How a Chinese spy forging a governor’s signature and the Biden auto-pen controversy expose the most dangerous insider threat vector
🎧 Related Podcast Episode
Executive Summary
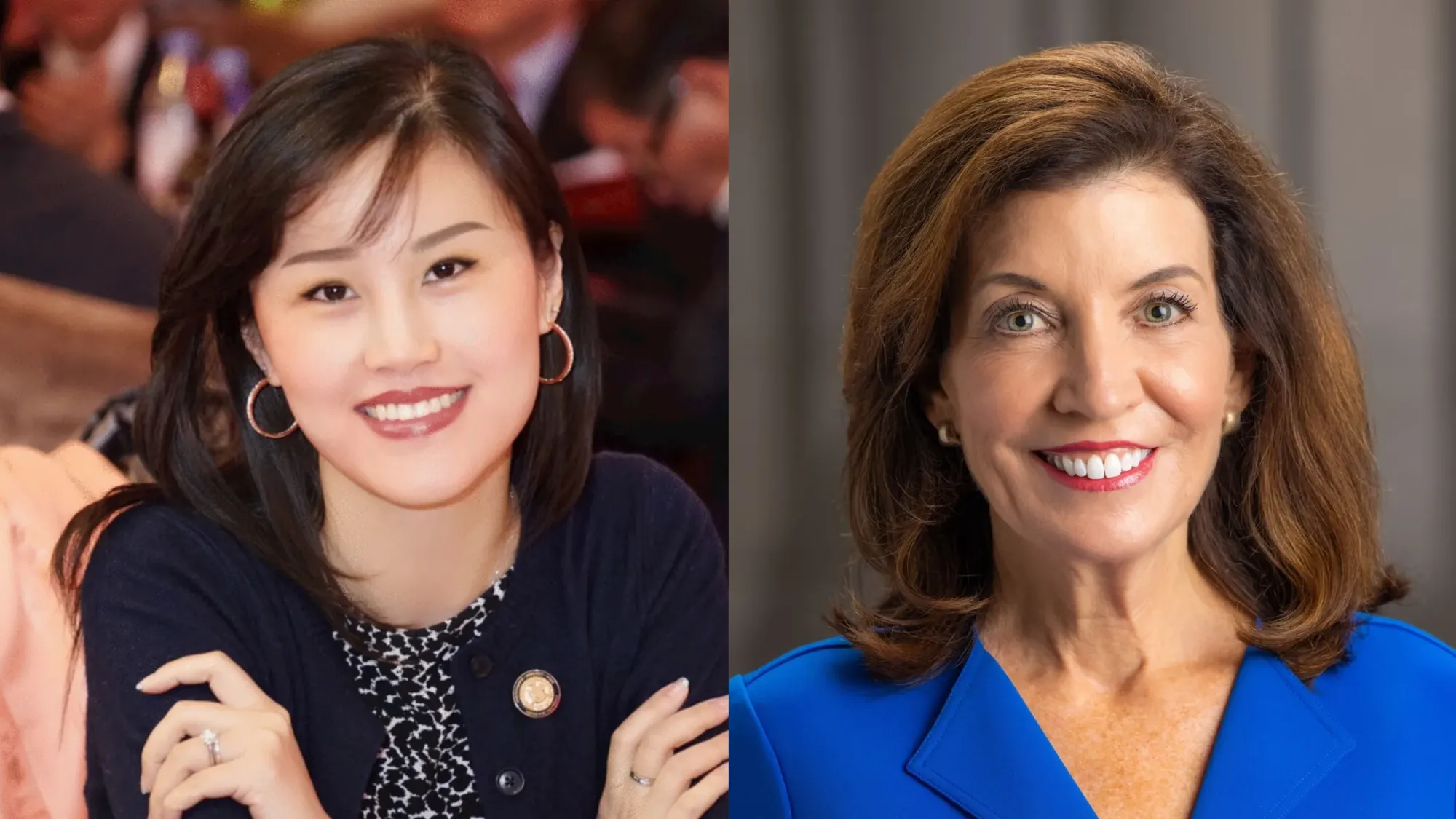
In November 2025, bombshell testimony revealed that Linda Sun, a former top aide to New York Governor Kathy Hochul, brazenly forged the governor’s signature multiple times to facilitate meetings between Chinese Communist Party officials and New York’s highest government offices. This revelation should be dominating national headlines—not because of political theater, but because it exposes a critical vulnerability in how we think about insider threats.
