Privacy Nightmare Hits Viral Dating Safety Platform
UPDATE - July 28, 2025: Second Breach Exposes Over One Million Private Messages
The Crisis Deepens: A More Serious Security Failure Revealed
Just days after our initial report on the Tea app’s data breach, 404 Media has uncovered a second, far more devastating security vulnerability that exposes the most intimate private conversations between users. This new breach reveals that the security failures at Tea run much deeper than initially understood, compromising not just identity verification data but the very core of user privacy that the app promised to protect.
Key Details of the Second Breach:
- Over 1 million private direct messages between users accessed by unauthorized parties- Messages as recent as last week - contradicting Tea’s claims that only “legacy” data was affected- Highly sensitive content including discussions about abortions, cheating partners, and personal crises- Easy identity unmasking - users’ real names, phone numbers, and social media handles frequently shared in messages- Ability to send push notifications to all Tea users discovered by researchers
The Content That Was Never Meant to Be Public
The exposed messages reveal the deeply personal nature of conversations users believed were private and secure. According to 404 Media’s investigation, the leaked communications include:
Medical Privacy Violations:
- Women discussing abortion procedures and reproductive health decisions- Conversations about pregnancy scares and contraception- Mental health discussions and therapy-related content
Relationship Exposures:
- Detailed accounts of cheating partners with identifying information- Plans to leave abusive relationships- Discussions about domestic violence situations
Identity Information:
- Real names, phone numbers, and addresses shared between users- Social media handles linking anonymous accounts to real identities- Workplace information and professional details
Why This Second Breach Is Far More Dangerous
While the initial breach of driver’s licenses and selfies was devastating, this second vulnerability represents a more profound violation of user trust:
Recent Data Exposure: Unlike Tea’s claims that the first breach only affected “legacy data from over two years ago,” this second breach includes messages from as recently as last week, proving that current user data remains vulnerable.
Identity Unmasking: 404 Media reports that despite Tea encouraging users to choose anonymous screennames, it was “trivial” to identify real-world identities of users based on the personal information shared in their private messages.
Ongoing Vulnerability: The fact that researchers could access current messages and even send push notifications to all users suggests that Tea’s security infrastructure remains fundamentally compromised.
Targeted Harm Potential: The combination of sensitive personal information and easily discoverable real identities creates perfect conditions for stalking, harassment, and blackmail campaigns.
UPDATE - Company Response Falls Short Again
Tea’s Contradictory Statements Raise More Questions
Tea’s response to news of the second breach continues the pattern of deflection and minimization that characterized their reaction to the first incident:
Initial Claims vs. Reality:
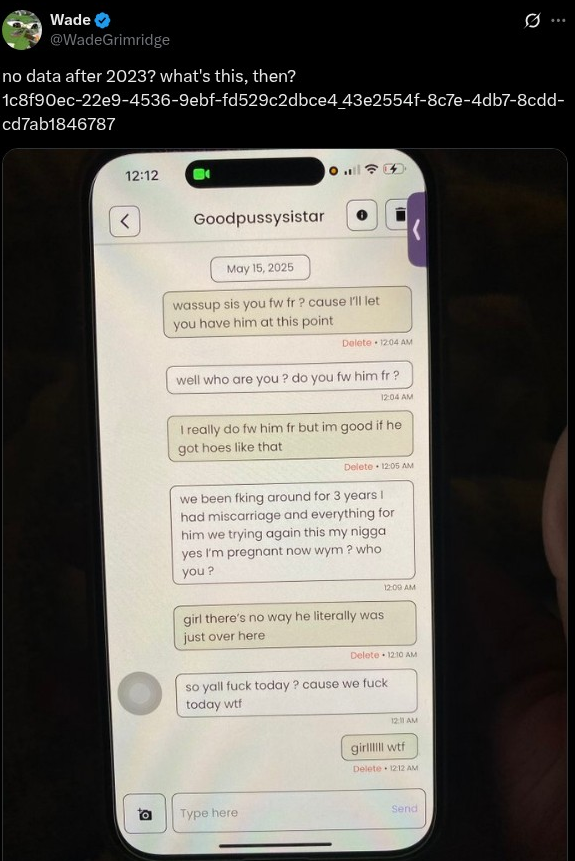
- Tea claimed: Only “legacy data from over two years ago” was affected- Reality: Messages accessed include content from as recently as last week
Data Storage Justification:
- Tea’s explanation: Data was stored “in compliance with law enforcement requirements related to cyber-bullying prevention”- The problem: No clear legal framework requires retention of private user messages for cyberbullying prevention
Security Measures:
- Tea stated: “All data has been secured” and users don’t need to change passwords- Reality: Researchers continued to access current data after this statement was made
The Pattern of Deflection
The company’s handling of both breaches reveals a concerning pattern:
- Initial Denial: Downplaying the severity and scope of data exposure2. Blame Shifting: Attributing breaches to “legacy systems” rather than current security failures3. Minimization: Claiming only “old” data was affected despite evidence to the contrary4. False Reassurance: Telling users they don’t need to take protective action when they clearly do
UPDATE - The Technical Reality: How Bad Is It Really?
