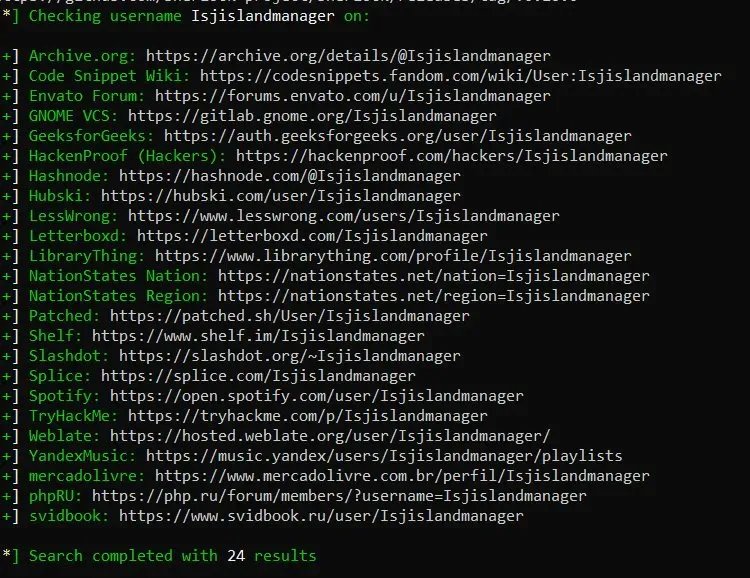
Researchers who have run OSINT analysis on the username “lsjislandmanager” have found the account registered across dozens of platforms — Facebook, Twitter, Pinterest, TikTok, Telegram, Spotify, and others — suggesting the Gmail account behind it was actively used and linked to a broader identity footprint. Screenshots of attempted Nest logins show the account still exists in Google’s system, triggering a two-factor verification email sent to a redacted Gmail address.
That verification step matters. It means Google’s systems still recognize this account. Which brings us to the question no one has officially asked: has anyone ever served Google a warrant for the backend data associated with lsjislandmanager@gmail.com?
Chain of Custody Crisis: Digital Evidence Integrity in the Jeffrey Epstein Case
The Nancy Guthrie Precedent Changes Everything
In February 2026, a case emerged that directly answers the question of whether Google retains Nest footage even when cameras are disconnected and no paid subscription exists.
Nancy Guthrie — mother of NBC’s Today Show host Savannah Guthrie — was abducted from her Arizona home. Investigators discovered her Nest Video Doorbell had been tampered with and removed before her disappearance. She was not a Nest Aware subscriber. By Google’s own stated policy, event video is deleted on a rolling basis within hours for non-subscribers.
Ten days after her abduction, the FBI released surveillance footage of the apparent abductor. The footage came from her Nest camera. In a statement, the FBI wrote that the video was “recovered from residual data located in backend systems” — and that they had been “working closely with our private sector partners” to retrieve it.
TechRadar’s reporting confirmed Guthrie had no active subscription, which ordinarily means video is deleted within hours. The FBI’s recovery of footage from “backend systems” raises significant questions about what Google actually retains, even for non-subscribers, and under what circumstances that data becomes accessible to law enforcement. Ring’s founder was asked directly about his own platform and stated clearly that without a subscription or saved recording, Ring doesn’t store the data. Google has offered no equivalent clarity.
This has direct implications for the Epstein investigation. The lsjislandmanager@gmail.com Nest account was registered to camera equipment on a heavily trafficked dock at one of the most significant crime scenes in modern federal investigation history. If Google retained backend data in the Guthrie case without a subscription — which the FBI’s own statement confirms — similar backend data from the Epstein Nest account may still exist in Google’s systems, covering years of activity including periods when cameras were supposedly unplugged before Epstein’s arrivals.
A warrant for that account has reportedly never been served.
For deeper context on what this means for the broader surveillance-as-a-service ecosystem, see our coverage: The Doorbell Surveillance State: Smart Doorbells, Law Enforcement Partnerships, and the 67 Million Daily Strangers at Your Door and Deleted Doesn’t Mean Gone: What the Nancy Guthrie Case Exposed About Your Smart Camera.
What Investigators Should Be Looking At
From a technical forensics standpoint, the Epstein IT trail raises several unresolved threads:
Logitech cloud servers: The 2014 Ruan email explicitly references setting up Logitech Alert camera access via a web interface with cloud storage. Logitech’s servers may retain years of footage. These have never been formally subpoenaed, to public knowledge.
The lsjislandmanager Nest account (Google): The 2015 email chain shows Epstein’s island dock was monitored via the lsjislandmanager@gmail.com Nest account. The Nancy Guthrie case demonstrates that Google retains backend camera data even for non-subscribers, beyond what its consumer-facing policy describes. This account should be the subject of a federal warrant. The account appears to still exist in Google’s system.
Ubiquiti network logs: The enterprise-grade Ubiquiti infrastructure deployed across Little Saint James would generate detailed network logs — device connections, data transfers, access patterns. Those logs either still exist on local hardware or were exported.
The Outlook account: If the account referenced in the DOJ files was still accessible and Ruan sent a test email to it in June 2019, Microsoft would have server logs of that activity.
Ruan’s testimony: As the person who physically installed, configured, and maintained these systems across multiple Epstein properties spanning more than a decade, Ruan has technical knowledge that no document release can substitute for.
The Broader Pattern
The Epstein case has always had a technology dimension that received far less scrutiny than the social and financial networks. The documents that have now surfaced show that someone — likely multiple people — was thinking carefully about surveillance, network security, and data exposure in ways that suggest either sophisticated personal knowledge or access to professional technical advice.
The cybersecurity community’s own reckoning, evidenced by the DEF CON bans and the scrutiny now falling on figures like Iozzo, suggests that Epstein’s network extended into technical and security circles in ways that are still being mapped.
What’s clear from the documents alone: Epstein’s technical infrastructure was deliberately designed, professionally maintained, and capable of storing significant amounts of data. Some of that data may still exist on commercial cloud servers. The one person with comprehensive knowledge of where all of it went has never been asked to explain.
Related coverage from our network:
myprivacy.blog:
- Citizen Coders Built a Dark Google to Search the Epstein Files — Because the Government Wouldn’t
- Chain of Custody: Digital Evidence and Forensics in the Epstein Case
- February 2026: The Epstein Files Explode
- The Digital Safety Theater: How Child Protection Became the Trojan Horse for Global Surveillance
secureiot.house:
- The Doorbell Surveillance State: A Technical and Statistical Analysis of Smart Doorbells, Law Enforcement Partnerships, and the 67 Million Daily Strangers at Your Door- Deleted Doesn’t Mean Gone: The Nancy Guthrie Case Just Exposed the Uncomfortable Truth About Your Smart Camera
Published on myprivacy.blog | Part of the CISO Marketplace cybersecurity content network