 Combined with the ongoing House Oversight Committee investigation into the Biden administration’s use of auto-pen signatures on executive actions and pardons, these cases illuminate a sophisticated attack vector that traditional cybersecurity frameworks consistently miss: the weaponization of signature authority by trusted insiders.
Combined with the ongoing House Oversight Committee investigation into the Biden administration’s use of auto-pen signatures on executive actions and pardons, these cases illuminate a sophisticated attack vector that traditional cybersecurity frameworks consistently miss: the weaponization of signature authority by trusted insiders.
Bottom Line Up Front: When insiders with legitimate access abuse signature authority—whether through forgery or unauthorized use of auto-pen technology—they can exercise executive power without authorization, compromise national security, facilitate foreign influence operations, and undermine the fundamental chain of command that underpins governmental legitimacy.
The Linda Sun Case: Signature Forgery as State-Sponsored Espionage
The Anatomy of a Perfect Insider Threat
Linda Sun’s infiltration of New York state government represents what cybersecurity professionals call the “perfect insider threat”—one that combines legitimate access, advanced social engineering, and foreign state sponsorship. From 2012 to 2023, Sun held multiple senior positions across New York state government:
- Director of Asian-American Affairs under Governor Andrew Cuomo- Chief Diversity Officer at the New York State Department of Financial Services- Deputy Chief of Staff to Governor Kathy Hochul
This progression gave Sun something more valuable than network access or database credentials: she gained signature authority proximity—the ability to create, route, and authenticate documents bearing executive signatures.





The Forgery Operation: How It Worked
According to federal prosecutors and testimony presented at Sun’s trial in Brooklyn federal court, the signature forgery scheme operated with disturbing sophistication:
The Setup (March 2018):
- A Chinese consulate official provided Sun with a list of Communist Party delegation members from Henan Province- The official handed Sun an English-language document titled “Reference of Invitation Letter” for Hochul’s signature- Sun was tasked with arranging for the delegation to travel to the U.S. and meet with then-Lieutenant Governor Hochul
The Execution:
- On March 29 and April 5, 2018, Sun provided the Chinese official with two versions of invitation letters from the governor’s office- Sun relied on language from a previously authorized invitation letter for a different Chinese delegation (from Jiangxi Province)- Most critically: Sun forged Hochul’s signature on the letters by hand
The Detection:
- When prosecutors presented the forged letters to the jury, Hochul’s former chief of staff Jeff Lewis immediately identified the forgeries- The signatures featured “overly loopy” handwriting inconsistent with Hochul’s actual signature- Lewis testified: “From my experience, this is not how she would sign her name. The ‘K’ is different than it typically would be.”
Why This Matters More Than You Think
Sun didn’t hack a database. She didn’t exploit a zero-day vulnerability. She didn’t even need to steal credentials. She simply forged a signature—and in doing so:
- Facilitated Chinese intelligence operations on American soil2. Compromised visa application processes for foreign nationals3. Created fraudulent government documents that appeared legitimate4. Exercised executive authority without authorization5. Enabled face-to-face meetings between CCP officials and New York’s executive leadership
Governor Hochul’s response captured the severity: “Lying and misleading these administrations, breaking our ethics rules, and even forging my signature on documents. But even more importantly, this is a betrayal of New Yorkers and the American people.”