Multiple Database Compromises Suggest Systemic Failure
The revelation of a second, separate database breach indicates that Tea’s security problems are not isolated incidents but reflect fundamental architectural failures:
Database Architecture Issues:
- Multiple exposed databases suggest lack of centralized security controls- Different data types (images vs. messages) stored with inadequate protection- No apparent security monitoring or intrusion detection systems
Firebase Configuration Failures:
- Google Firebase storage buckets left publicly accessible without authentication- Basic security configurations ignored during setup- No access logging or monitoring to detect unauthorized access
Development Security Gaps:
- Production systems apparently running with debugging configurations- Sensitive data stored in easily accessible formats- No encryption for data at rest in storage systems
The Researcher’s Capabilities Expose Deeper Issues
The independent security researcher who uncovered the second breach was able to:
- Access over one million private messages- Review message content in real-time- Send push notifications to all app users- Easily correlate anonymous users with real identities
These capabilities suggest that Tea’s infrastructure was not just vulnerable but essentially operating as an open database with minimal security controls.
UPDATE - User Impact Assessment: The Human Cost Multiplies
From Identity Theft to Targeted Harassment
The combination of both breaches creates unprecedented risks for Tea’s users:
Enhanced Blackmail Potential:
- Driver’s licenses + intimate messages = perfect blackmail material- Ability to identify users by real name increases targeting precision- Sensitive health information (abortion discussions) particularly valuable to bad actors
Stalking and Harassment Amplification:
- Real identities easily discovered through message content- Location information often shared in private conversations- Social media handles linking to broader online presence
Professional and Social Consequences:
- Discussions about workplace relationships and affairs- Comments about colleagues, bosses, and professional situations- Content that could destroy careers if made public
Family and Relationship Destruction:
- Detailed discussions about cheating partners- Plans to leave relationships- Private concerns about family members
Vulnerable Populations at Increased Risk
Certain groups of Tea users face disproportionate harm from these combined breaches:
Domestic Violence Survivors:
- Safety plans and escape strategies potentially exposed- Communications with support services compromised- Location information that could endanger physical safety
Healthcare Workers and Public Figures:
- Professional reputations at risk from private conversations- Higher-value targets for blackmail and extortion- Greater potential for public humiliation
LGBTQ+ Users:
- Coming-out discussions and identity exploration- Information about relationships not yet public- Health discussions around transition or sexual health
UPDATE - Legal and Regulatory Implications Expand
HIPAA and Medical Privacy Concerns
The exposure of abortion-related discussions raises serious legal questions:
Potential HIPAA Violations:
- If any messages contained protected health information- Tea’s role as a potential business associate under HIPAA- State medical privacy laws that may apply
State Abortion Privacy Laws:
- In states with strict abortion laws, exposed communications could be used for prosecution- Increased danger for users in restrictive legal environments- Potential for law enforcement surveillance of reproductive health discussions
Expanded Liability Exposure
The second breach significantly increases Tea’s legal vulnerability:
Class Action Potential:
- Multiple types of sensitive data exposed across different systems- Ongoing nature of breaches suggests negligence rather than isolated incident- Enhanced damages from particularly sensitive nature of message content
Regulatory Scrutiny:
- FTC investigation likely given the scope and sensitivity of exposed data- State attorneys general inquiries expected- Potential CCPA violations in California
UPDATE - Industry Analysis: A Case Study in How Not to Build Women’s Safety Tech
The Irony of a Safety App Creating Danger
Tea’s security failures represent a devastating case study in how good intentions can create worse outcomes when coupled with poor execution:
Trust Exploitation:
- Users entrusted Tea with their most sensitive information specifically because it promised safety- The app’s women-only nature encouraged users to share more personal details- Verification requirements created a false sense of security
Amplified Harm:
- Traditional dating apps typically don’t collect driver’s licenses or intimate health discussions- Tea’s model concentrated maximum sensitive data in poorly secured systems- The anonymous nature of the platform actually makes users more vulnerable when anonymity fails
Lessons for the Safety Tech Industry
Tea’s failures offer crucial lessons for other companies building safety-focused platforms:
Security Must Match Sensitivity:
- Apps handling sensitive user data need enterprise-grade security from day one- User verification systems must be built with security-by-design principles- Regular third-party security audits are essential, not optional
Transparency Over Marketing:
- Clear communication about data storage and retention policies- Honest assessment of security capabilities rather than false reassurance- Immediate, full disclosure when breaches occur
User Agency and Control:
- Tools for users to delete their data completely- Granular privacy controls for different types of information- Clear opt-out mechanisms for data retention
UPDATE - Recommendations for Affected Users
Immediate Actions for Tea Users
Given the scope and severity of both breaches, Tea users should take immediate protective action:
Identity Protection:
- Monitor credit reports for signs of identity theft2. Place fraud alerts with credit bureaus3. Consider identity monitoring services given the exposure of driver’s license information4. Review bank and credit card statements for unauthorized activity
Digital Security:
- Change passwords on all accounts, especially those that might match your Tea login2. Enable two-factor authentication on critical accounts3. Review social media privacy settings to limit discoverability4. Consider temporarily deactivating social media accounts if harassment begins
Communication Safety:
- Alert trusted contacts about potential harassment or blackmail attempts2. Document any suspicious communications you receive3. Report harassment to law enforcement if it occurs4. Seek support from domestic violence organizations if you’re in a vulnerable situation
Legal Preparation:
- Save evidence of your Tea account and any harm you experience2. Consult with a privacy attorney if you face blackmail or harassment3. Report the incident to your state attorney general4. Join class action suits if they become available
For Healthcare-Related Exposures
Users whose messages contained healthcare information should take additional steps:
- Contact healthcare providers about potential privacy violations2. Review HIPAA rights and file complaints if applicable3. Seek legal counsel specializing in medical privacy4. Document any discrimination or harassment related to exposed health information
Looking Forward: The Broader Implications
A Watershed Moment for Women’s Safety Tech
The Tea breaches represent more than just another corporate data security failure—they mark a potential turning point in how we think about women’s safety technology:
The Trust Deficit:
- How can users trust safety apps when the biggest names fail so spectacularly?- What level of security should be required for platforms handling sensitive safety data?- How do we balance safety features with privacy protection?