The Compensation Package: Following the Money
While Sun’s official salary was $145,000, the benefits she received from her Chinese handlers painted a picture of systematic state-sponsored corruption:
Financial Benefits:
- Millions of dollars in contracts steered to her husband Chris Hu’s seafood exporting business- $3.6 million mansion in Long Island- $1.9 million condominium in Hawaii- 2024 Ferrari Roma (valued at $243,360-$277,970)- 2022 Mercedes GLB SUV
Luxury Items:
- Multiple Hermès Birkin handbags (discovered in orange boxes by FBI)- Rolex watches- Patek Philippe timepieces- Pearl necklaces
Personal Perks:
- Nanjing-style salted ducks prepared by a Chinese consul’s personal chef and delivered to Sun’s parents- Business cards of Chinese government officials found in jewelry boxes
Beyond Forgery: The Full Scope of Influence Operations
The signature forgery was just one component of Sun’s broader influence campaign:
COVID-19 Pandemic Exploitation:
- Secretly added Chinese consulate officials to private conference calls about New York’s pandemic response in March 2020- Helped steer lucrative contracts for masks and ventilators to Chinese companies- Later charged with additional counts related to pandemic-era procurement fraud
Taiwan Suppression:
- Blocked Taiwanese officials from accessing the governor’s office- Edited press releases to remove references to Taiwan as a country- Prevented Governor Cuomo from publicly thanking Taiwan for assistance
Uyghur Censorship:
- Argued with Hochul’s speechwriter who wanted to mention the “Uyghur situation” in China- Successfully removed all references to Uyghurs from Hochul’s Chinese New Year message- Chinese Consulate in New York posted the sanitized message on their Facebook page
The Biden Auto-Pen Controversy: When Legitimate Technology Enables Illegitimate Authority
From Mechanical Convenience to Constitutional Crisis
While Linda Sun’s case involves old-fashioned signature forgery, the Biden auto-pen investigation exposes a more insidious vulnerability: the abuse of legitimate signature technology to obscure who actually exercises executive authority.
An auto-pen (or autopen) is a mechanical device that reproduces a person’s signature using a pen or writing instrument. Presidents have used this technology since Thomas Jefferson purchased one shortly after its patent in 1803. However, the House Oversight Committee’s investigation alleges something unprecedented: the systematic use of auto-pen technology to sign executive actions while concealing cognitive decline and unclear chains of command.
The House Oversight Committee’s Findings
On October 28, 2025, the House Oversight Committee released a 93-page report titled “The Biden Autopen Presidency: Decline, Delusion, and Deception in the White House.” The committee’s findings are striking:
Key Allegations:
- The “vast majority” of Biden’s executive actions were signed using auto-pen rather than hand signature- Auto-pen use increased during the second half of Biden’s presidency when cognitive decline was most apparent- Former Biden White House staffers expressed “degrees of confusion” about decision-making processes- No clear record exists demonstrating “Biden himself made all of the executive decisions that were attributed to him”
Staff Testimony Reveals Process Gaps:
- Former White House Staff Secretary Neera Tanden testified she “didn’t know what happened to the decision book between when she gave the materials to the Oval Office operations team and received it back with Biden’s signature”- Multiple staffers couldn’t identify who was approving or controlling auto-pen use- Several key witnesses invoked the Fifth Amendment when questioned about Biden’s health, cognitive decline, and auto-pen authorization
The Scale of Auto-Pen Usage:
- Biden issued pardons and commutations to 4,245 people—more than any other president- Preemptive pardons for Trump critics and family members- Executive orders and presidential memoranda- Federal judge appointments and policy decisions
The Committee’s Conclusion
The House Oversight Committee declared all Biden executive actions signed via auto-pen “void” without “proper, corresponding, contemporaneous, written approval traceable to the president’s own consent.”
Chairman James Comer characterized it as “one of the biggest political scandals in U.S. history,” alleging that “Biden’s top aides concealed his decline, exercised presidential authority without him, and misled the American people.”
Biden’s Defense: “I Made Every Decision”
In a rare interview with The New York Times, Biden defended his auto-pen usage: “I made every decision. We’re talking about a whole lot of people.” He explained that the volume of clemency requests necessitated auto-pen use.
Emails obtained by the Times showed that after Biden met with senior aides on January 19, 2025 (the day before Trump’s inauguration), Chief of Staff Jeff Zients emailed: “I approve the use of the autopen for the execution of all of the following pardons.”
Biden maintained: “I made every single one of those. I understand why Trump would think that, because obviously, I guess, he doesn’t focus much.”
The Legal and Technical Questions
Presidential Memorandum (June 4, 2025): President Trump ordered an investigation into Biden’s auto-pen use, directing the White House Counsel and Attorney General to investigate:
- Which policy documents used auto-pen (clemency grants, executive orders, presidential memoranda)- Who directed that the President’s signature be affixed- Whether Biden’s aides “secretly used the mechanical signature pen to conceal his incapacity”
The Legal Precedent: A 2005 Office of Legal Counsel memo states that the president “need not personally perform the physical act of affixing his signature to a bill he approves and decides to sign in order for the bill to become law.” However, this memo assumes the president actually approves the document.
Trump’s Own Auto-Pen Use: Trump acknowledged using auto-pen for “very unimportant papers,” such as responses to letters, while claiming he gets “thousands of letters a week” making manual signing impractical.
The Investigative Status
As of November 2025, the White House Counsel’s Office is leading the investigation in coordination with the Justice Department:
- More than 27,000 records obtained from the National Archives and Records Administration (NARA)- Transcribed interviews with 14 former senior Biden aides- Dr. Kevin O’Connor (Biden’s presidential physician) invoked the Fifth Amendment at his deposition- Additional senior aides scheduled for interviews in coming weeks
The Insider Threat Framework: Why Signature Authority Matters
Understanding Signature-Based Insider Threats
Traditional insider threat programs focus on data exfiltration, unauthorized access, and malicious code insertion. But the Linda Sun and Biden auto-pen cases expose a critical blind spot: the abuse of signature authority as a vector for exercising unauthorized power.
This attack vector is particularly dangerous because:
- Signature authority is inherently trusted - Organizations assume authorized signatories will act within their scope2. Detection requires human verification - Unlike database queries or network traffic, signature authenticity often requires forensic handwriting analysis3. The damage is immediate and irreversible - Once a document is signed and executed, it creates legal obligations and policy changes4. Attribution is deliberately obscured - Both forgery and auto-pen abuse make it difficult to determine who actually authorized an action
The Three Categories of Signature-Based Insider Threats
Category 1: Direct Forgery (The Linda Sun Model)
Characteristics:
- Insider manually replicates a legitimate signature- Creates fraudulent documents that appear authentic- Exploits physical access to signature templates or reference documents- Often involves state-sponsored or organized crime backing
Warning Signs:
- Signatures with unusual characteristics (too loopy, wrong letter formation)- Documents signed outside normal workflow processes- Multiple signatures from the same time period showing inconsistencies- Insider has access to genuine signature samples
Detection Methods:
- Forensic handwriting analysis- Comparison against known genuine signatures- Workflow auditing to identify documents that bypassed normal approval chains- Staff testimony from those familiar with the legitimate signature
Category 2: Unauthorized Technology Use (The Auto-Pen Model)
Characteristics:
- Legitimate signature technology used without proper authorization- Obscures who actually approved the action- Creates plausible deniability about decision-making- May indicate incapacity, delegation, or usurpation of authority
Warning Signs:
- Dramatic increase in auto-pen usage without clear policy justification- Staff confusion about approval processes- Lack of contemporaneous documentation of actual authorization- Resistance to questions about who directed signature application
Detection Methods:
- Audit trails linking auto-pen activation to specific individuals- Email records showing authorization chains (or lack thereof)- Staff interviews about decision-making processes- Comparison of auto-pen usage rates across time periods
Category 3: Digital Signature Compromise
Characteristics:
- Theft or unauthorized use of digital certificates- Compromise of private keys used for electronic signatures- Man-in-the-middle attacks on signature workflows- Insider access to signature tokens or hardware security modules