The Verification Dilemma:
- Are identity verification requirements creating more risk than they prevent?- Can safety platforms function effectively without collecting sensitive identity data?- What alternatives exist to document-based identity verification?
The Regulation Question:
- Should safety-focused apps be subject to higher security standards?- What role should government play in protecting women’s safety data?- How can we ensure innovation while requiring adequate protection?
The Tea incident will likely be studied for years as an example of how well-intentioned technology can create devastating consequences when security is treated as an afterthought rather than a foundation. For the hundreds of thousands of women whose most intimate information now circulates in the digital underground, the damage is already done. The question is whether the industry will learn from this failure to build truly safe and secure platforms for women’s safety.
These updates incorporate breaking developments through July 28, 2025. The situation continues to evolve, and this article will be updated as new information becomes available.
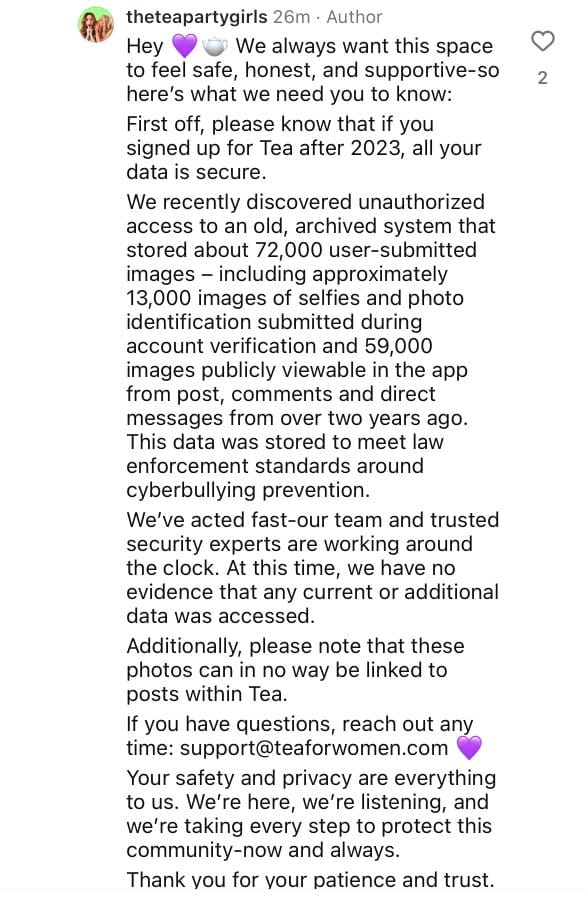
 The women-only dating safety app Tea, which rocketed to the top of Apple’s App Store charts this week, has suffered a catastrophic data breach that exposed tens of thousands of users’ driver’s licenses, selfies, and personal verification photos to users on the anonymous messaging board 4chan.
The women-only dating safety app Tea, which rocketed to the top of Apple’s App Store charts this week, has suffered a catastrophic data breach that exposed tens of thousands of users’ driver’s licenses, selfies, and personal verification photos to users on the anonymous messaging board 4chan.
What is Tea?