Warning Signs:
- Digital signatures verified but not recognized by the purported signer- Signatures applied from unusual locations or devices- Certificate usage outside normal business hours- Multiple signatures generated in impossibly short timeframes
Comparative Analysis: The Common Patterns
What Linda Sun and the Biden Auto-Pen Cases Share
Despite their surface differences—one involving a Chinese spy forging signatures, the other involving White House staff using legitimate technology—these cases reveal common insider threat patterns:
1. Legitimate Access as Cover
- Sun: Held senior government positions giving her document creation authority- Biden staff: Had legal access to auto-pen technology and presidential materials
2. Exploitation of Trust Relationships
- Sun: Leveraged her role as Asian-American community liaison- Biden staff: Operated within the “Executive Office operations team” with presumed authorization
3. Obscured Chain of Command
- Sun: Created documents that appeared to be legitimately signed by Hochul- Biden staff: Generated signatures without clear documentation of presidential approval
4. Systemic Nature Over Time
- Sun: Forged signatures “several times” in 2018 and maintained influence operations until 2023- Biden staff: “Vast majority” of executive actions in latter part of presidency used auto-pen
5. Detection Through Human Verification
- Sun: Former chief of staff identified forgeries through handwriting analysis- Biden staff: Staffers testifying revealed confusion about approval processes
6. Questions of Foreign Influence
- Sun: Directly working for Chinese government interests- Biden investigation: Raises questions about who actually controlled executive authority
The National Security Implications
Both cases demonstrate how signature authority abuse can:
Compromise National Security:
- Sun facilitated Chinese intelligence operations and censored discussion of human rights abuses- Auto-pen controversy raises questions about who controlled pardons, executive orders affecting military and intelligence policy
Undermine Government Legitimacy:
- Citizens must trust that executive actions reflect actual executive decisions- When that trust erodes, it damages democratic institutions
Enable Foreign Influence:
- Sun’s case shows how insiders can literally sign documents beneficial to foreign powers- Auto-pen questions: who was actually directing policy if not the president?
Create Legal Uncertainty:
- House Oversight Committee deems auto-pen-signed actions “void”- Questions about enforceability of executive actions and pardons
The Broader Insider Threat Landscape: Lessons from Recent Cases
State-Sponsored Research Theft: The Dr. Yunhai Li Case
The July 2025 arrest of Dr. Yunhai Li at Houston’s Bush Airport demonstrates another dimension of signature-based insider threats. Li attempted to board a flight to China with 90 gigabytes of stolen breast cancer vaccine research from MD Anderson Cancer Center.
Signature Authority Connection: Li maintained legitimate employment at a Chinese institution while working on U.S. defense-funded research, signing documents and agreements that gave him authorized access. His case shows how legitimate credentials and signature authority create perfect cover for espionage.
Military Espionage: The Systematic Compromise
The FBI opens a new China-related counterintelligence case every 10 hours. Recent cases include:
- Two U.S. Navy sailors providing sensitive military information to China- Air National Guard member Jack Teixeira leaking classified information- Pentagon employee Gokhan Gun charged with transmitting classified information
Each case involved insiders with legitimate access who abused signature authority, security clearances, or trusted positions.
Corporate Espionage: Google’s Contractor Breach
In October 2025, Google discovered a contractor had exfiltrated nearly 2,000 screenshots of sensitive Play Store infrastructure. The case of former Google engineer Linwei Ding—who stole AI infrastructure secrets while simultaneously working for Chinese AI companies—demonstrates how legitimate employment creates signature authority for accessing sensitive systems.
The Jack Teixeira Discord Leaks
Air National Guard member Jack Teixeira’s leak of classified documents via Discord represents a different type of insider threat, but signature authority played a critical role: Teixeira had legitimate security clearance and access credentials that were never revoked despite behavioral red flags.
Technical Deep Dive: How Signature Forgery Works
Traditional Handwritten Signature Forgery
Types of Forgery:
- Blind Forgery - No access to real signature; just guessing2. Traced Forgery - Tracing over authentic signature (Sun’s likely method)3. Free-hand Simulation - Studying and practicing the signature4. Digital Copy-Paste - Using Photoshop to copy legitimate signatures onto documents
Detection Techniques:
- Pressure analysis (traced forgeries show heavy, unnatural lines)- Flow analysis (forgeries lack the natural fluidity of practiced signatures)- Consistency comparison (forgers inadvertently include elements of their own signature style)- Microscopic examination for tool marks
Digital Signature and Auto-Pen Technology
How Auto-Pen Works: Modern auto-pen systems (like those from Automated Signature Technology or The Autopen Company):
- Store signatures on smart cards or USB flash drives- Write at human speed to create realistic reproductions- Can use any writing instrument (ballpoint pen, fountain pen, etc.)- Cost between $5,000-$20,000 for government-grade machines
Auto-Pen Vulnerabilities:
- Who controls the signature file storage?- Who authorizes each signature application?- How is the authorization documented?- What audit trail exists?
Digital Signature Security: Legitimate digital signatures use:
- Public Key Infrastructure (PKI)- Cryptographic algorithms (AES-256 for encryption, ECDSA for signatures)- Multi-factor authentication- Biometric verification- Tamper-evident certificates
Digital Signature Attacks:
- Certificate compromise through hacking or insider access- Private key theft- Man-in-the-middle attacks during signing workflow- Fake e-signature platforms designed to capture credentials
Prevention and Detection: Building Robust Controls
For Government Organizations
1. Signature Authority Frameworks
Implement clear policies defining:
- Who may sign on behalf of executives- Under what circumstances- Required contemporaneous documentation- Audit requirements
Example Policy Elements:
- All documents signed via auto-pen must be pre-approved in writing
- Approval email must specify: document title, purpose, approval date
- Auto-pen operator must be different from approval authority
- Weekly audit of all auto-pen usage submitted to ethics officer
- Quarterly forensic review of signature consistency
2. Technical Controls
- Digital signature platforms with multi-factor authentication- Blockchain-based signature verification creating immutable audit trails- AI-powered signature analysis detecting anomalies in real-time- Access controls preventing single-person signature application
3. Process Controls
- Segregation of duties - Document creator ≠ signer ≠ auto-pen operator- Mandatory rotation - No single person controls signature processes indefinitely- Escalation workflows - High-value documents require multiple approvals- Random audits - Forensic verification of signature authenticity
For Private Sector Organizations
1. Insider Threat Program Integration
Your insider threat program should specifically monitor for:
Signature Authority Red Flags:
- Employees with both document creation AND signature authority- Unusual volumes of signed documents from single individuals- Signatures applied outside normal business hours- Documents missing normal approval workflow artifacts
Behavioral Indicators:
- Unexplained wealth (Sun’s Ferrari, mansions, luxury goods)- Undisclosed foreign contacts or travel- Foreign financial interests or employment- Resistance to signature verification procedures
Technical Indicators:
- Access to signature templates or reference documents- Multiple failed attempts to replicate signatures- Unusual interest in signature authentication processes- Access to auto-pen devices outside normal duties
2. Document Workflow Security
Implement systems that:
- Track every document from creation through signature- Require contemporaneous approval documentation- Generate automated alerts for workflow deviations- Maintain immutable audit logs
3. Training and Awareness
For Executives:
- Your signature represents legal authority—guard it like your private keys- Understand who has access to signature technology or samples- Review signature audit reports regularly- Report suspicious document requests immediately
For Staff:
- Recognize social engineering tactics around signature requests- Report pressure to bypass signature verification procedures- Understand the legal implications of forged or unauthorized signatures- Know how to verify signature authenticity
4. Vendor and Contractor Management
The Google contractor breach demonstrates the risks of third-party signature authority:
- Contractors should NEVER have direct signature authority- Limit contractor access to document templates- Separate contractor networks from signature authentication systems- Conduct background checks on anyone with signature-adjacent access