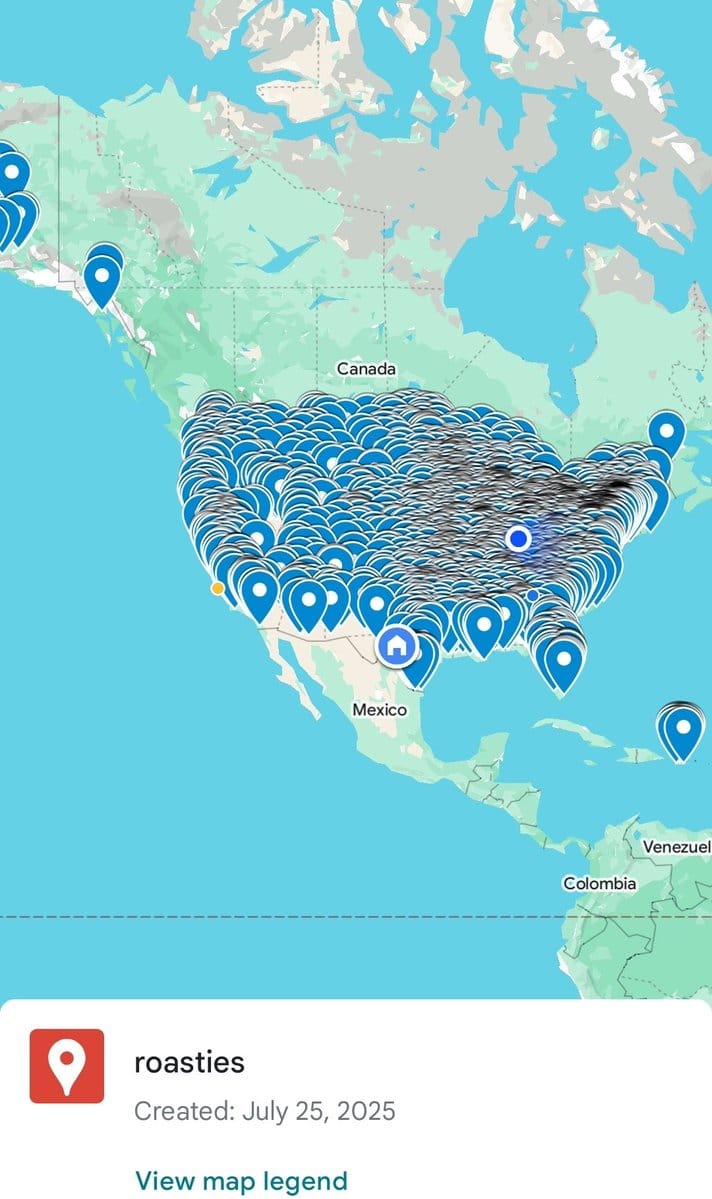
Tea is a controversial app designed exclusively for women to anonymously share experiences and warnings about men they’ve dated. The platform requires strict identity verification—users must upload both a selfie and a government-issued ID to prove they are women before gaining access to the community.
The app’s premise is simple but polarizing: women can search for men by photo and location, then view anonymous reviews and “red flags” or “green flags” posted by other users who have dated them. Think of it as a combination of Yelp and a background check service, but for romantic partners.
https://t.co/tDpKMg1qmk— vx-underground (@vxunderground) July 26, 2025
The Security Disaster
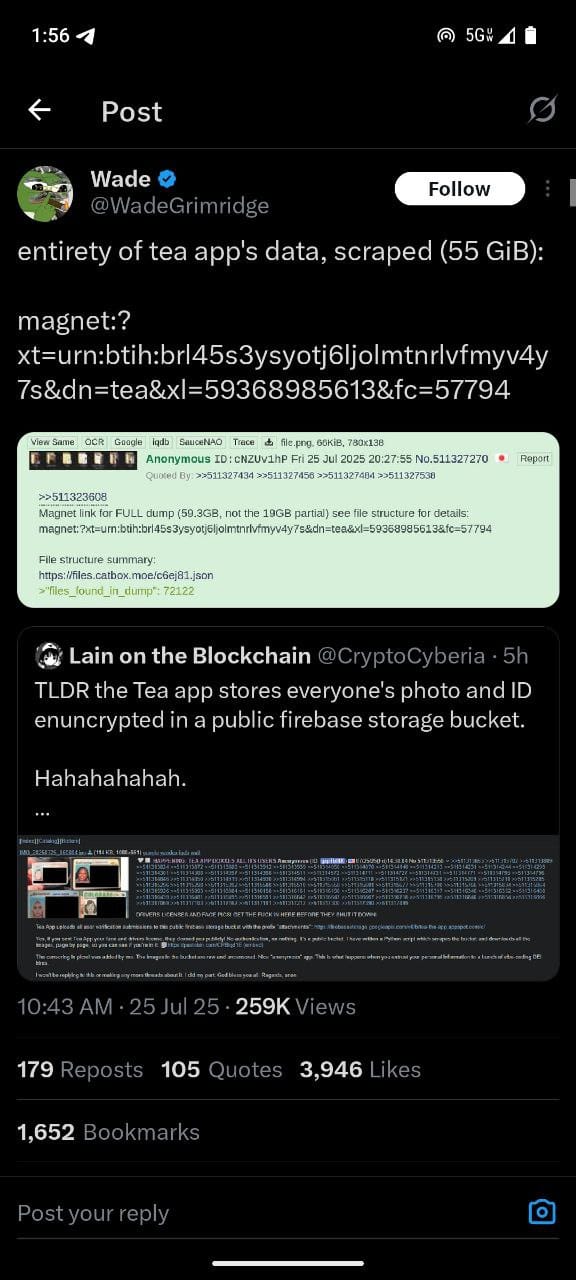
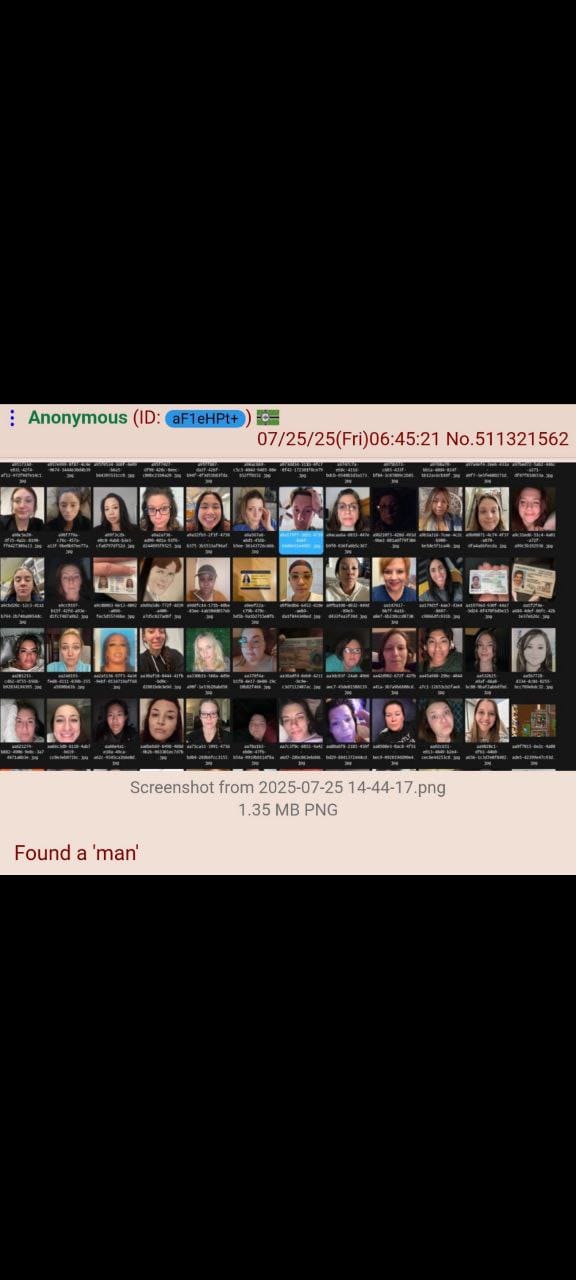
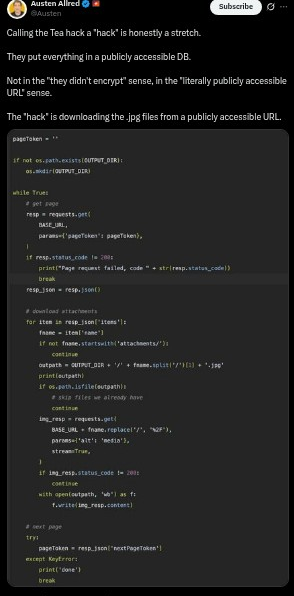
On July 25, 2025, users on 4chan discovered that Tea’s entire user database was stored in a completely unsecured Google Firebase storage bucket. No password, no authentication, no security measures whatsoever—just a public URL that anyone could access.