For Security Professionals
Building a Signature Security Program:
Phase 1: Discovery (Weeks 1-4)
- Inventory all signature authorities across the organization- Map document workflows from creation to signature- Identify all auto-pen, digital signature, and signature template systems- Interview executives about signature delegation practices
Phase 2: Risk Assessment (Weeks 5-8)
- Evaluate current signature verification procedures- Test signature forgery detection capabilities- Review access controls for signature systems- Analyze audit trail completeness
Phase 3: Control Implementation (Months 3-6)
- Deploy technical controls (MFA, audit logging, anomaly detection)- Establish process controls (segregation of duties, approval workflows)- Implement monitoring and alerting- Train staff on new procedures
Phase 4: Continuous Monitoring (Ongoing)
- Monthly signature audit reports- Quarterly forensic verification of high-value signatures- Annual penetration testing of signature workflows- Continuous behavioral monitoring for red flags
Legal and Compliance Considerations
U.S. Legal Framework for Electronic Signatures
ESIGN Act (Electronic Signatures in Global and National Commerce Act):
- Electronic signatures have the same legal standing as handwritten signatures- Requires signer intent and consent- Must be attributable to the person who signed- Record retention requirements
UETA (Uniform Electronic Transactions Act):
- Adopted by 47 states (plus DC and US Virgin Islands)- Electronic signature = “electronic sound, symbol, or process attached to or logically associated with a record and executed or adopted by a person with the intent to sign the record”- Intent is critical—unauthorized signature lacks intent
Criminal Penalties for Signature Forgery
Federal Crimes:
- 18 U.S.C. § 495 - Forgery of government signatures: up to 10 years- 18 U.S.C. § 1001 - False statements: up to 5 years- 18 U.S.C. § 371 - Conspiracy: up to 5 years- Foreign Agents Registration Act violations: up to 5 years
State Crimes (varies by jurisdiction):
- Forgery: typically 2-10 years- Identity theft: 1-5 years- Fraud: varies by amount involved
Linda Sun’s Charges:
- Violation of Foreign Agents Registration Act- Visa fraud- Alien smuggling- Money laundering conspiracy- Bribery- Wire fraud
Civil Liability
Organizations facing signature forgery may pursue:
- Breach of fiduciary duty claims- Fraud and misrepresentation- Conversion of corporate opportunities- Trade secret theft- Breach of employment contract
Damages can include:
- Actual losses from forged documents- Costs of forensic investigation- Legal fees and litigation costs- Reputational harm- Regulatory fines
Future Threats: Where Signature Security Is Headed
AI-Powered Signature Forgery
Emerging threats include:
Generative AI Signature Creation:
- AI models trained on signature samples can generate perfect forgeries- Deep learning systems analyze pressure, speed, and stroke patterns- Automated forgery at scale becomes possible
Deepfake Document Creation:
- AI-generated “authentic” documents complete with forged signatures- Video conferencing hijacking to capture signature motion for replication- Voice synthesis combined with signature forgery for multi-factor fraud
Quantum Computing Threats to Digital Signatures
Current digital signature algorithms (RSA, ECDSA) will be vulnerable to quantum computers:
- Shor’s algorithm can break RSA encryption- Timeline: 10-20 years until quantum computers reach this capability- Organizations must begin transitioning to quantum-resistant signatures now
Post-Quantum Signature Algorithms:
- NIST has standardized quantum-resistant algorithms (CRYSTALS-Dilithium, Falcon, SPHINCS+)- Organizations should begin planning migration now- Hybrid approaches use both classical and quantum-resistant algorithms
Biometric Signature Authentication
Future signature systems may incorporate:
- Continuous authentication through keystroke dynamics- Behavioral biometrics analyzing signature motion- Multi-modal authentication (fingerprint + signature + voice)- Blockchain-based immutable signature records
Recommended Actions for CISOs and Security Leaders
Immediate Actions (This Week)
- Conduct signature authority inventory
- Who in your organization can sign on behalf of executives?- What systems contain signature templates or auto-pen functionality?- Are there clear policies governing signature delegation?2. Review recent high-value signatures
- Spot-check contracts, financial documents, policy approvals from past 90 days- Verify workflow compliance- Look for anomalies3. Brief executive team
- Share Linda Sun and Biden auto-pen cases- Explain signature authority as insider threat vector- Get buy-in for enhanced controls
Short-Term Actions (This Month)
- Implement basic technical controls