“Yes, if you sent Tea App your face and drivers license, they doxxed you publicly! No authentication, no nothing. It’s a public bucket,” read one 4chan post that included the vulnerable database link.
The thread, which has since been deleted, contained messages like “DRIVERS LICENSES AND FACE PICS! GET THE F*** IN HERE BEFORE THEY SHUT IT DOWN!” as users scrambled to download as much personal data as possible.
Scale of the Breach
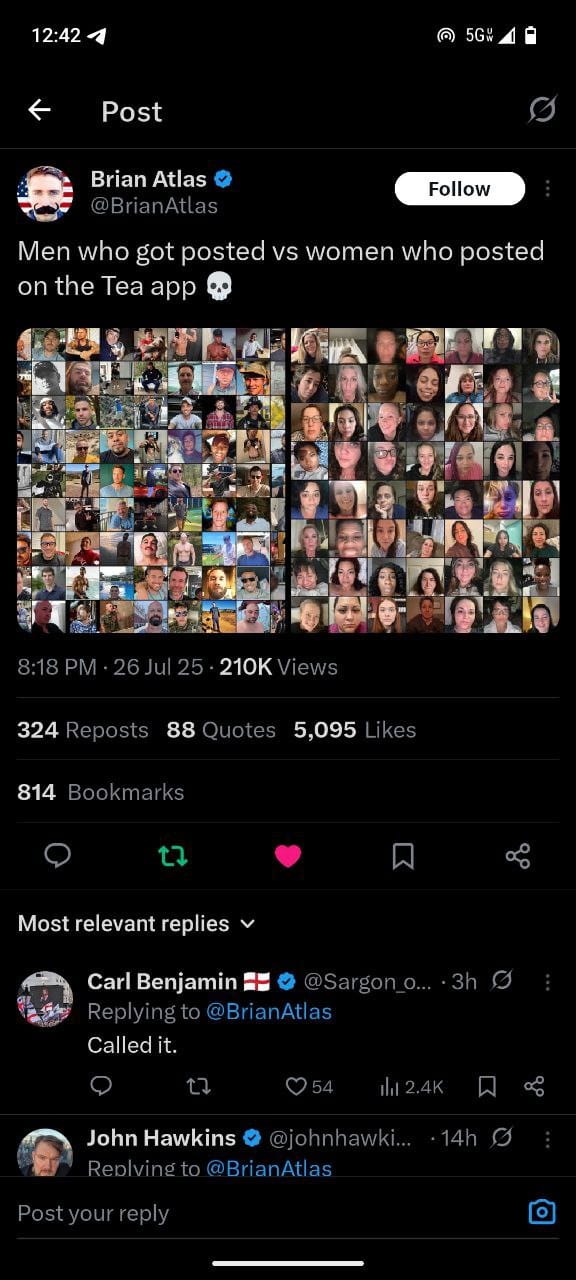
The exposed data included:
- 72,000+ user verification photos including selfies and driver’s licenses- Personal identification documents with full names, addresses, and dates of birth- Some direct messages between users- Location data tied to user profiles
4chan users created automated scripts to mass-download the exposed files, with some claiming to have collected thousands of women’s personal documents within hours of the discovery.
Company Response Falls Short
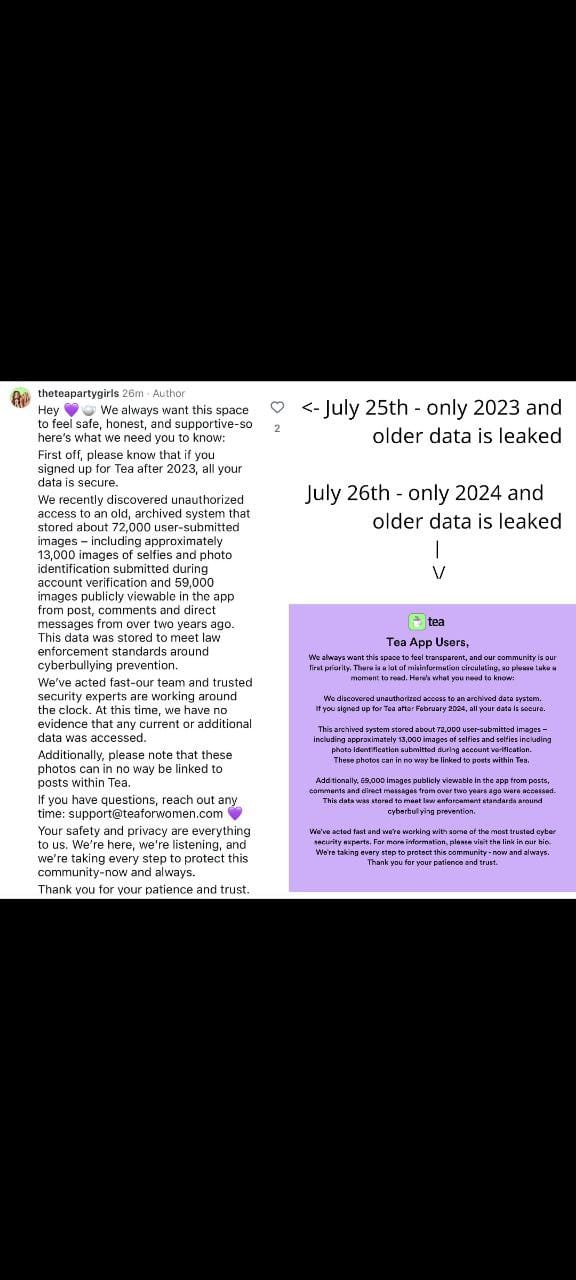
Tea’s response to the breach has been inadequate and contradictory. The company initially claimed the exposed data was “from more than two years ago” and that “no current user data is affected.”
This explanation raises serious questions, as the app only went viral and gained massive popularity this week. If the data is truly two years old, why was it still accessible? And why were recent users’ verification photos apparently included in the leak?
The company’s founder, Sean Cook, has not responded to media requests for comment, leaving users in the dark about the full scope of the breach and what steps are being taken to protect them.


The Bigger Picture
This breach highlights the dangerous intersection of good intentions and poor execution. Tea’s mission—helping women stay safe while dating—is admirable and addresses a real need. However, the app’s complete failure to secure users’ most sensitive personal information has potentially put thousands of women at greater risk.
The irony is stark: an app designed to protect women’s safety has become a tool that could facilitate stalking, harassment, or identity theft. The very women who trusted Tea with their most personal information to stay safe while dating now face the possibility of being doxxed by anonymous internet users.
Founder of Tea Dating Advice was a previously a product leader at Salesforce
Massive moment for big tech PMs
Never doubt them again pic.twitter.com/UNoSsqcRIW— Jordi Hays (@jordihays) July 23, 2025
Rule Number Two: If you are the spouse of a high-ranking Congressman, don’t take a selfie to sign up for a gossip app from inside the home of the individual you are having an affair with. https://t.co/Rljo37G8lD pic.twitter.com/YGViGLFSIl— BelowTheTearline (@BelowTearline) July 25, 2025
What Users Should Do
If you’ve used the Tea app:
- Monitor your identity - Watch for signs of identity theft or unauthorized use of your personal information2. Consider a credit freeze - Protect yourself from potential financial fraud3. Document everything - Keep records of your Tea account and any suspicious activity4. Report incidents - Contact authorities if you experience harassment or stalking that may be linked to the breach
The Cost of Poor Security
This incident serves as a cautionary tale about the importance of cybersecurity, especially for apps handling sensitive personal data. Tea’s decision to store unencrypted user verification documents in a public, unsecured database represents a fundamental failure of basic security practices.