- Multi-factor authentication for digital signature systems- Audit logging for all signature application- Access reviews for signature-related systems2. Establish approval workflows
- Written pre-approval required for high-value signatures- Segregation of duties (creator ≠ signer)- Contemporaneous documentation requirements3. Begin staff training
- Awareness of signature forgery risks- Reporting procedures for suspicious requests- Verification procedures before applying signatures
Medium-Term Actions (This Quarter)
- Deploy advanced monitoring
- AI-powered signature analysis systems- Behavioral analytics for signature authority users- Integration with insider threat program2. Conduct forensic signature audit
- Hire handwriting experts to verify key signatures- Compare auto-pen usage patterns over time- Identify workflow deviations3. Update policies and procedures
- Clear signature authority matrix- Auto-pen usage policies- Incident response procedures for suspected forgery
Long-Term Actions (This Year)
- Migrate to modern signature infrastructure
- Blockchain-based signature verification- Quantum-resistant digital signature algorithms- Biometric authentication integration2. Establish signature security program
- Dedicated role or team responsible for signature integrity- Regular audits and penetration testing- Integration with enterprise risk management3. Build organizational resilience
- Cross-train staff to reduce single points of failure- Mandatory rotation for signature authority roles- Culture of verification and accountability
Conclusion: The Signature Scandal We Can’t Ignore
The revelation that Linda Sun forged Governor Kathy Hochul’s signature to facilitate Chinese Communist Party operations should be a national security wake-up call. Combined with the ongoing House Oversight Committee investigation into Biden administration auto-pen usage, these cases expose a critical blind spot in modern cybersecurity:
We’ve spent billions on network security, endpoint protection, and threat intelligence—while leaving the fundamental mechanism of executive authority largely unmonitored and unprotected.
This is not a partisan issue. It’s not about Republicans vs. Democrats or American politics vs. foreign espionage. It’s about a systematic vulnerability that transcends individual cases:
When insiders can exercise executive authority through forged or unauthorized signatures, they can:
- Execute legally binding documents- Authorize financial transactions- Grant security clearances- Issue pardons- Approve classified operations- Facilitate foreign influence- Undermine democratic processes
The Linda Sun case demonstrates how a single insider with signature access can operate for years on behalf of a foreign power. The Biden auto-pen investigation raises fundamental questions about who actually controlled executive authority during the latter part of a presidency.
The Path Forward
Security professionals must recognize signature authority as a critical insider threat vector requiring:
Technical controls (MFA, audit logging, AI-powered verification) Process controls (segregation of duties, approval workflows, mandatory documentation) People controls (training, awareness, behavioral monitoring) Governance (clear policies, regular audits, executive accountability)
The signature scandals of 2025 will either serve as a wake-up call driving meaningful security improvements—or as the first chapter in a much longer story of insider threats exploiting signature authority to exercise unauthorized power.
The question isn’t whether your organization is vulnerable to signature-based insider threats.
The question is: Who can sign your name, and how would you know if they did?
Additional Resources
Related Articles from CISO Marketplace:
- The Growing Insider Threat: How U.S. Military and Intelligence Personnel Are Being Recruited as Spies- The Perfect Insider Threat: How a State-Sponsored Researcher Nearly Smuggled 90GB of Cancer Research to China- Google Contractor Security Breach: A Deep Dive into Insider Threats and Stolen Intellectual Property- National Guard Under Siege: A Comprehensive Analysis of Cybersecurity Breaches and Insider Threats- DOGE SSA Data Security Breach: A Case Study in Government Contractor Access and Insider Threats
Tools and Resources:
- Insider Threat Risk Profiler - Quantify your organization’s insider threat risks- CISO Marketplace Vendor Risk Management Platform- Security Assessment Tools and Frameworks
Industry Standards:
- NIST SP 800-53: Security and Privacy Controls- ISO/IEC 27001: Information Security Management- CISA Insider Threat Mitigation Guide- NIST Cybersecurity Framework
Disclaimer: This article is for informational and educational purposes only. It does not constitute legal advice. Organizations should consult with qualified legal counsel regarding their specific signature authentication requirements and insider threat programs.