For an app built around safety and trust, this breach may prove fatal to both its reputation and its mission. The women who needed Tea’s protection the most are now the ones most at risk from its catastrophic security failures.
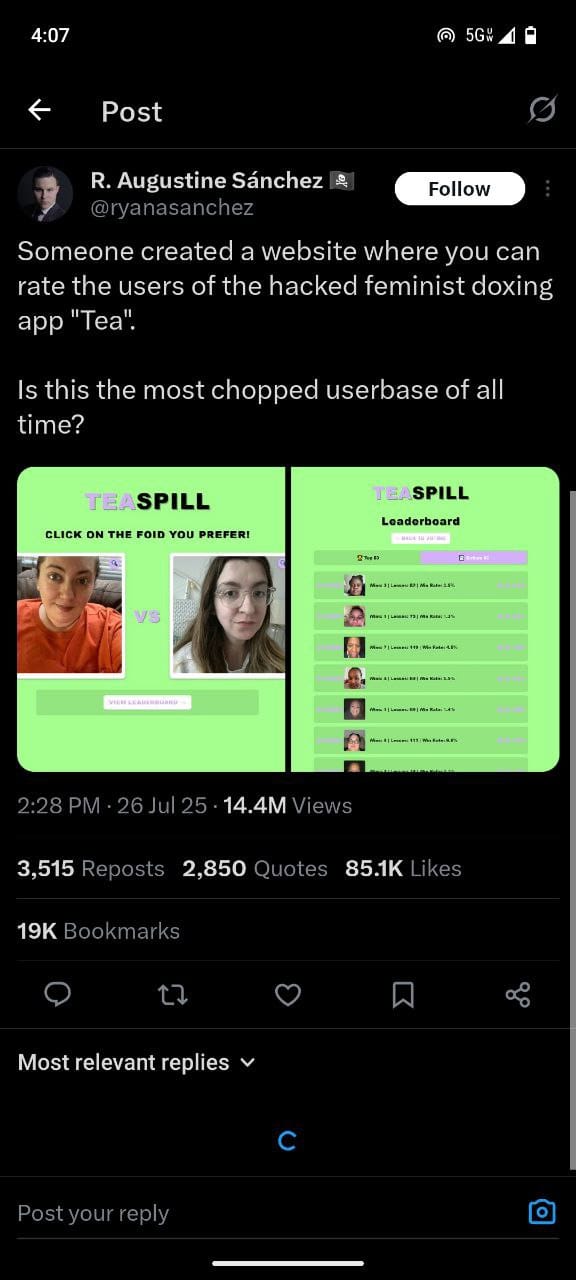
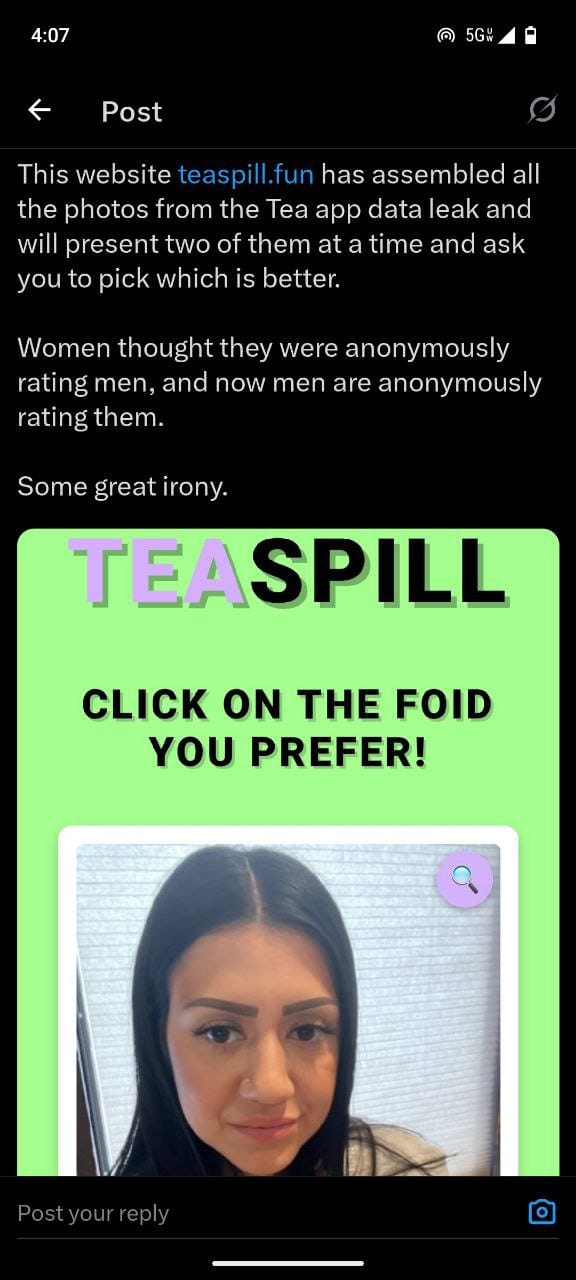
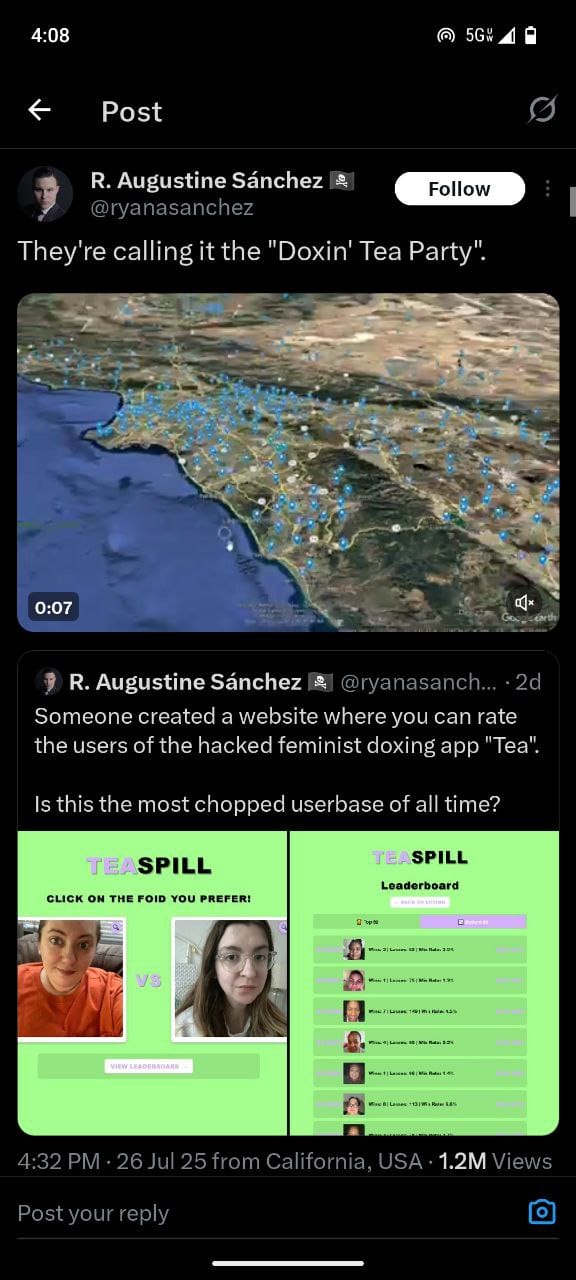
Someone created a website where you can rate the users of the hacked feminist doxing app “Tea”.
Is this the most chopped userbase of all time? pic.twitter.com/0HwSxWCMnS— R. Augustine Sánchez 🏴☠️ (@ryanasanchez) July 26, 2025
Tea’s Competitors: How Do They Stack Up on Security?
The Tea app breach highlights a critical gap in the women’s dating safety space. Here’s how Tea’s main competitors handle security and user protection:
Are We Dating The Same Guy (AWDTSG) Facebook Groups
The original inspiration for Tea came from the “Are We Dating The Same Guy?” Facebook groups, which have over 3.5 million members across 200+ individual groups worldwide. Unlike Tea’s centralized app approach, AWDTSG operates through private Facebook groups where women share dating profiles and experiences.
Dating Apps Under Siege: The Growing Hacking Epidemic Threatening Modern Romance
Security differences:
- No identity verification required - Users only need a Facebook account- Screenshots allowed - Unlike Tea’s anti-screenshot technology, Facebook groups can’t prevent image sharing- Platform liability - Facebook’s infrastructure handles data security, rather than a startup’s potentially vulnerable systems- Legal challenges - Multiple defamation lawsuits have been filed against AWDTSG groups, with one man in Los Angeles suing for $2.6 million
Noonlight: America’s #1 Safety App
Noonlight protects over 3 million users and is America’s number one safety app, with integrated compatibility with Tinder and other major dating platforms. Unlike Tea’s community-driven approach, Noonlight focuses on emergency response.
Key features:
- Emergency button technology - Users hold a button when feeling unsafe; releasing without entering a code alerts police- Professional monitoring - 24/7 help centers with trained operators screen calls and connect users with appropriate emergency services- Major platform integration - Match Group invested in Noonlight in 2020, integrating it across Tinder, Match, OkCupid, and other dating apps- No personal review system - Focuses purely on emergency response rather than crowdsourced information sharing
Other Dating Safety Apps
Kitestring: A text-based check-in service that doesn’t require app downloads - users set timers and receive SMS check-ins, with emergency contacts alerted if they don’t respond
Arlo Safe: Professional security monitoring with live, medically trained experts available 24/7
bSafe: Voice activation and live streaming capabilities for emergency situations
The Security Comparison
What makes Tea’s breach particularly damaging is how it contrasts with its competitors:
- AWDTSG groups rely on Facebook’s established infrastructure rather than building their own vulnerable systems2. Noonlight partners with major tech companies like Match Group, likely ensuring enterprise-level security standards3. Traditional safety apps focus on emergency response rather than storing sensitive identity documents
Tea’s approach of requiring driver’s licenses and ID verification created a honeypot of sensitive personal data that proved irresistible to malicious actors. In contrast, most competitors either avoid collecting such sensitive information or rely on established platforms with proven security track records.
The lesson is clear: good intentions in women’s safety technology mean nothing without proper cybersecurity infrastructure to protect the very users you’re trying to help.
This story is developing as more details about the breach continue to emerge.